Patrick Biernat
@patrickbiernat
Security Researcher @ret2systems
ID: 1176686372
13-02-2013 19:57:40
161 Tweet
601 Followers
270 Following

A little month than month ago i finished the wargames challanges by RET2 Systems. Before this course i had 0 knowledge regarding low-level exploitation techniques, mitigations and bypass strategies. The course really pushes you and gives you knowledge required to break into VR💯
On the passing of our dear friend and alumni, Sophia "quend" d'Antoine (Sophia d’Antoine)











Confirmed! Jack Dates of RET2 Systems (RET2 Systems) used a single Out-of-Bounds (OOB) write to exploit the #Sonos Era 300 speaker. He earns himself $60,000 and 6 Master of Pwn points. #Pwn2Own #P2OIreland

Confirmed! Jack Dates of RET2 Systems (RET2 Systems) used an OOB Write to get a shell and a modified login page on the Synology DiskStation DS1823xs+. His second round win nets him $20,000 and 4 Master of Pwn points. #Pwn2Own #P2OIreland





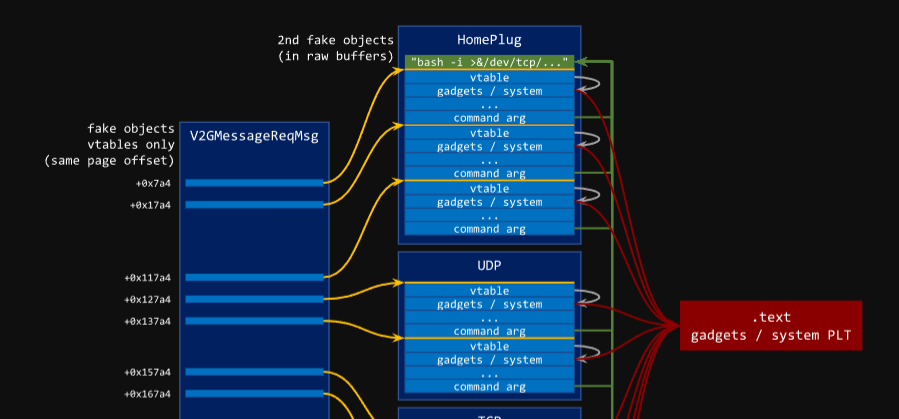
New blogpost! Want to see how we exploited Synology Inc. network-attached-storage devices at Pwn2Own Ireland? RCE to root via out-of-bounds NULL-byte writes, click the embed for a fun little writeup of CVE-2024-10442 🔎🎉 blog.ret2.io/2025/04/23/pwn…