Miasm
@miasmre













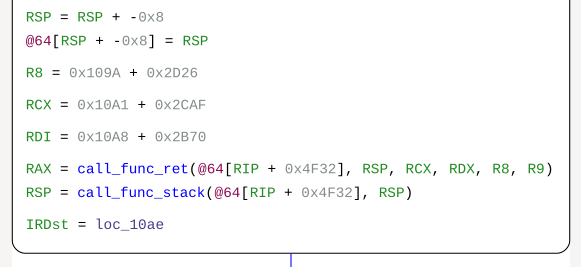
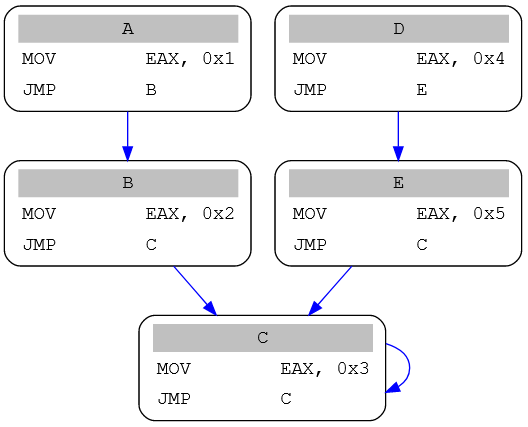
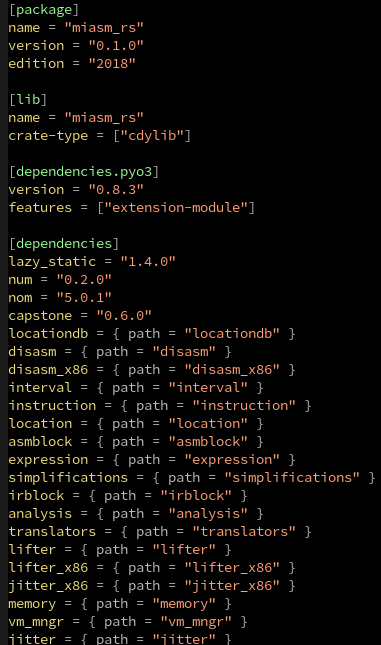
I finally decided to publish my complete toolset written for Tinynuke analysis You'll find config and injects grabber, dll extractors, Ghidra deobfuscation scripts and CEA IT Security miasm based scripts github.com/Heat-Miser/tin… #Tinynuke #ReverseEngineering #Malware


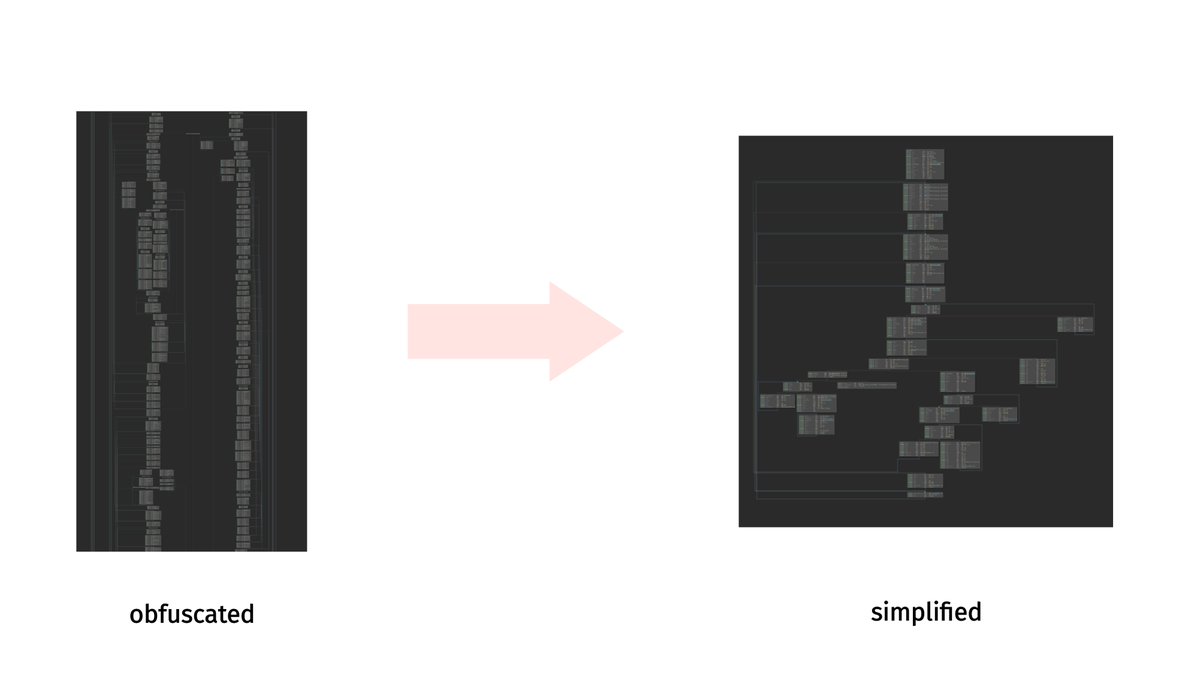
Little update: based on the great NCC Group Research & Technology blog post (research.nccgroup.com/2021/10/12/a-l…), we added color support for IR and ASM graph output: Thank you guys !