Ziyi Guo
@kitahara_triple
CS Ph.D. Student @NorthwesternU / 42-b3yond-6ug #aixcc / CTFer @r3kapig / Cyber Security, LLM agent for Security
ID: 1199288268530913281
26-11-2019 11:26:26
93 Tweet
470 Takipçi
181 Takip Edilen

The award-winning Qualys Threat Research Unit (TRU) has discovered a critical vulnerability in OpenSSH, designated CVE-2024-6387 and aptly named "regreSSHion." This Remote Code Execution bug grants full root access, posing a significant exploitation risk. blog.qualys.com/vulnerabilitie…




Team members of 42-b3yond-6ug at USENIX Security. Our topics cover LLM Security, System & Software Attack and Defense. #aixcc




Extremely happy that our paper "Moneta: Ex-Vivo GPU Driver Fuzzing by Recalling In-Vivo Execution States" has been accepted for publication NDSS Symposium 2025. TU Delft DistriNet Yonsei University


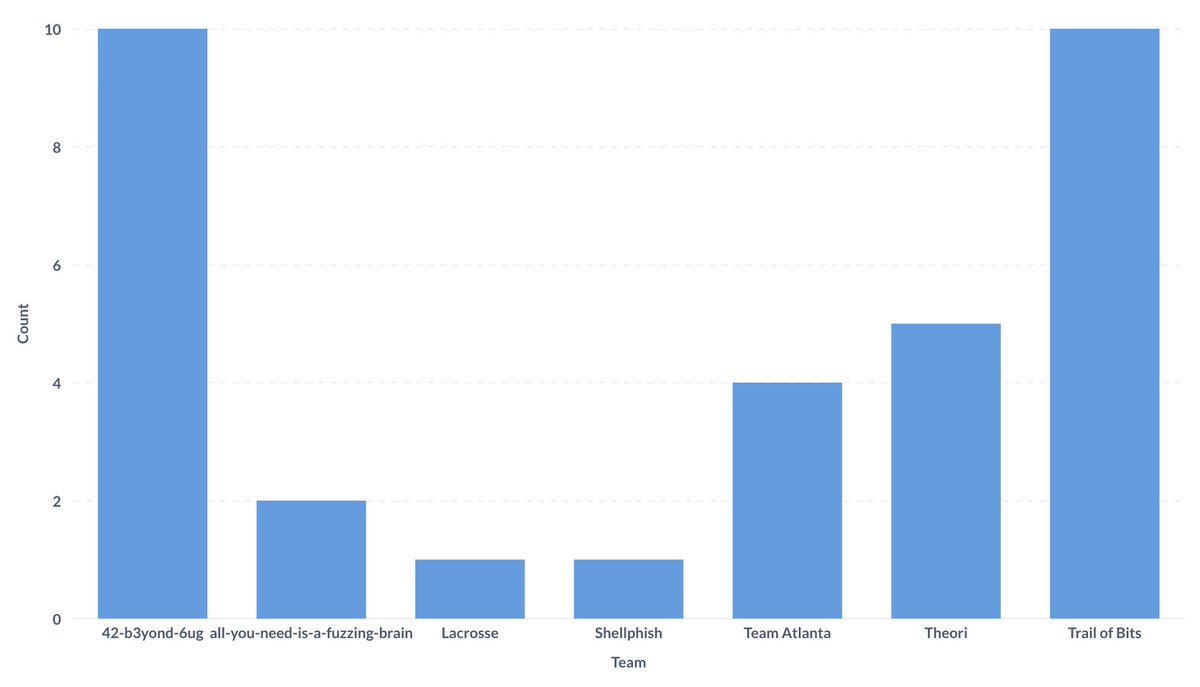
Team 42-b3yond-6ug - led by Northwestern Engineering's Xinyu Xing and Yan Chen - was among the top seven scoring teams at the DARPA and ARPA-H #AIxCC semifinal competition! They will advance to the final competition in August 2025. Congratulations! spr.ly/6012WDs1y







