Kitto Hernandez
@kittoh_
will never stop pushing 🫷🏼... .. . .
ID: 923013260785336320
25-10-2017 02:28:04
6,6K Tweet
334 Followers
3,3K Following

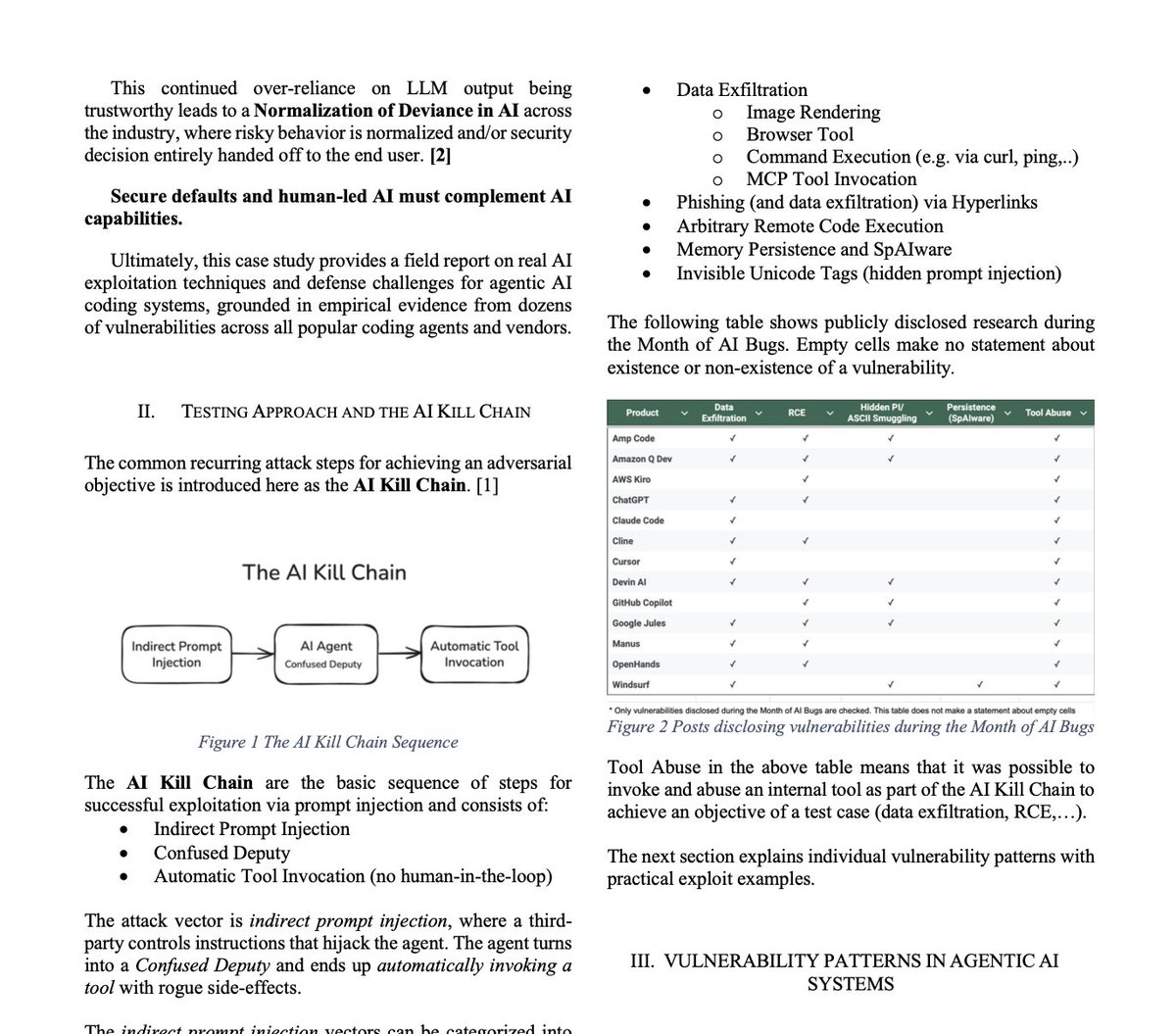
Before launch, Perplexity hired us to test the security of Comet, their AI browser assistant. We demonstrated how four prompt injection techniques could extract users' private information from Gmail. 🧵

infosecwriteups.com/hacking-micros… This is the longest and most in-depth article I’ve published on Medium so far. It covers IIS and ASP dotNET vulnerabilities from absolute basics to advanced techniques. Even if you have zero background in IIS, you’ll be able to understand the fundamentals

















BREAKING: While a new War for Oil erupts in the Middle East A Physics Paper just quietly dropped TODAY that will eventually make Oil, and the entire current Energy Industry, irrelevant. Ushering in the era of Zero-Point Energy Harold "Sonny" White, PhD Here is the breakthrough🧵