NotSurprised
@notsurprisedtw
I don't know when it'll end. It's nobody guess.
ID: 844323237966200832
21-03-2017 23:02:01
32 Tweet
6 Followers
259 Following









The Hardware Hacking Handbook final version by Jasper van Woudenberg and Colin O'Flynn is finally out! 🥳 nostarch.com/hardwarehacking



First confirmed entry for day1 of TianfuCup, Kunlun Lab SorryMybad pwned Google Chrome to get Windows system kernel level privilege with only two bugs. First time since 2015 as I remembered





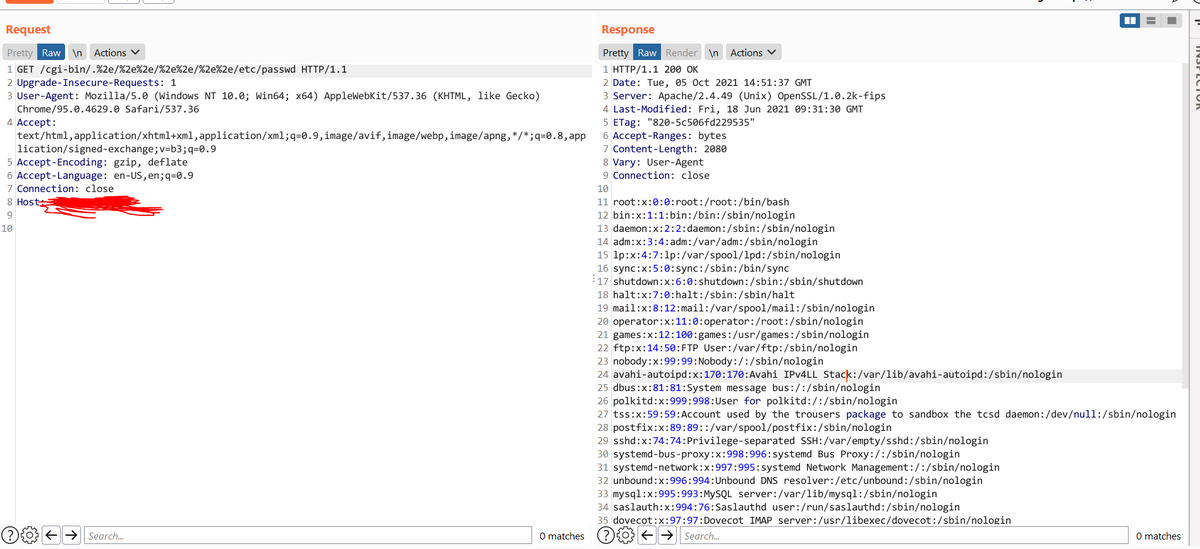
#Nginx 1.18 exploit in the wild! #infosec #0day #exploit Catalin Cimpanu