Sergej Schumilo
@ms_s3c
Security Researcher sh -c ‘﹤&$1’
ID: 2318840439
https://schumilo.de 01-02-2014 21:53:54
220 Tweet
1,1K Followers
365 Following

Turns out, libxdc is still by far the fastest PT decoder out there! Find more infos on why libxdc outperforms honeybee: github.com/nyx-fuzz/libxdc. Thanks to Sergej Schumilo for investigating this and to Allison Husain {@[email protected]} for the fresh ideas and helping us understand the performance of honeybee!



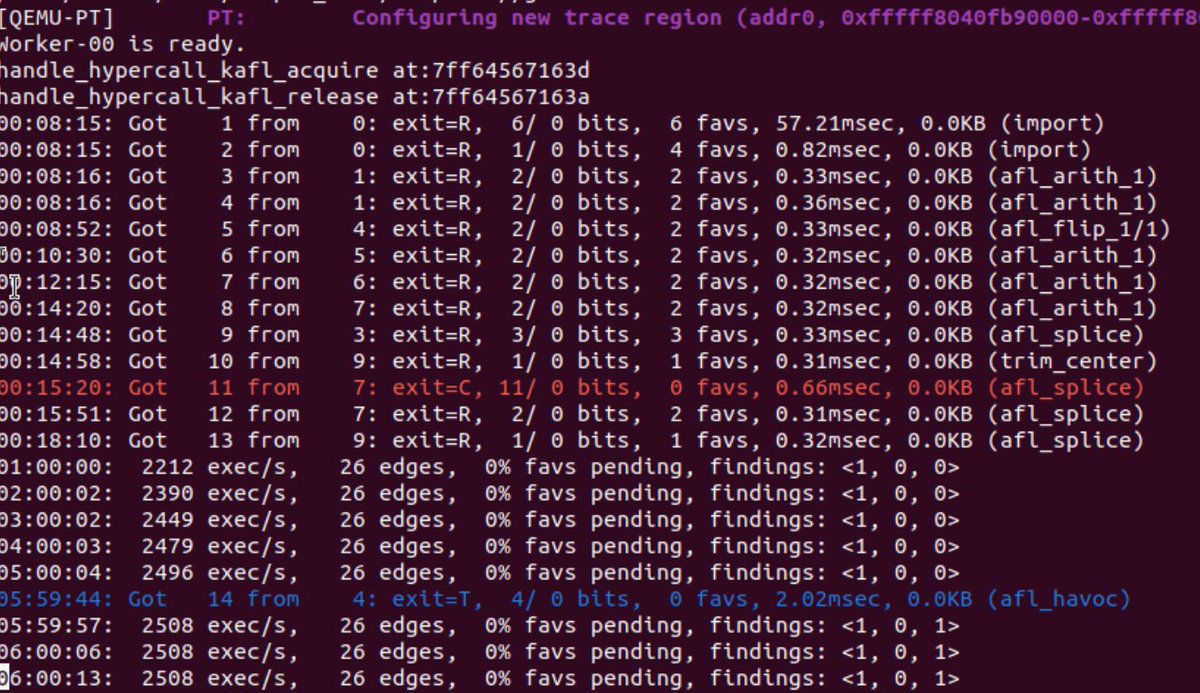
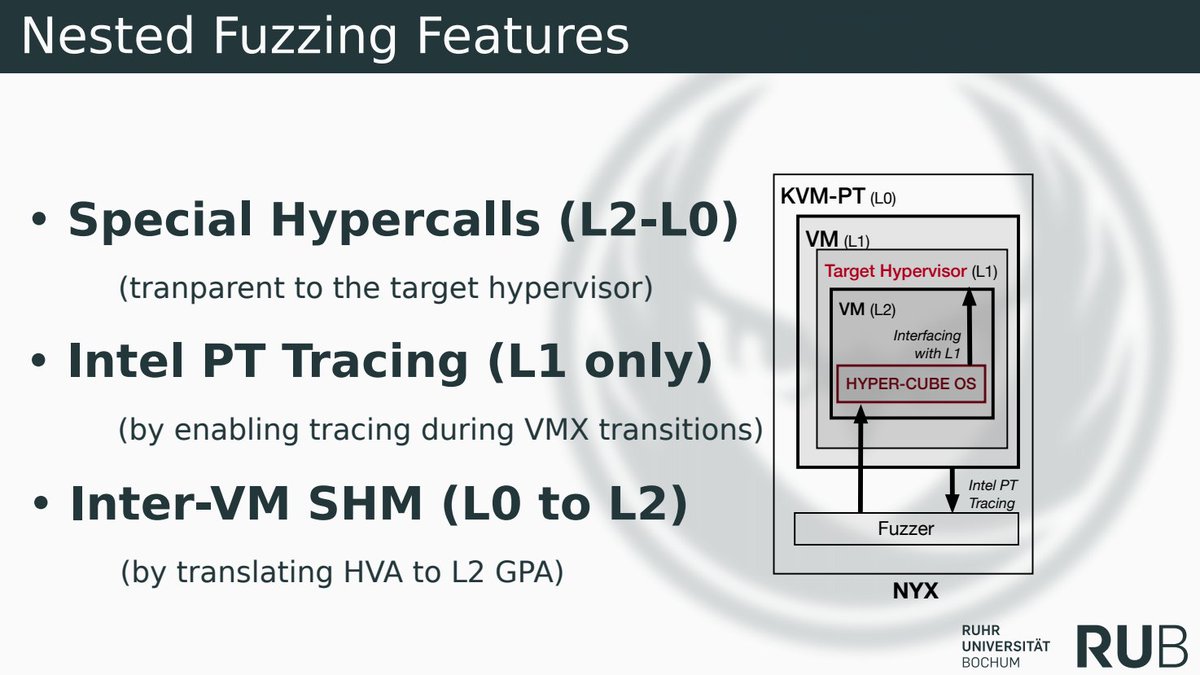
Sergej Schumilo and I just published the code of our snapshot based hypervisor fuzzer Nyx github.com/RUB-SysSec/Nyx. Paper and talk: usenix.org/conference/use…. Stay tuned for a much more polished version at nyx-fuzz.com

