duckie
@n0tduck1e
likes malware | does blue+red team things | OSCP
check out my rarely updated blog 👇🏻👇🏻👇🏻
ID: 803647654617956352
https://n0tduck1e.github.io/ 29-11-2016 17:11:46
3,3K Tweet
289 Followers
1,1K Following


AirTouch from Hack The Box is a wireless box featuring SNMP enumeration, WPA2-PSK capture and crack, WireShark traffic decryption, client-side cookie role bypass with a phtml upload, and an evil twin via eaphammer to capture a crackable challenge. 0xdf.gitlab.io/2026/04/18/htb…








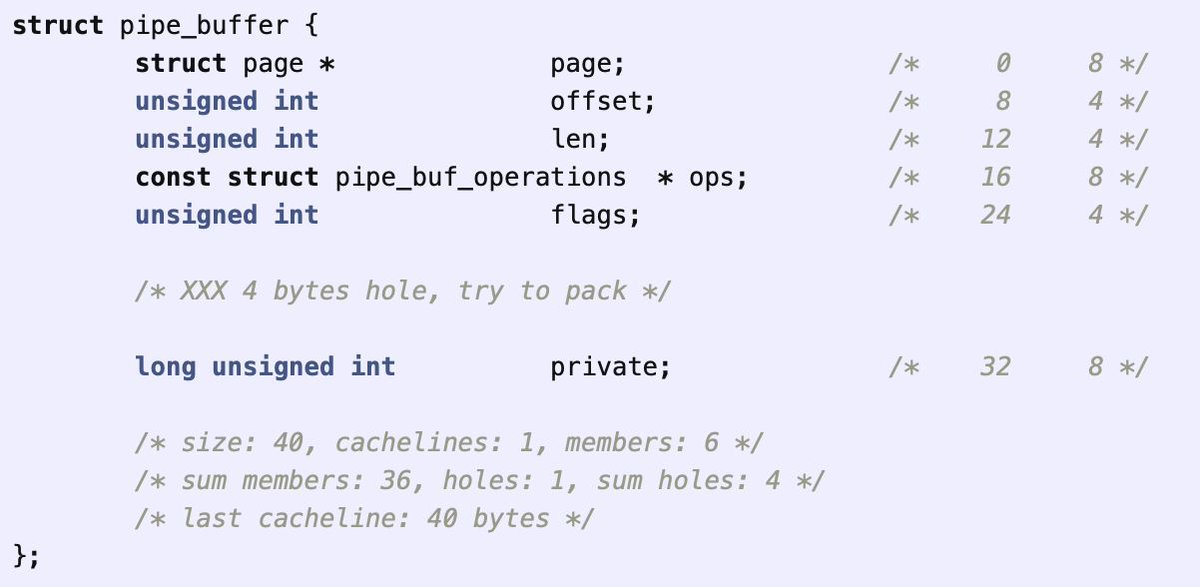
Security properties of the Linux kernel pipe_buffer object for building exploit primitives by Alexander Popov a13xp0p0v.github.io/2026/04/20/pip… #infosec