Paul Jespersen
@pauljespersen
Cybersecurity, Startups, VC, Tech, Linguistics, History, Texas, Photography, Lacrosse, Flyfishing, Skiing, Travel. Founder @PRESecurityAI
ID: 38895729
09-05-2009 17:56:58
2,2K Tweet
173 Takipçi
829 Takip Edilen

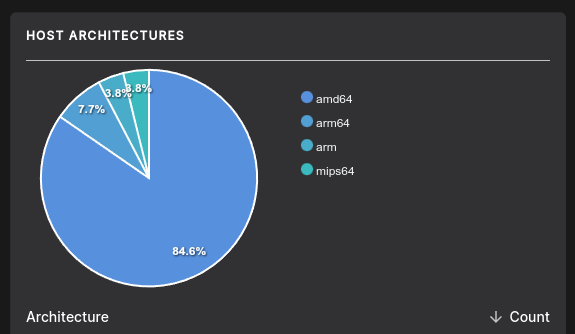
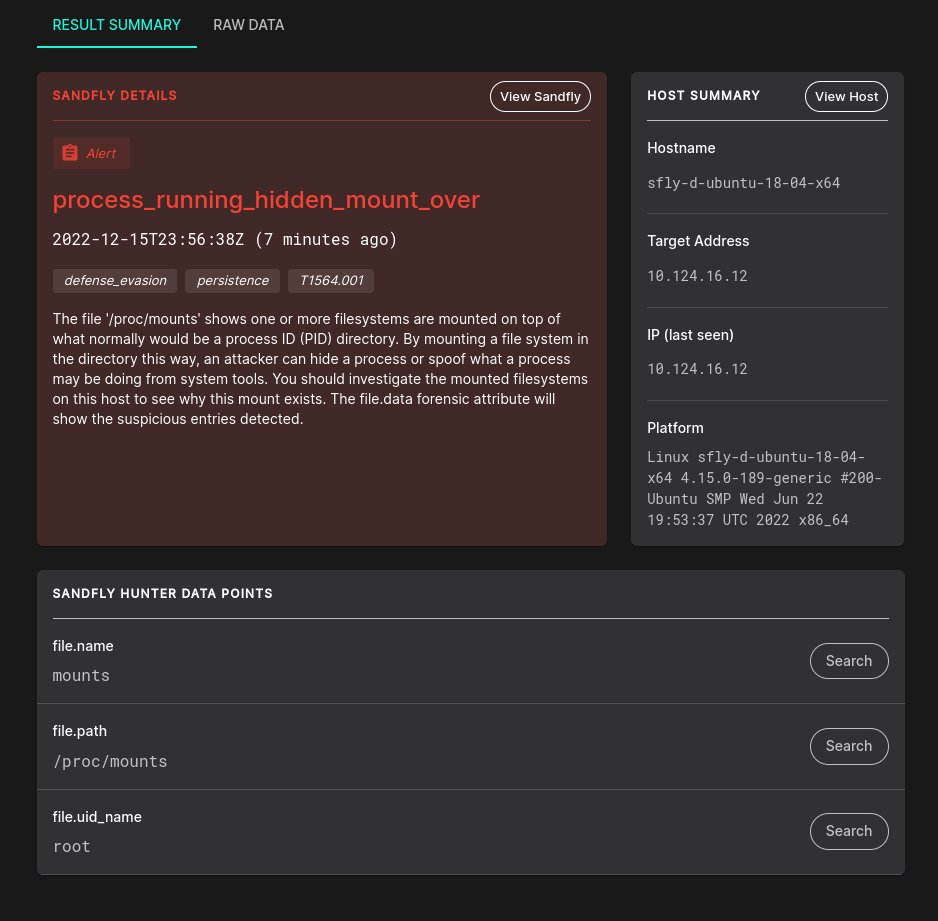
Great to be on the Sandfly Security team. Great agentless solution for Linux cybersecurity. #freemium version of our new 4.0 release available now at sandflysecurity.com











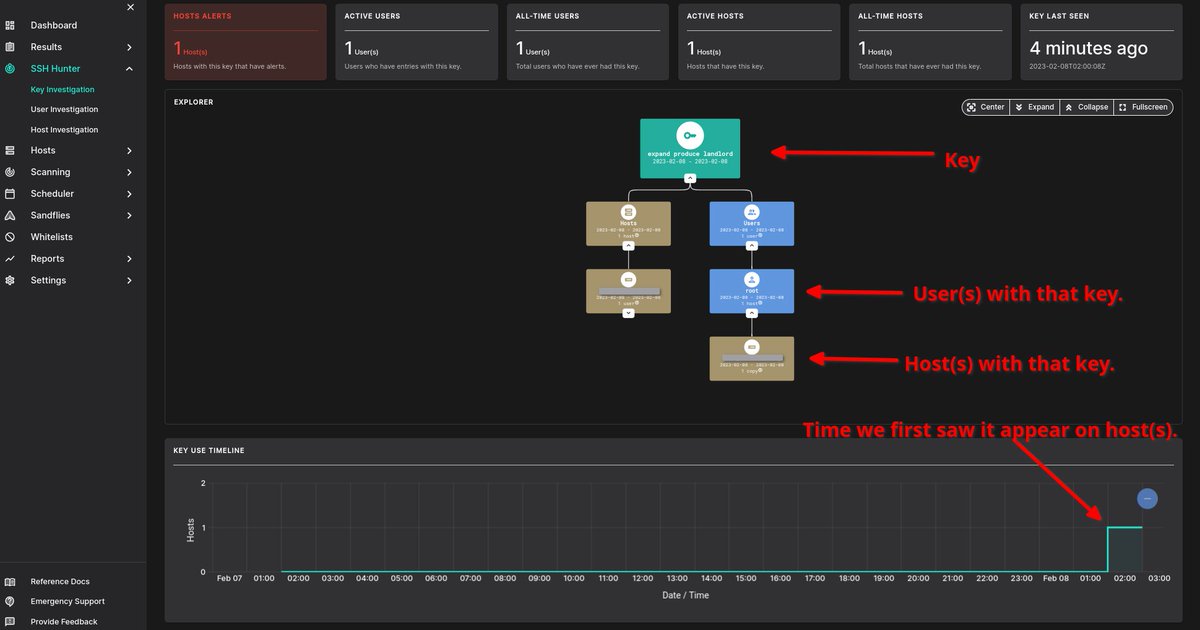
If you want to quickly find SSH keys used by this and other Linux malware, simply paste it into Sandfly Security SSH Hunter. We collect SSH public keys on all systems automatically. If you see any hosts show up, you have a problem. Easy.




Good stuff for PRE Security at RSAConference this year. prnewswire.com/news-releases/…