Prometheus
@nftyprometheus
ID: 1092446830108045314
04-02-2019 15:36:35
614 Tweet
70 Followers
0 Following


Mudit Gupta The wallets ****NOT***** affected by this: Ledger Trezor MM / MEW / MyCrypto / anything ethereumjs That said, if your SRP is from 2019 or before and has ever been on an online device (meaning it has ever existed in any form besides 1) your hardware wallet 2) paper then you

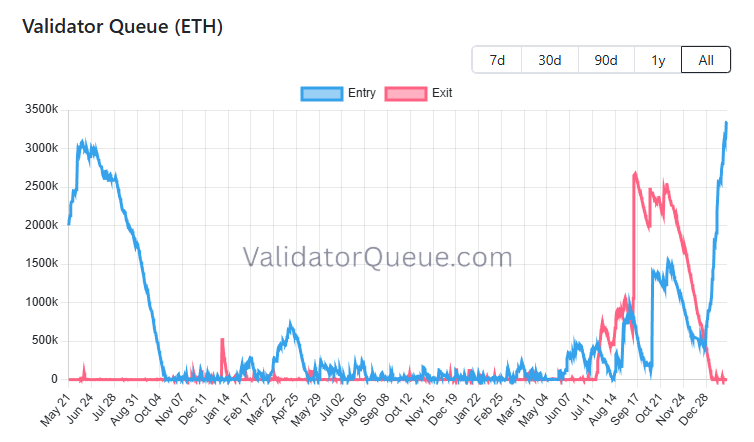
Bob Loukas 🗽 Also, as others pointed out, we may be heading into a reality where users don't even see the L2. They just see Ethereum, and the dapp frontend and intermediate protocols abstracts away the details, including the very concept of gas fees even.