Ling
@ling_sec
I do security things (sometimes)
ID: 1140992833236733952
http://ling.re 18-06-2019 14:41:04
193 Tweet
263 Followers
863 Following


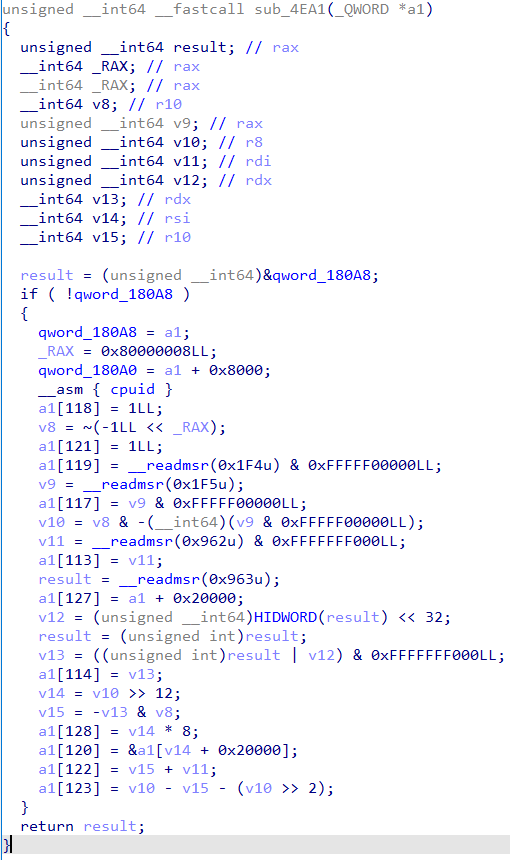
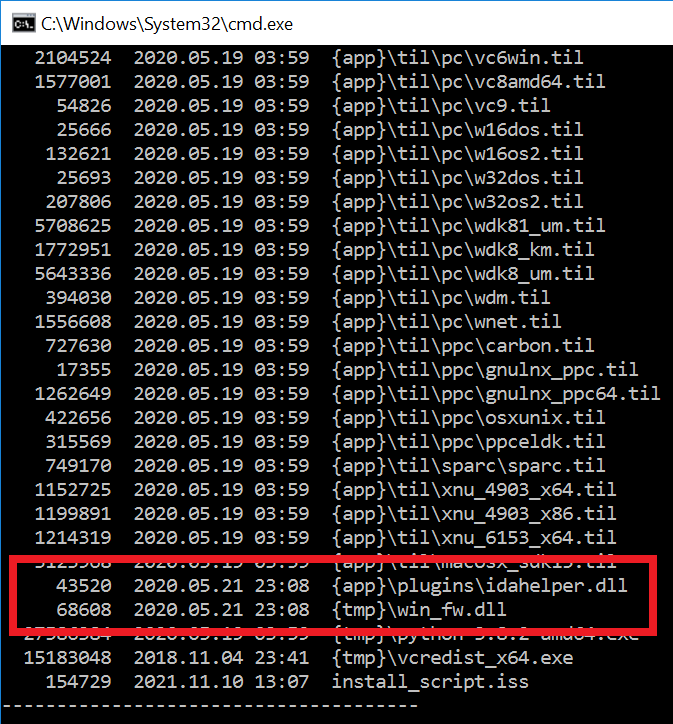
#ESETresearch discovered a trojanized IDA Pro installer, distributed by the #Lazarus APT group. Attackers bundled the original IDA Pro 7.5 software developed by Hex-Rays SA with two malicious components. Anton Cherepanov 1/5














May I present to you; a full copy of doom, running inside of a Rollercoaster Tycoon 1 save game exploit ✨ Thanks for everyone that came to check out our DistrictCon Junkyard talk! We had a lot of fun putting it together. (check the thread for slides / exploit)