nate
@nate2x4
Sysadmin turned CSIRT.
ID: 1905304646
25-09-2013 20:18:29
689 Tweet
253 Followers
674 Following










Woo! Big thank you to Invictus Incident Response !

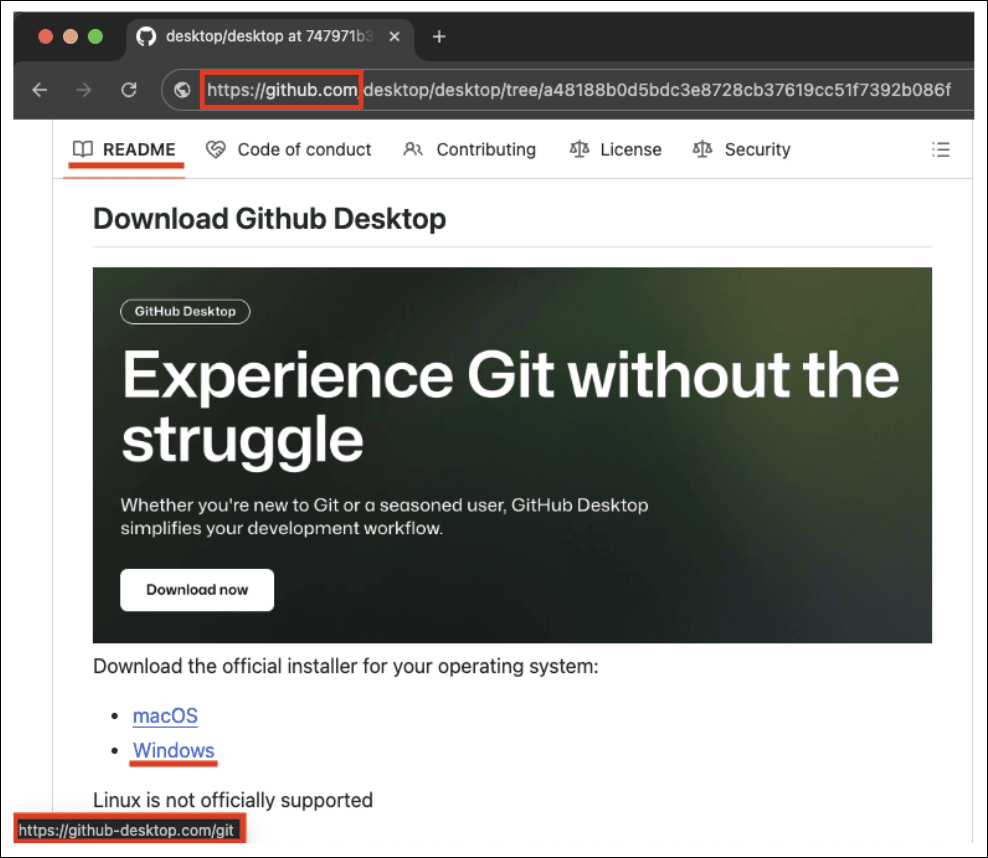
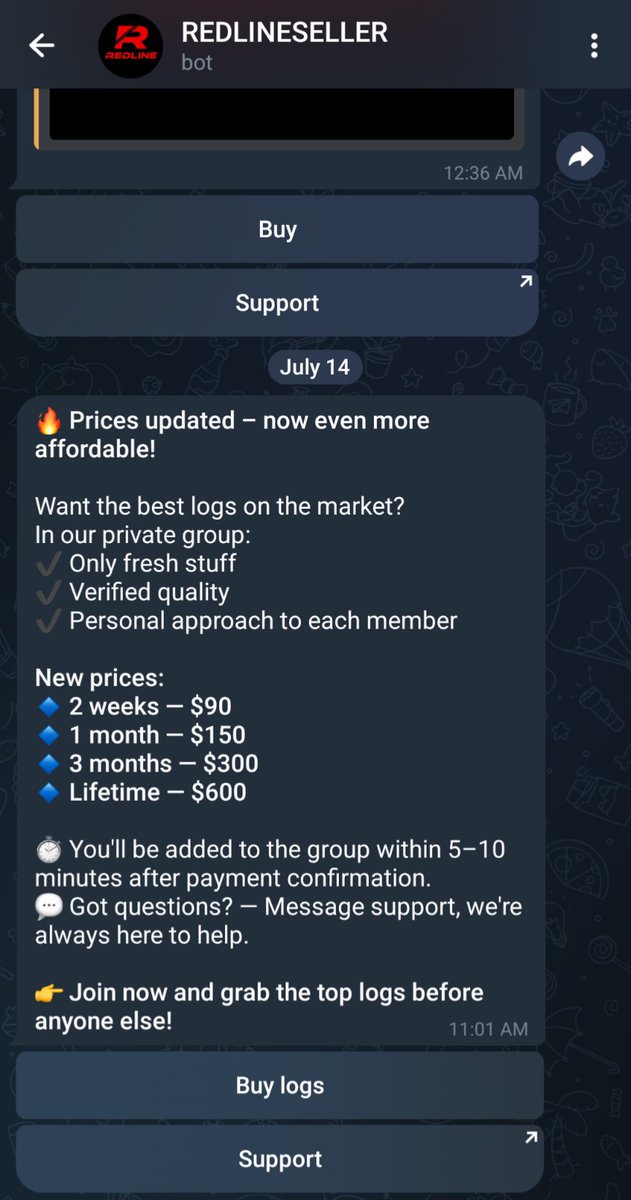
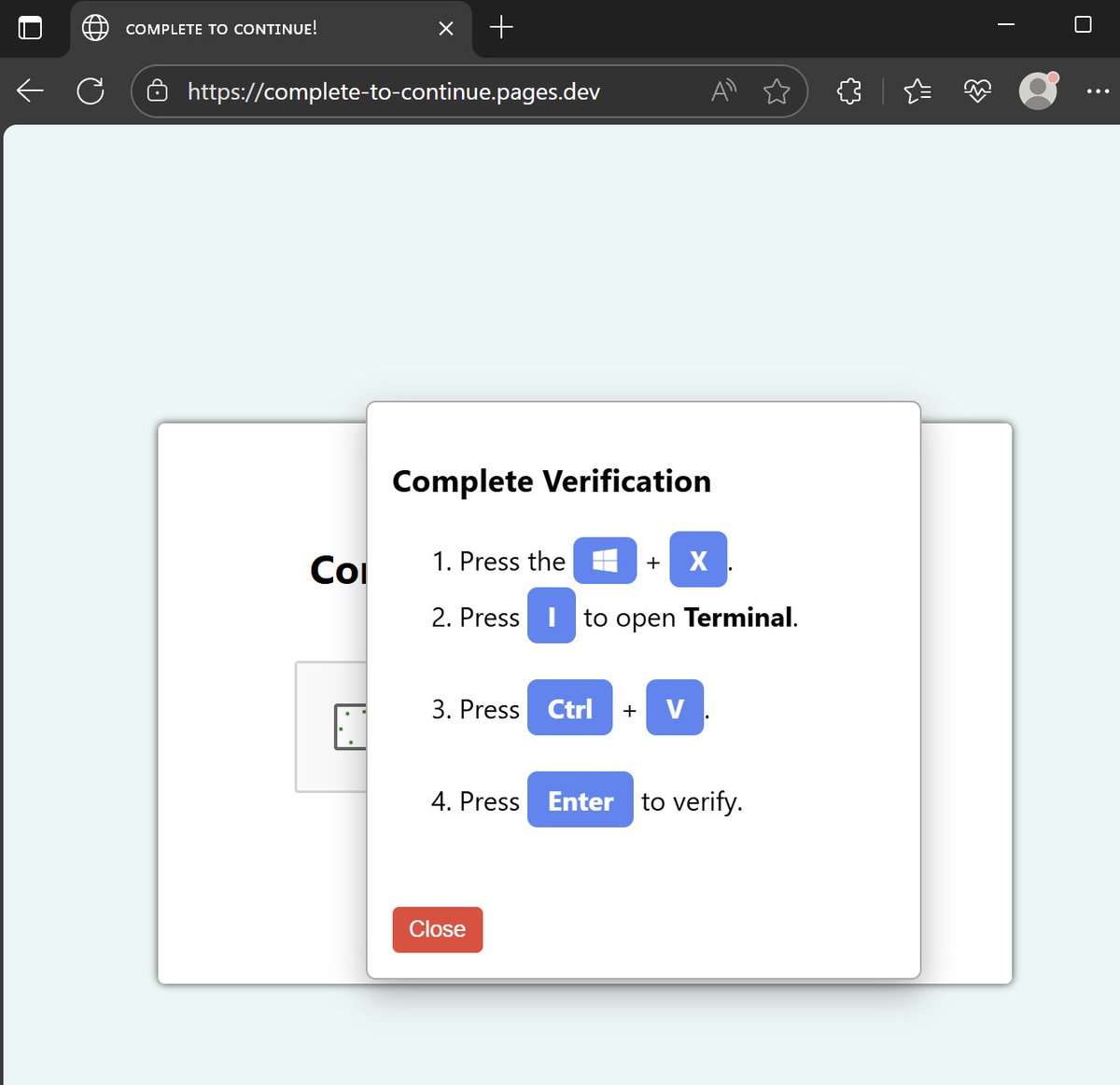
🚫 These threat actors tried to hide their code behind the GPU. We caught them anyways. 🐺 Our Arctic Wolf Labs team uncovered a threat actor abusing GitHub’s repository structure and Google Ads to redirect users to a malicious download, while a GPU-gated decryption routine kept