Manuel Urueña
@muruenya
Security Architect at @RedeiaCorp. Entropy fighter.
@[email protected]
@muruenya.bsky.social
ID: 261301392
05-03-2011 17:37:00
8,8K Tweet
341 Takipçi
1,1K Takip Edilen



MeteorExpress (aka Predatory Sparrow, Gonjeshke Darande, Adelat Ali, Indra, CodeBreakers, etc) represents the most significant effort at cyber signaling and force projection in nearly a decade. #NoRegerts sentinelone.com/labs/meteorexp…


🚨NEW REPORT: exposing a new hacking tactic. 🇷🇺Russian state-backed hackers used an App-Specific Password attack against prominent Russia expert Keir Giles & others. It's like they know what we all expect from them...and then did the opposite 1/ By us The Citizen Lab & @google's


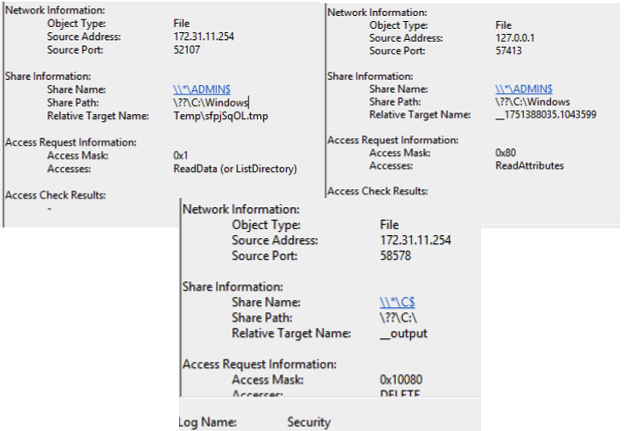
New The DFIR Report Hide Your RDP: Password Spray Leads to RansomHub Deployment thedfirreport.com/2025/06/30/hid…