PhysicalDrive0
@physicaldrive0
Malware Hunter / I've already taken the red pill!
ID: 218798348
23-11-2010 09:12:58
22,22K Tweet
16,16K Followers
924 Following






2019-02-08: #ExileRAT Group: "CVE-2017-8759" altered toolkit "get_robin.py" server thread w/ local logging { SHELLCODE1 = 'sc.dat' as JScript | LOG_FILE = 'robins.log' } h/t PhysicalDrive0 Original Research 👍 -> x.com/TalosSecurity/…





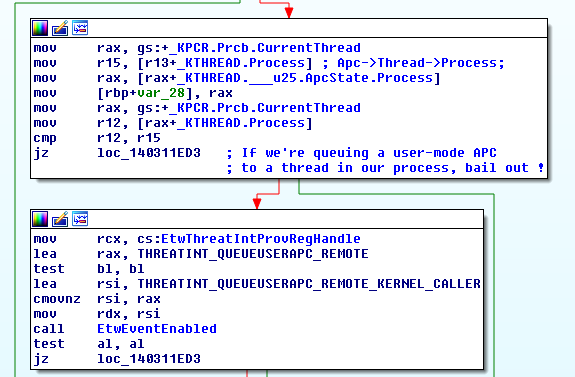
Google discovered a Chrome RCE #0day in the wild (CVE-2019-5786). Reportedly, a full chain with a sandbox escape: chromereleases.googleblog.com/2019/03/stable… In 2019, I expect epic 0days to be found in the wild: Android, iOS, Windows, Office, virtualization, and more. Stay safe and enjoy the show.