osint
@osintcookie
ID: 1892115607706886144
19-02-2025 07:35:30
219 Tweet
6 Followers
169 Following








Elias Daler Packt cookbooks are pretty terrible




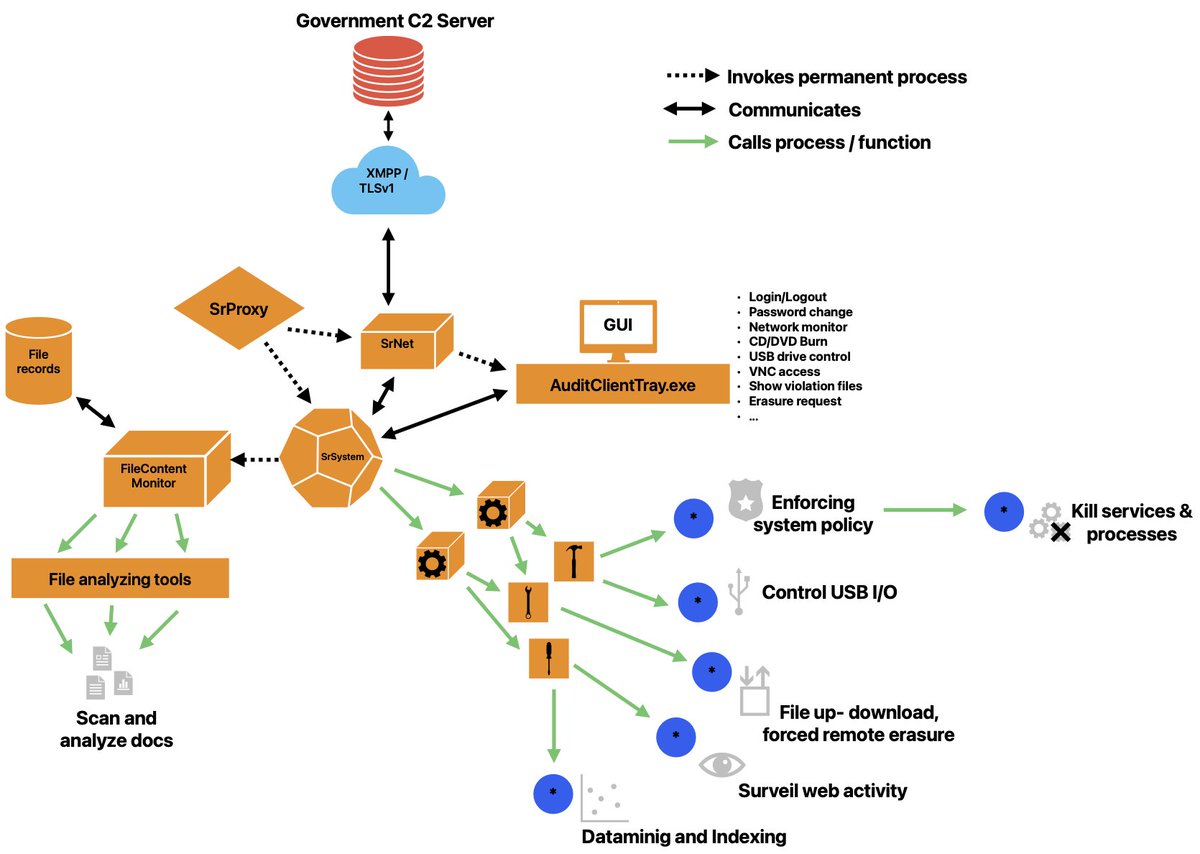
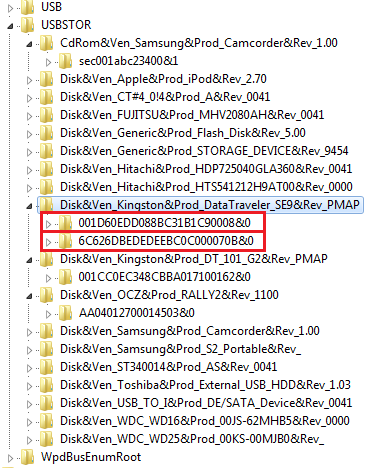
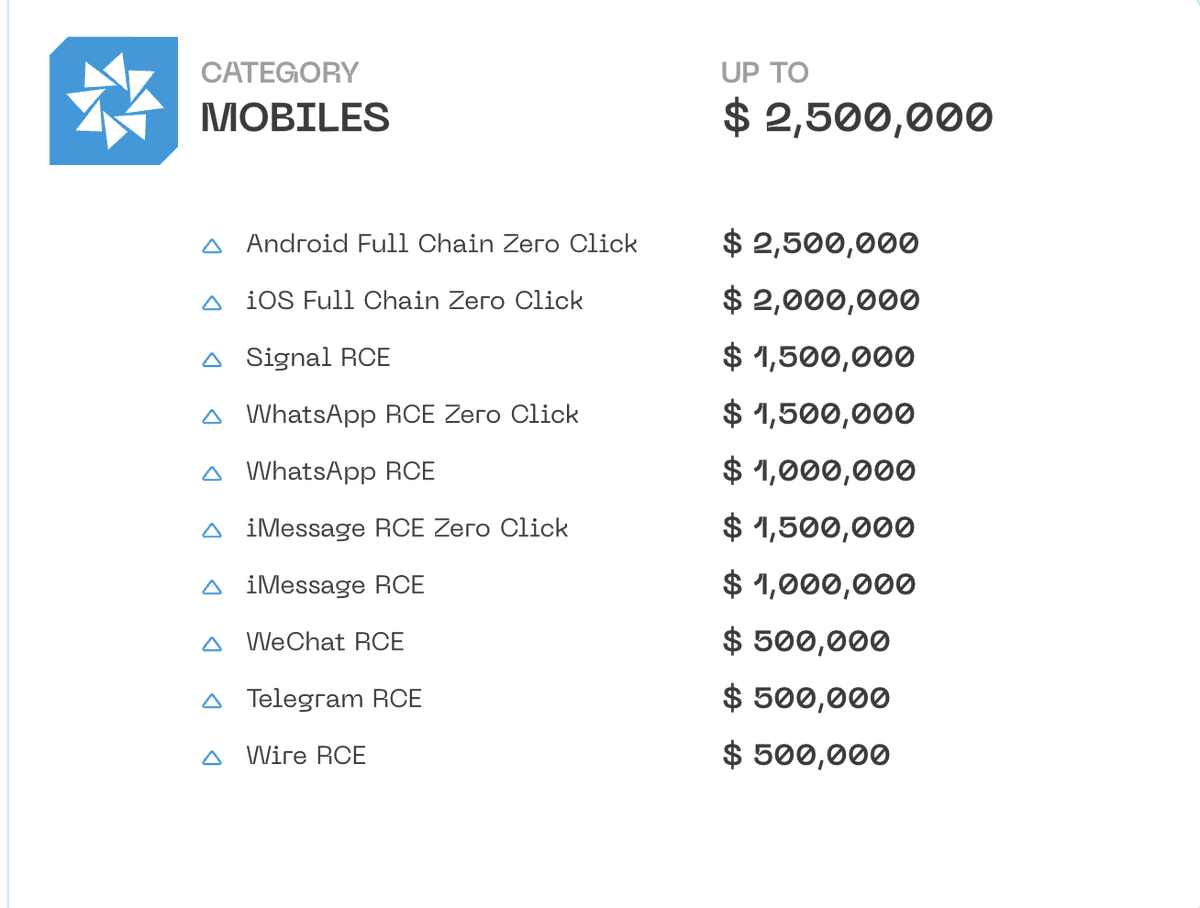
Today the United States sanctioned Sergey Zelenyuk, and his company Matrix LLC, notably for "acquiring at least eight proprietary cyber tools exclusive to the United States government". Want to guess what those tools were? See image two! Info via John Scott-Railton




Sam Altman shut the fuck up you technocrat piece of shit