Daniel Kalinowski
@llamaonsecurity
Founder of @tlbcpl - Security researcher, spare time bounty hounter
ID: 93431155
https://dkalinowski.me 29-11-2009 16:30:25
593 Tweet
301 Followers
1,1K Following

TODAY IS THE DAY! The Frans Rosen Episode is LIVE. Frans Rosén is pretty much the king of bug bounty and because of all the crazy research and content we had to talk about, this episode ran over 2h. It's one of the best ones we've put out yet. Enjoy. ctbb.show/s1e45








I just posted a roadmap on how I learnt C (+ x86-64 Assembly and OS Internals) from scratch. I highly recommend it to anyone planning to take a course at OpenSecurityTraining2 or who is interested in malware development. github.com/theokwebb/C-fr…



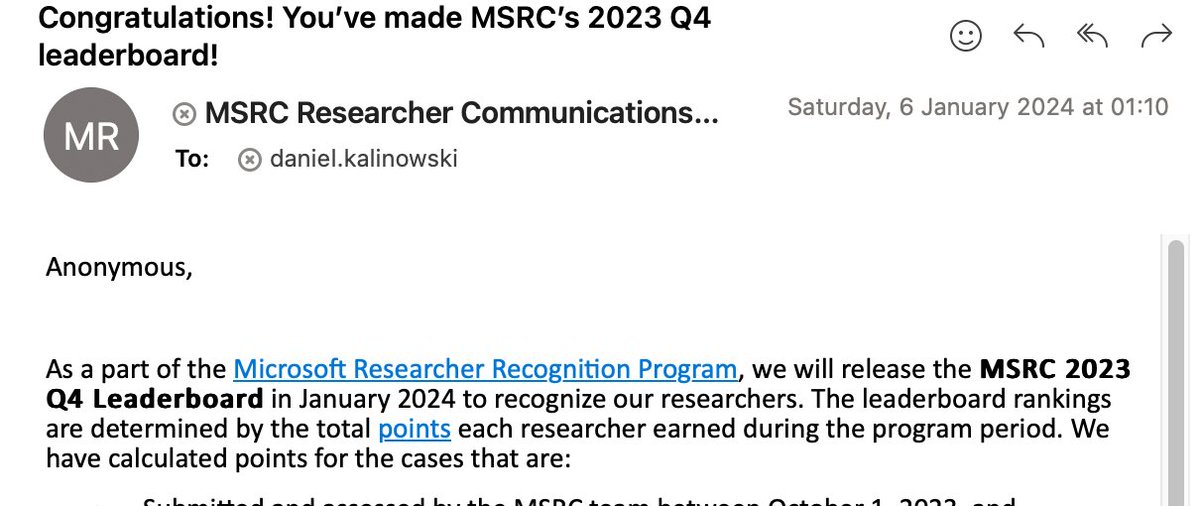
Pierogi team 🥟🇵🇱 secured 8th place. Thanks Bug Bounty Reports Explained for this opportunity!