Samuel Dobson
@meshcollider
PhD (mathematics) from @AucklandUni
ID: 2819198815
19-09-2014 04:13:53
447 Tweet
5,5K Followers
225 Following



PhD Thesis submitted✅🎉 Has been a great journey, thank you Steven Galbraith for your excellent supervision! Now the wait for the examiners' reports begins 😎


An alpha version of my coinswap project is released! lists.linuxfoundation.org/pipermail/bitc… Doesnt have all the features yet, but works on regtest, signet and mainnet Imagine a new privacy tech for bitcoin, like coinjoin, but cant be blocked b/c the txes look exactly the same as regular txes


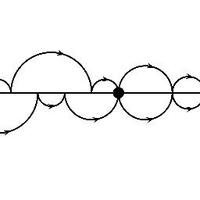
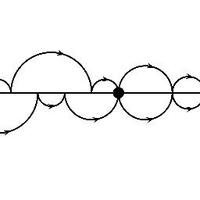
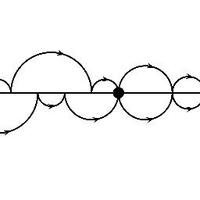
Congratulations to Samuel Dobson , who successfully defended his PhD thesis "Key Exchange and Zero-Knowledge Proofs from Isogenies and Hyperelliptic Curves" this morning.