Our (is-eqv.bsky.social, Andrea Jemmett, @bl4ckic3 and Thorsten Holz) paper on robust snapshot based network fuzzing has landed on ArXiv, check it out here: arxiv.org/abs/2111.03013

Sergej Schumilo Sergej Schumilo and I also just published the most recent version of the codebase here: nyx-fuzz.com (the homepage even has gifs, check it out!!!)

Remember when Sergej Schumilo and is-eqv.bsky.social showed us how to fuzz Super Mario Bros. at FuzzCon Europe 2020? -> youtu.be/jkNao0SjBAA They just published the source code to their hypervisor-based snapshot fuzzer. Feel free to check it out! ->github.com/RUB-SysSec/nyx… #Fuzzing #SuperMario

Except from the Mozilla Security Firefox Security Newsletter/FSN-2021-Q3 (wiki.mozilla.org/Firefox_Securi…): "Now, we have received and successfully evaluated a research prototype for fuzzing the IPC Layer. " - Congratulations Sergej Schumilo and is-eqv.bsky.social!

Want to fuzz complex targets with AFL++ and snapshots? is-eqv.bsky.social and I now got you covered: there is a Nyx implementation for AFL++ available here github.com/nyx-fuzz/Nyx/b…

Full system, hypervisor accelerated, incremental snapshot fuzzing with Intel PT coverage engine enabling full protocol stateful fuzzing via Nyx-Net! Getting roughly 1000 exec/s/core on dnsmasq. This is followup work to kAFL/RedQueen. Kudos to the authors is-eqv.bsky.social and Sergej Schumilo!


expy is-eqv.bsky.social Sergej Schumilo Here is Nyx backend powering the familiar AFL++ frontend. This is still using intelpt + full system snapshots and achieving similar to inlined source instrumentation performance.




Every paper from them is gold. (is-eqv.bsky.social, Sergej Schumilo, Tim Blazytko et al) Every. Single. One. nyx-fuzz.com/papers/


🚀 kAFL release v0.8 1⃣ New Linux tutorial based on the Damned Vulnerable Kernel Module (DVKM) by Hardik Shah 2⃣ Docs how to use the kAFL "agent.sh" and sharedir based workflow to fuzz Linux targets 3⃣ A simplified kAFL agent in the Linux kernel !


starting a new fuzzer project on the blog that is based on an old Brandon Falk idea. in the first post, we load a statically built Bochs emulator ELF into our fuzzer process and execute it. there is some code and the humble beginnings of a repo. lets gooo h0mbre.github.io/New_Fuzzer_Pro…



📷We’re excited to announce the second training session for #TyphoonCon24: “Fuzzing & Attacking Deeply Embedded Devices” by Tobias Scharnowski (Tobias Scharnowski) & Marius Muench (nSinus-R (@[email protected])). Learn more and register: eventbrite.com/e/typhooncon-2…