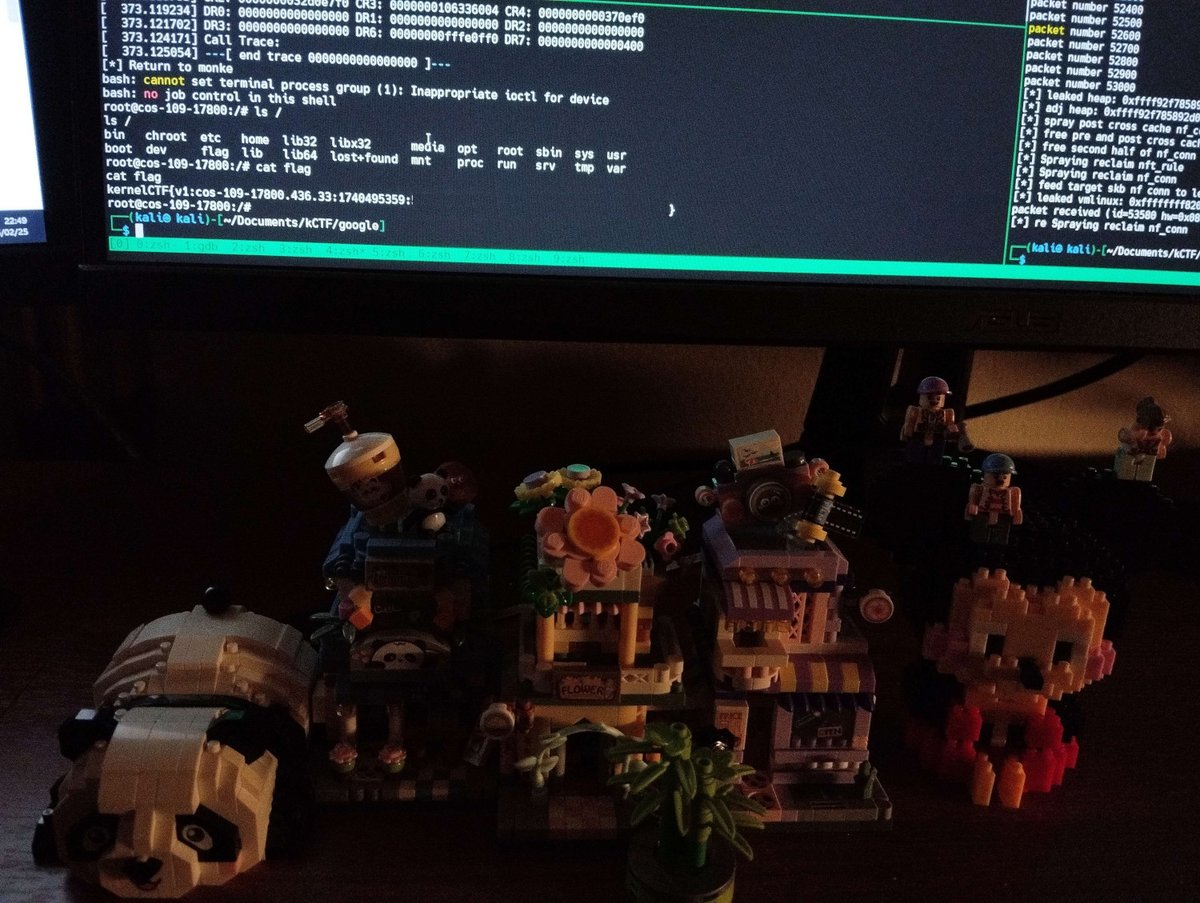
CVE-2023-52927 - Turning a Forgotten Syzkaller Report into kCTF Exploit Article by Hoàng Hải Long 🇻🇳 about finding an unfixed netfilter use-after-free bug reported by syzbot. The researcher exploited it to pwn the kernelCTF COS instance. seadragnol.github.io/posts/CVE-2023…