king 👑
@musengeng
ID: 1434133402635091971
04-09-2021 12:37:16
1,1K Tweet
80 Takipçi
2,2K Takip Edilen

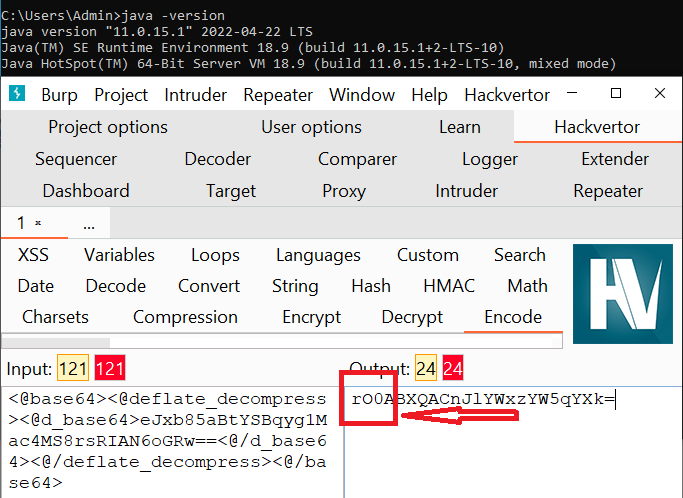
Not able to understand the behavior. Anyone has any clue? Two different result of java program on 2 different operating system. Burp Suite hackvertor #deserialization #Java



And that's a wrap! To dive deeper into how email security strategies can unintentionally leak sensitive info to the public, check out the full slides in Shockwave - External Attack Surface Management.'s blog post 👇 🔗 shockwave.cloud/blog/email-sec…









Wanna learn API hacking checkout this playlist by Katie Paxton-Fear YouTube: youtube.com/playlist?list=…











![YS (@yshahinzadeh) on Twitter photo This one was easy: searched JS files → revealing endpoints → JSON HTTP request → exposed PII. Tip: account for lazy-loading. many hunters miss endpoints. Method: click to trigger lazy-loaded JS, then search again for endpoints. Happy hunting :] This one was easy: searched JS files → revealing endpoints → JSON HTTP request → exposed PII. Tip: account for lazy-loading. many hunters miss endpoints. Method: click to trigger lazy-loaded JS, then search again for endpoints. Happy hunting :]](https://pbs.twimg.com/media/G4SM64xXQAAhU47.png)