Phoenix
@phoenix244001
Web3 Security Researcher
ID: 1349816098640674816
https://pheonix244001.github.io/portfolio-website/ 14-01-2021 20:30:25
609 Tweet
673 Followers
1,1K Following


















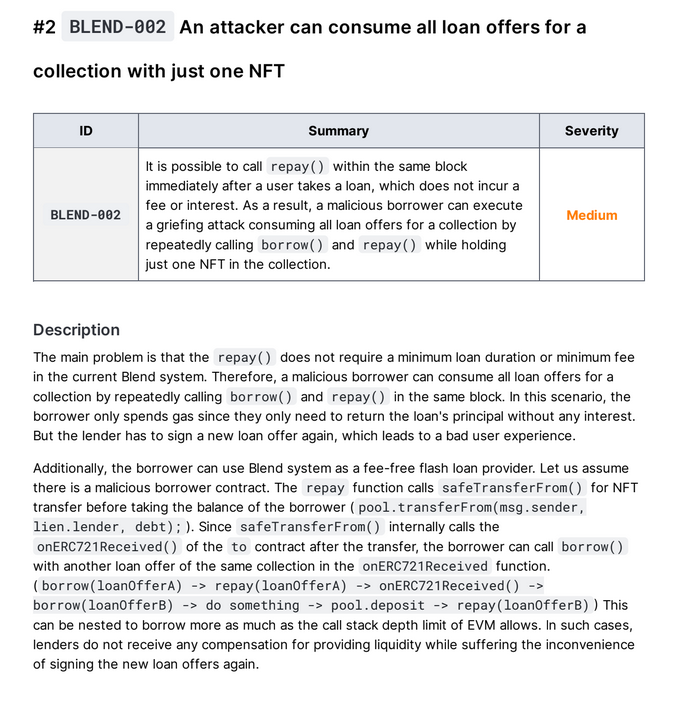
We at QuillAudits Just wrapped up one of our Audit and what a ride! 🚀 80 issues identified, including multiple criticals and some truly fascinating vulnerabilities. Massive shoutout to our auditors Cryptanu 🥷 Phoenix Rahul Saxena for delivering exceptional depth and
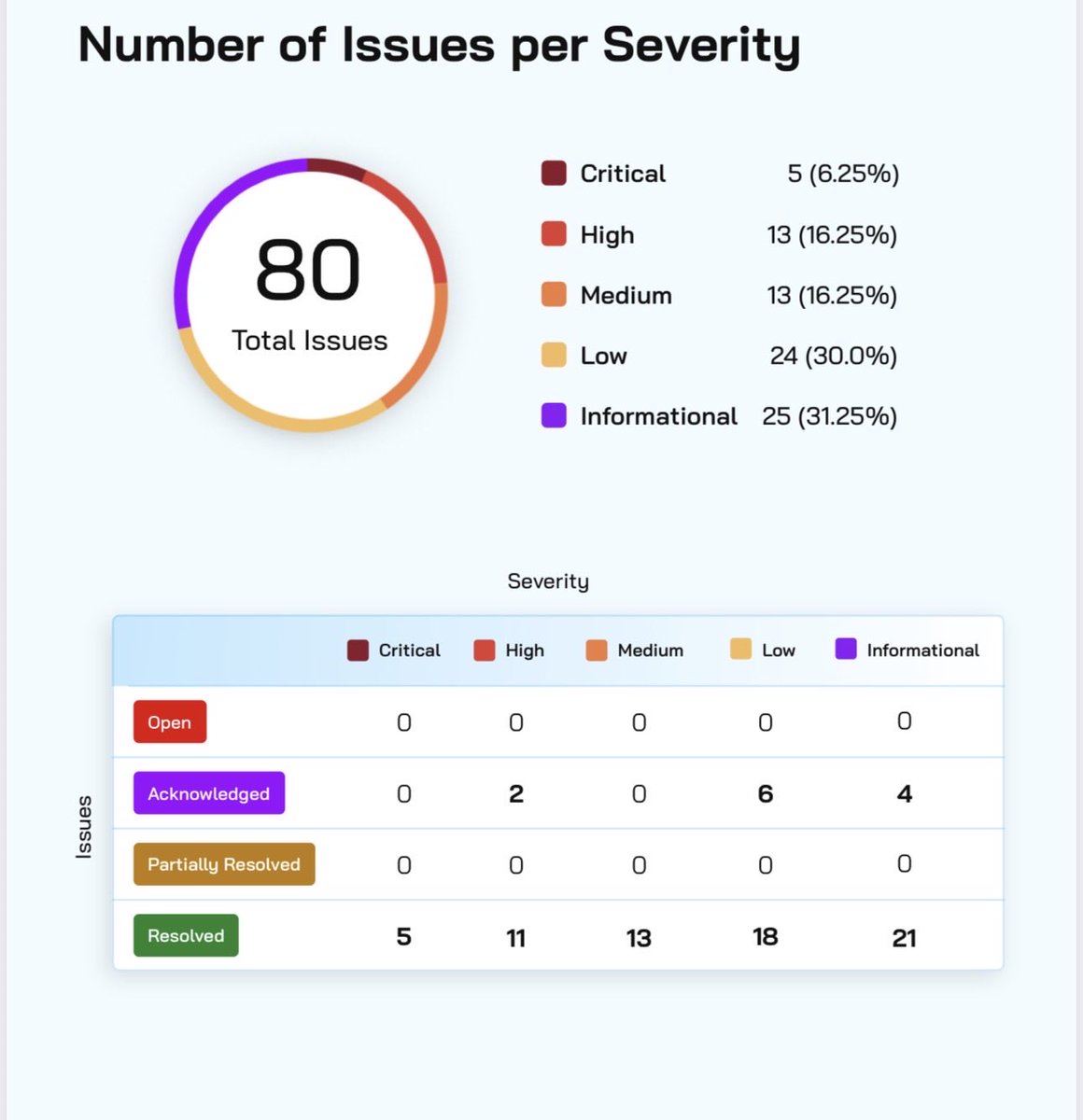

As 2025 comes to a close, what an incredible year it’s been for us QuillAudits ✈️ ConsensusHK26 ✅ 200+ audits completed 🐞 1200+ issues identified, including ~300 High & Critical findings Worked across ecosystems: Monad, Sonic, Soneium, Avalanche, Plume Chain, Scroll, Tron, Avitus, XRP,