Rakesh Mane
@rakeshmane10
Tech. Bug Hunting. CTFs. Security Engineering.
ID: 1521519164
https://rakeshmane.com 16-06-2013 07:33:37
1,1K Tweet
3,3K Followers
1,1K Following


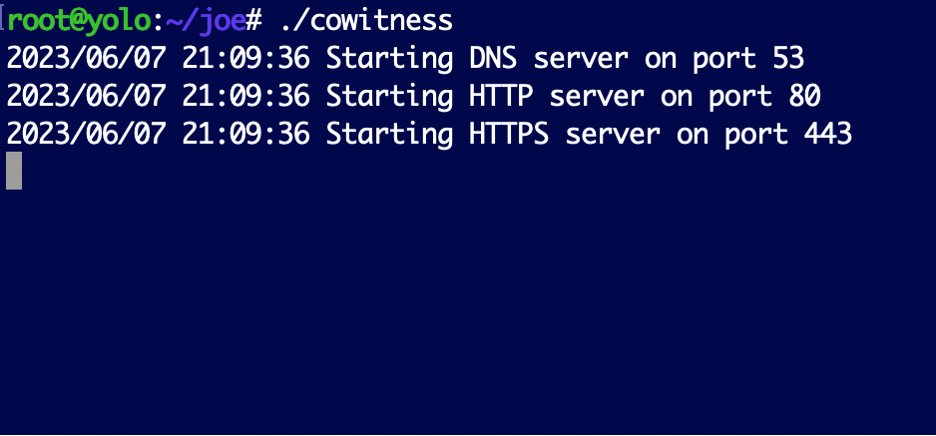
Are you a web tester who specializes in blind or out-of-band vulns? Check out CoWitness, a dope (stand alone) alternative to Collaborator by TrustedSec which adds URI and User-Agent. github.com/stolenusername… trustedsec.com/blog/introduci…



I’ve published the slides for my Security BSides Ahmedabad closing keynote: bit.ly/pwning-cloud-c… In this talk, I shared: “Lateral movement brute forcing” — a new technique that I covered and used against different targets to go, eg. From a limited GitHub token to achieve multi-lateral



🔥 OAuth "token reuse" vulnerability An interesting OAuth attack technique by Aviad Carmel that reused OAuth tokens from a different app to fully takeover victim's account in many popular apps like Grammarly salt.security/blog/oh-auth-a… #bugbountytips #bugbounty #cybersecurity



DVWA Security >>>> ICICI Bank 's Security





.Rakesh Mane solved #XSS Challenge with identical solution as "Abdul Aziz Khan", making it the shortest. For the record, the number of characters are "55". Link: xss.redseclabs.com #xss #challenge #BugBounty