ledziow (aka W0J)
@ledziow
Senior Principal Threat Analyst at Advanced Practices in Mandiant Intelligence
ID: 4011882143
https://www.linkedin.com/in/wojciech-ledzion-68599542/ 21-10-2015 20:14:55
456 Tweet
409 Takipçi
167 Takip Edilen

This year at confidenceconf I’ll be presenting on UNC4841 with my talk titled "Tales from the Deep". Join me on 27-28 May 2024 in Krakow! Get 15% off your ticket with the discount code: TEAM15 (for individual registrations). confidence-conference.org



confidenceconf was a really impressive conference and it was an honour to present there this week. Overwhelmed by all the positive feedback! Thanks to all the organisers and attendees, I met so many great fellow experts this week. I hope to be back again one day in Kraków. 🇵🇱👨💻


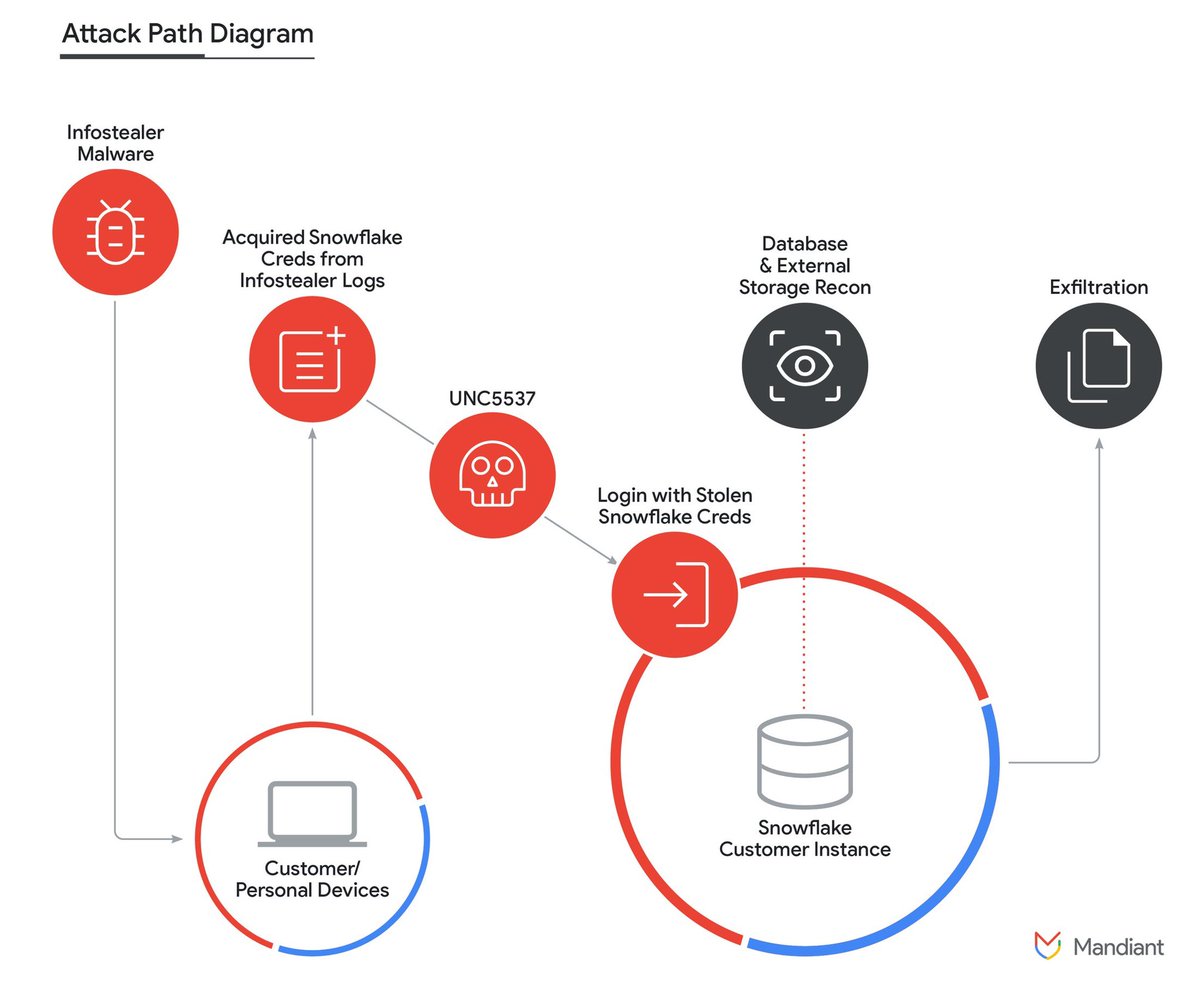
Mandiant (part of Google Cloud) is releasing details on a data theft and extortion campaign undertaken by UNC5537, targeting Snowflake customer instances. Since April, UNC5537 has leveraged stolen credentials to target over 100 organizations. cloud.google.com/blog/topics/th…

🚨 ALERT: Mandiant (part of Google Cloud)'s #AdvancedPractices team has recently received a video message from a State nexus actor. Sharing this for general visibility. Be safe out there. cc:Ryan Kazanciyan 🚨 cameo.com/recipient/664e…

CrowdStrike is actively working with customers impacted by a defect found in a single content update for Windows hosts. Mac and Linux hosts are not impacted. This is not a security incident or cyberattack. The issue has been identified, isolated and a fix has been deployed. We


“Malware distribution groups are tricky to look at as a collective, so let’s narrow it down to some of my *least* favorites…” See ya next week, mWISE Conference 🫶🏼 #mWISE2024







Looking forward to giving my first TEAM CYMRU research webinar tomorrow! I shall be discussing a hot topic for many: DPRK IT Workers👨🏻💻 Tune into this tomorrow if you’re interested in how you can use NetFlow data to detect the 🇰🇵 activities 🔍 Reg here: team-cymru.zoom.us/webinar/regist…