pickpocket team
@pickpocket001
Obsessed with Infosec
ID: 2462282971
24-04-2014 21:52:18
487 Tweet
569 Takipçi
4,4K Takip Edilen





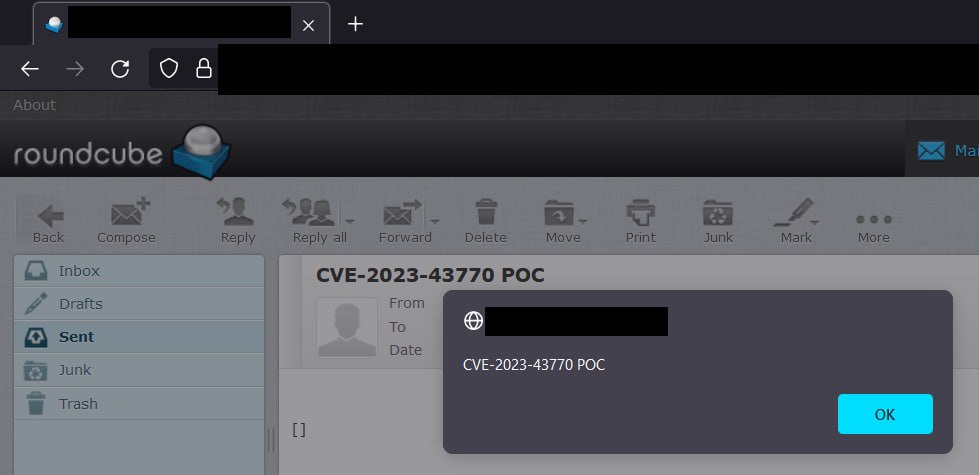
CVE-2023-43770 mail server Roundcube * usage: python cve-2023-43770.py -e [email protected] -p Attack3rPwd -t [email protected] * POC exploit github.com/s3cb0y/CVE-202… 👀 Check Out Old Tweets Of Today Cyber News #cybersecurity #BugBounty #infosec #CVE