Luke Wei🦇🔊
@lukewei8
程序员、铲屎官、Bitcoiner
ID: 1341480776018227201
22-12-2020 20:28:45
101 Tweet
574 Followers
2,2K Following



We just announced the launch of $100M ventures fund! Let’s go OFR! Old Fashion Research Cover from Bloomberg




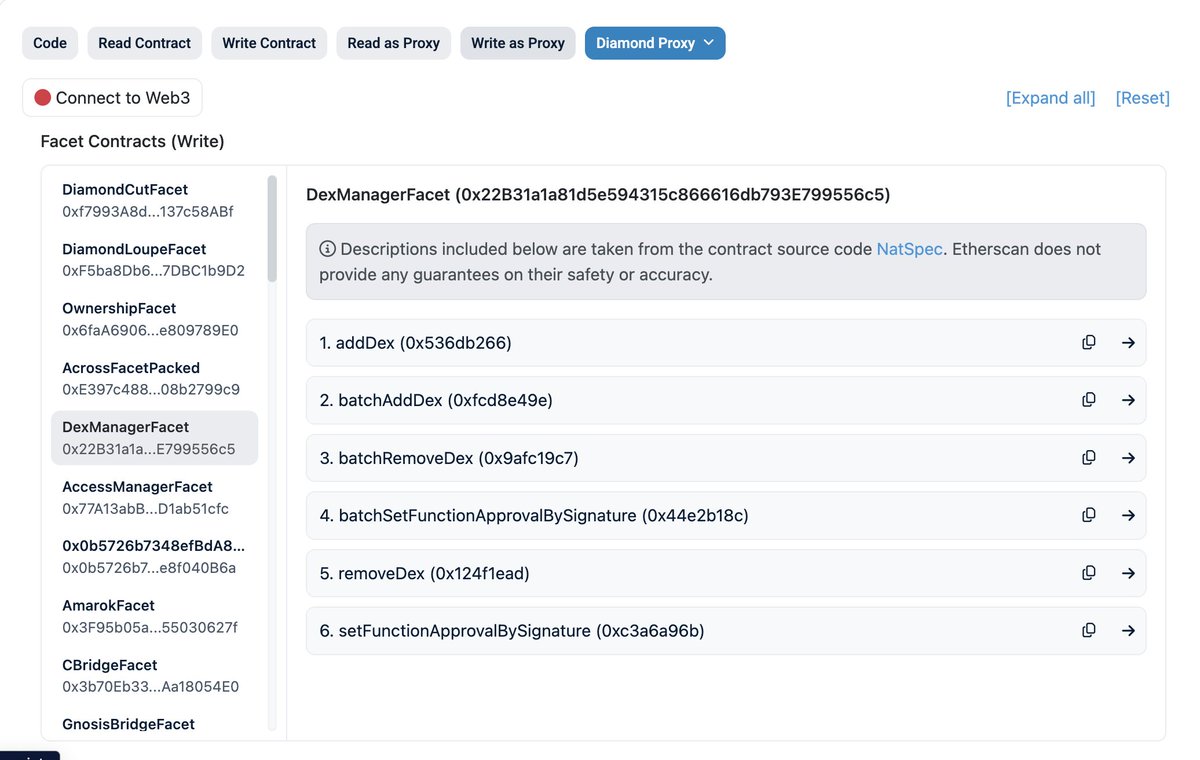
EIP-2535 Diamond Standard Now Finalized! A standard for designing "upgradeable" & "replaceable" contracts, also known as the Diamond Standard by Nick Mudge 💎
Secure on-chain randomness is a topic that has been touched on a lot over the past few years. In the latest blog, by Paradigm Engineering, sina.eth, Georgios Konstantopoulos, and I explore and implement secure randomness on Ethereum using SNARKs and VDFs. paradigm.xyz/2023/01/eth-rng






1/ How to use MetaDockMetaSuites (Prev. MetaDock)'s variable log to identify a rug token contract with a backdoor. IGET token on BSC (0x8D07f605926837Ea0F9E1e24DbA0Fb348cb3E97D) has a backdoor to mint a large number of tokens to a backdoor address. Thanks to @MetaDockTeam's excellent tool.