Mark Dufresne
@mark_dufresne
Detection Engineering @sentinelone
ID: 25934148
23-03-2009 02:21:04
632 Tweet
1,1K Followers
570 Following



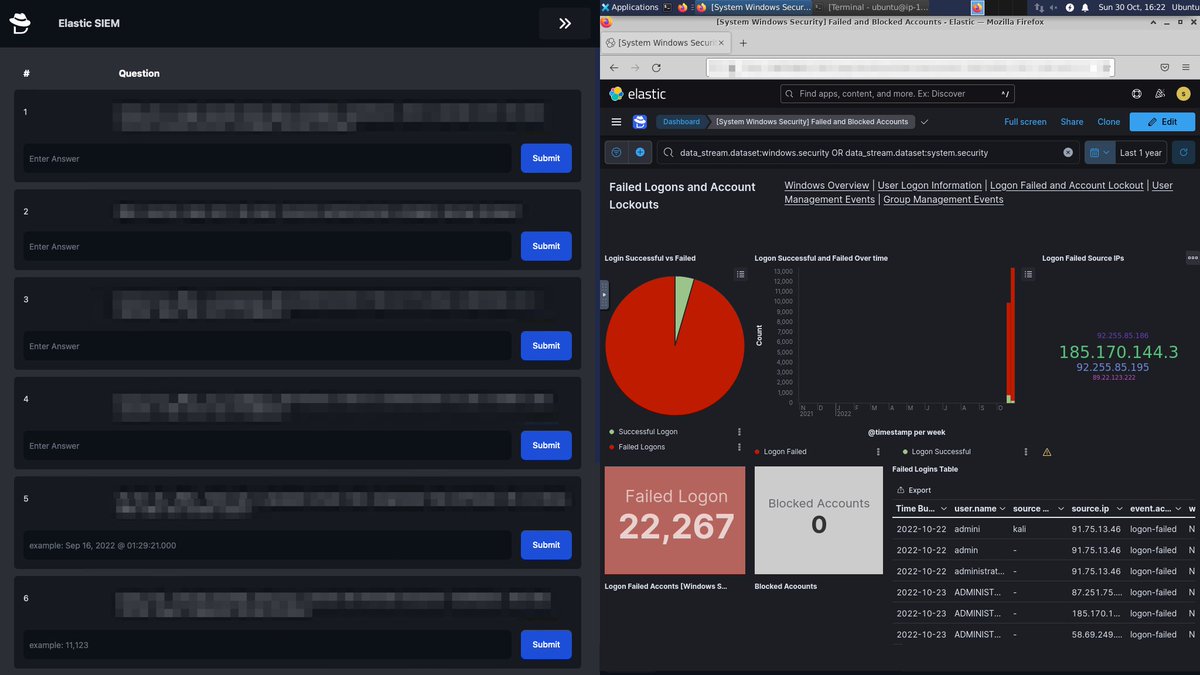
Check out REF2731 research - a 1, 2, 3...4...5 stage(!) intrusion set for two PARALLAX + NETWIRE campaigns. Malware & campaign analysis and an open-source payload extractor. Collab w/Daniel Stepanic SolidSnake Seth Enjoy, it's a journey. elastic.co/security-labs/…


Amazing write-up on a dynamic emotet config extractor by RemcoS. He uses a combination of YARA, the SMDA decompiler, Unicorn Engine, lief-project and more to get the job done. Read it! And then read it again. And maybe again. elastic.co/security-labs/….

Happy Friday, Twitter! If you don't know Terrance DeJesus let me correct that-- Terrance is a member of the Threat Research and Detection Engineering team Elastic. His most recent publication to Elastic Security Labs is part one of three on Google Workspaces: elastic.co/google-workspa…

Our team had tons of fun participating in this year’s #FlareOn9 Challenge. Check out our write-up on how we solved them! Thanks Mandiant (part of Google Cloud) for all your effort putting it together. elastic.co/flare-on-9-sol…

We’re proud of the #ElasticSecurityLabs team and the incredible amount of work that went into creating the 2022 Elastic Global Threat Report. Mark Dufresne shares a behind-the-scenes look into how the report was built. Read more here: go.es.io/3OxutUd



New SentinelLabs Research on WIP26 - s1.ai/WIP26 🟣 New actor targeting telco in the Middle East 🟣 Abuses Microsoft 365 Mail, Google Firebase, and Dropbox for C2 🟣 Targeted WhatsApp msgs -> Dropbox -> loader -> backdoors Aleksandar Milenkoski Collin Farr 91 QGroup IT-Security





Yesterday I learned that SentinelOne blocks the Windows application white listing and digital signature bypass that I’ve been using for 10 years. Now I’ll need to find a new way to digitally sign any binary as Microsoft (on S1 customers). Well done SentinelOne.