LoomingSecurity
@loomingsecurity
Always looking the edge in cybersecurity…
ID: 1409553635701370882
28-06-2021 16:46:29
22 Tweet
11 Followers
228 Following

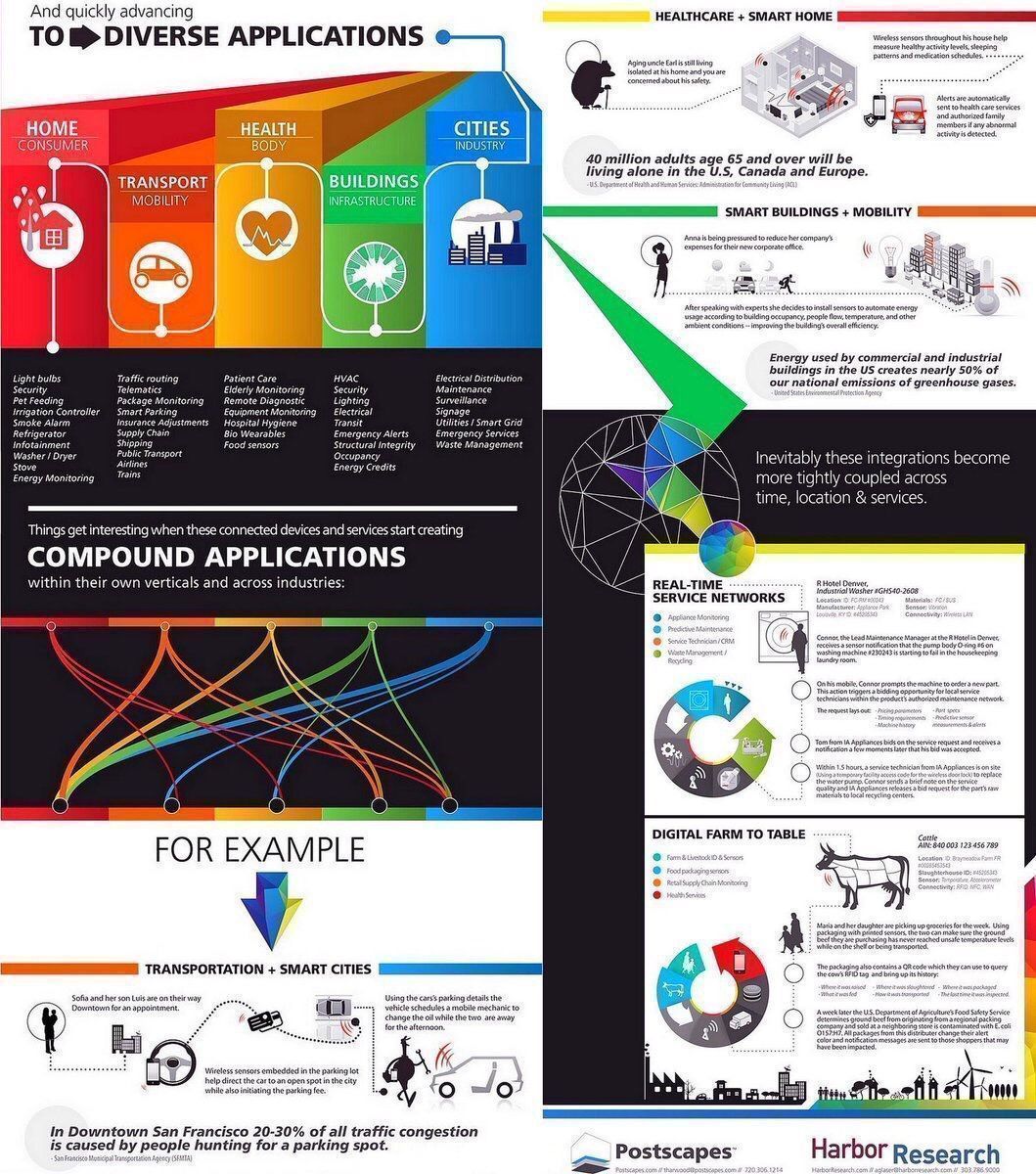
What are some application use cases for #IoT? #BigData #SmartCity #fintech #AI #ML #startups Michael Fisher #innovation #Sensors #IIoT #Healthcare

