
Raul Muñoz
@raulmuo16535398
Cibersecurity,Threats Intelligence Engineer, Cyber Threats.
Focusing on the problem is not the Solución.
ID: 1448063540519178241
12-10-2021 23:11:08
118 Tweet
28 Followers
499 Following








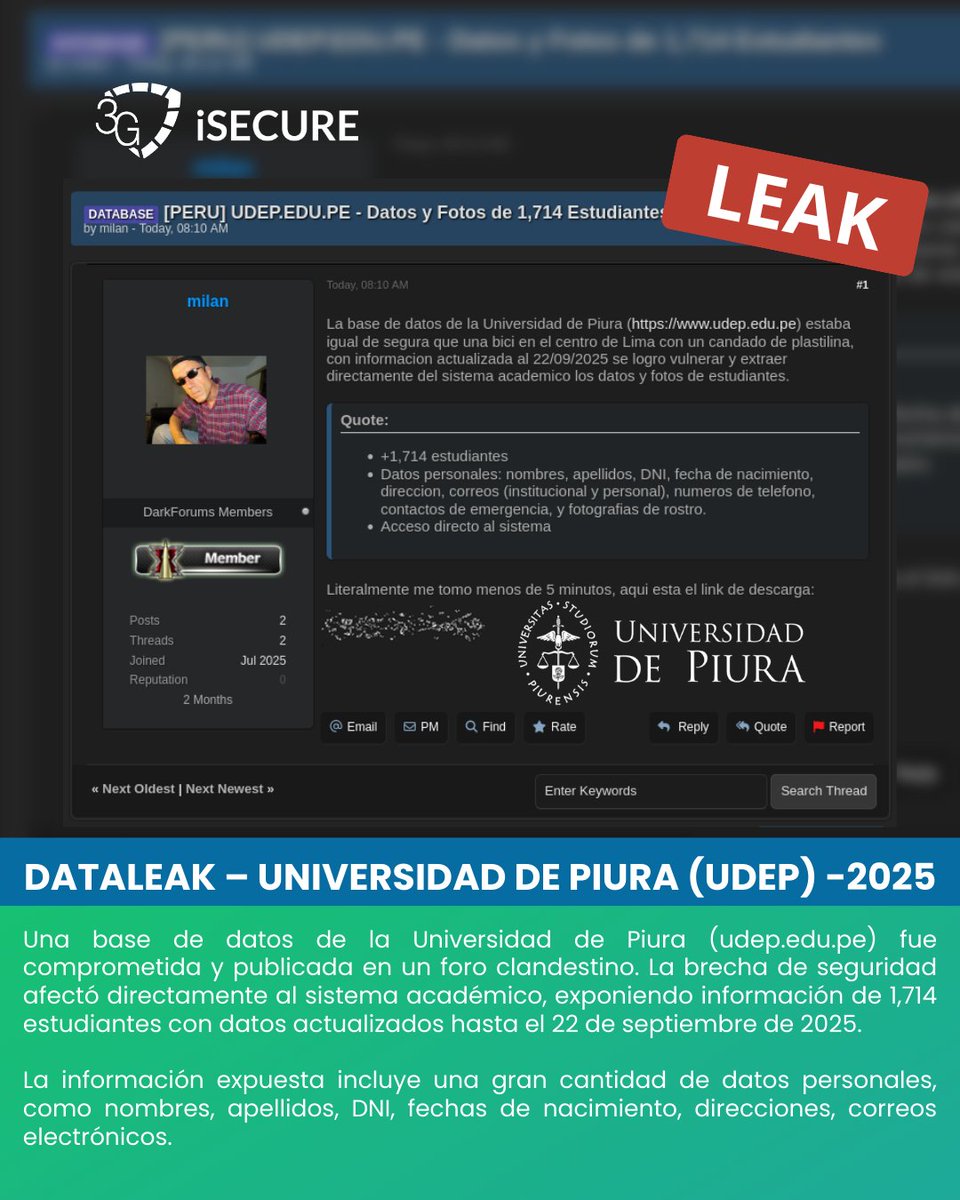
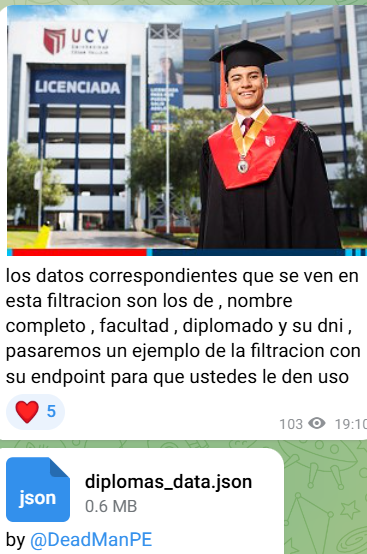
Una base de datos estudiantes de la Universidad de Piura (Universidad de Piura) fue comprometida y publicada en un foro clandestino. 📂 Data expuesta: - 1,714 estudiantes afectados - Nombres, DNI, correos, direcciones y fechas de nacimiento, fotos.







New ZuRu Malware Variant Targeting Developers via Trojanized Termius macOS App thehackernews.com/2025/07/new-ma… via The Hacker News

Hacktivists tampered with Canadian industrial systems, cyber agency warns therecord.media/canada-ics-hac… The Record From Recorded Future News










![Raul Muñoz (@raulmuo16535398) on Twitter photo A new family of Trojans with clicker functionality has emerged. They share a common characteristic: they are managed from the hxxps[:]//dllpgd[.]click server, or are loaded and executed by command from it. This type of malware infects smartphones running the Android operating.. A new family of Trojans with clicker functionality has emerged. They share a common characteristic: they are managed from the hxxps[:]//dllpgd[.]click server, or are loaded and executed by command from it. This type of malware infects smartphones running the Android operating..](https://pbs.twimg.com/media/G_pET7zXAAANdVv.png)