Palak Sethia
@ps_doom
ID: 383583282
02-10-2011 04:23:51
307 Tweet
47 Followers
342 Following






All media channels, digital platforms and individuals are advised to refrain from live coverage or real-time reporting of defence operations and movement of security forces. Disclosure of such sensitive or source-based information may jeopardize operational effectiveness and

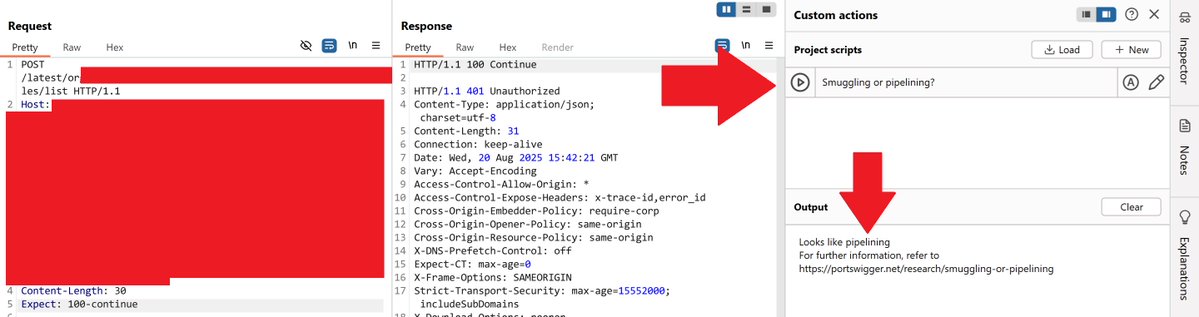
ok, so, when in doubt for http request smuggling or http pipelining, use the bambda by James Kettle github.com/PortSwigger/ba…