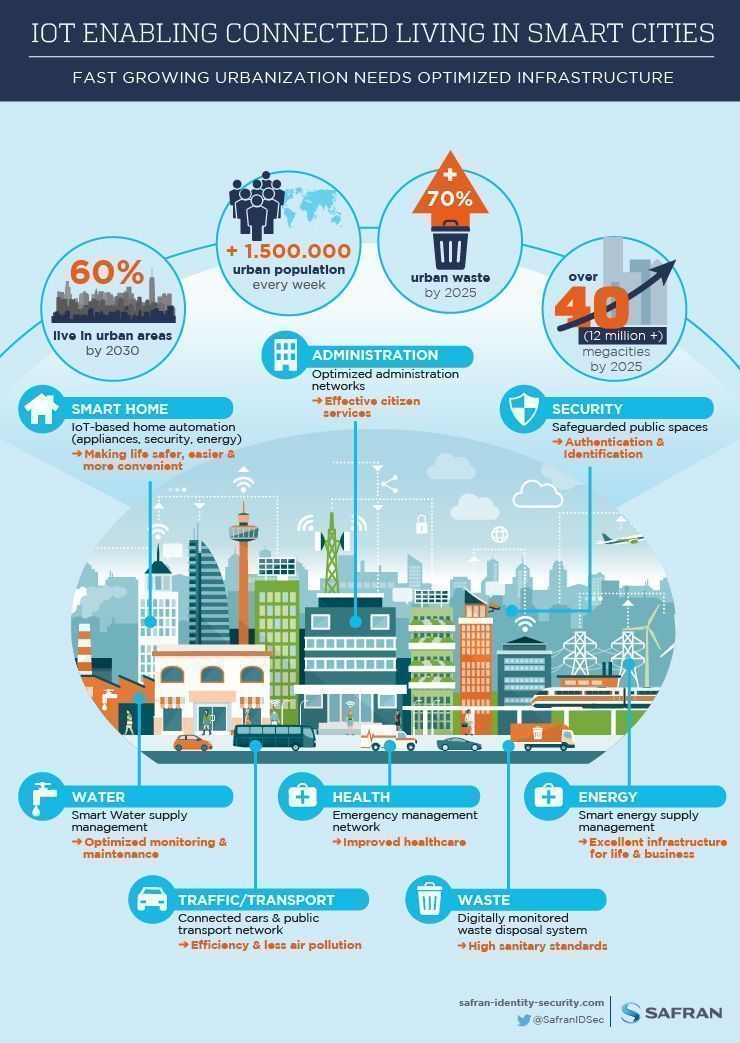
Internet of Things Living in #SmartCities {Infographic} #IoT #Healthcare #IIoT #M2M #CyberSecurity #Analytics #AI #ML Michael Fisher #fintech #BigData


CEO & Co-Founder Ruvi Kitov took center stage at #FortinetChampionship21 during today's security summit to counsel attendees on #cloud enablement & digital transformation via #automation.


To control risk & maintain compliance, enterprises need full visibility of the perimeter and “inside” the #cloud. 👀☁️ Learn why #securitypolicy mgmt is critical for #cloudadoption & migrations: okt.to/wW9VKm #cloudsecurity Cyber Management Alliance - Cybersecurity Training




