Grimmjow
@neocyberx
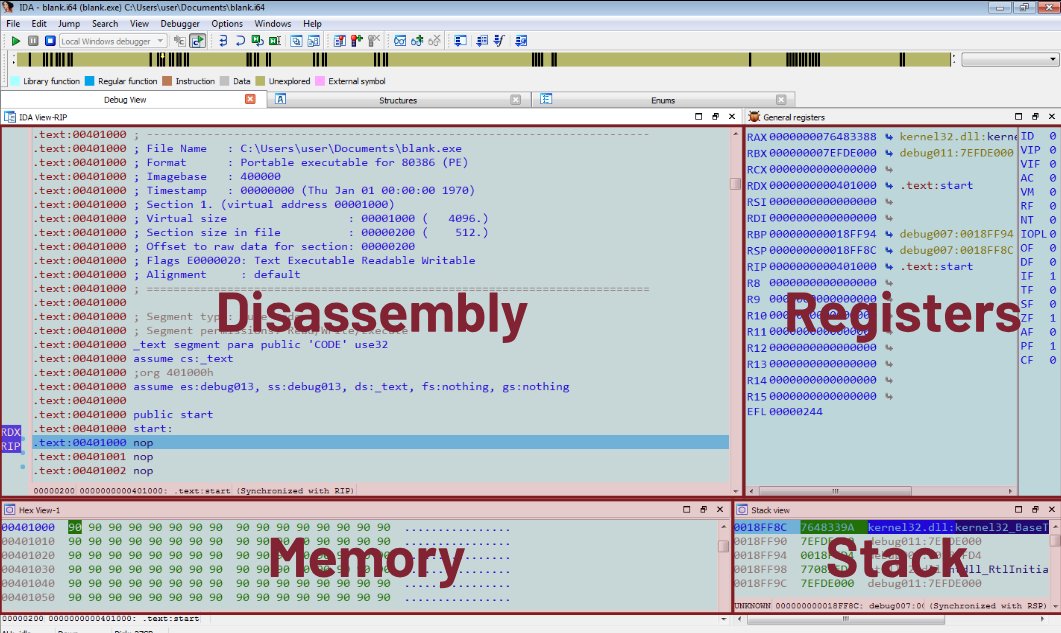
EDR | Malware | TH
ID: 1840965778910429187
01-10-2024 04:03:58
264 Tweet
31 Followers
172 Following






Stop “trying harder” for OSCP. Start using a system. Hacker Blueprint helps you: → Build a real pentesting methodology → Practice on exam-like AD labs → Eliminate guesswork with structured notes This is how people actually pass. Check it out 👇 hackerblueprint.pages.dev