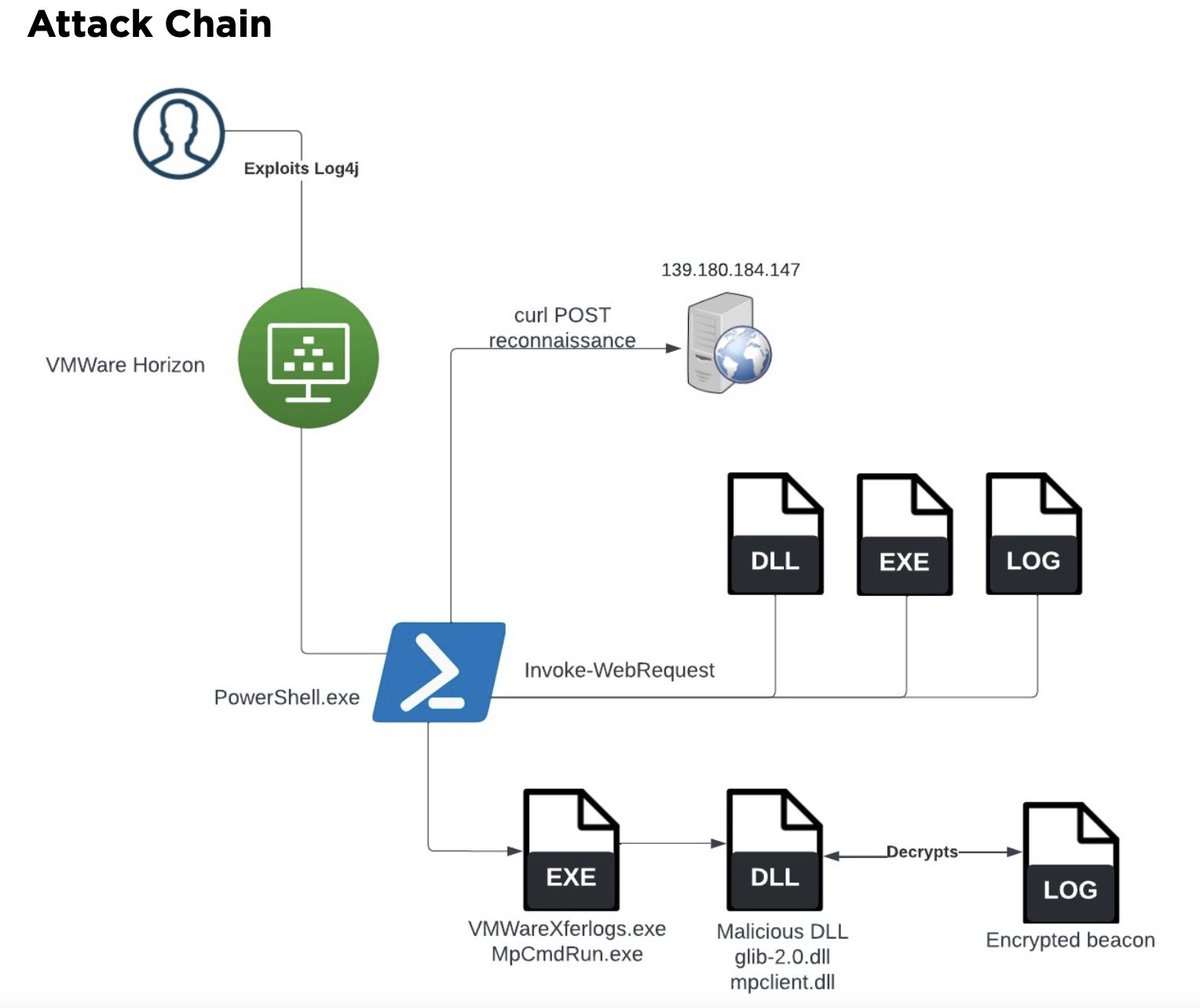
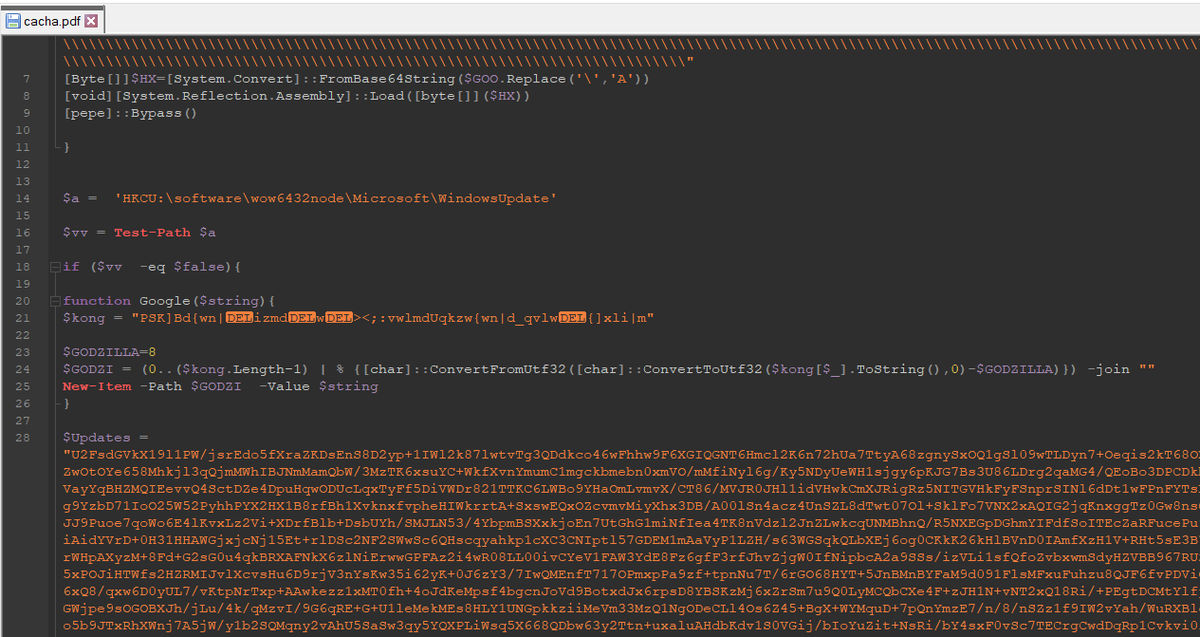
Analysis via SentinelOne details Lockbit #ransomware group "abusing the Windows Defender command line tool MpCmdRun.exe to decrypt and load Cobalt Strike payloads" sentinelone.com/blog/living-of… #malware #cybersecurity

In this article from Silicon Republic, CTO & Co-Founder @reuvenharrison covers the dangers of an ‘us versus them’ attitude between developers and security teams plus how to avoid them: okt.to/mj6a2D








Top Cyber Attacks - 2026 via Cyber Security News

![Anthony Randazzo (@amrandazz) on Twitter photo We were trying to conceptualize the "current state" of cloud [native] threat detection and this is what we sorta came up with. Sharing it more broadly in case others find it useful in organizing your cloud detection & response approach 🔎 We were trying to conceptualize the "current state" of cloud [native] threat detection and this is what we sorta came up with. Sharing it more broadly in case others find it useful in organizing your cloud detection & response approach 🔎](https://pbs.twimg.com/media/FRNQs-lWYAMlMa6.jpg)