James T. Bennett
@jtbennettjr
malware analyst, pizza expert
ID: 1713680959
30-08-2013 20:23:55
186 Tweet
821 Takipçi
128 Takip Edilen






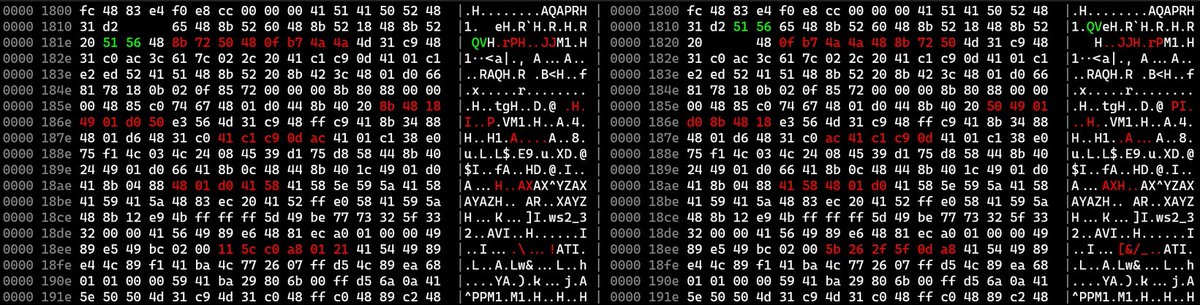
short post introducing `biodiff`, a tool by 8051 enthusiast for diffing binary files, and how you might use it to find malware configuration changes. the UI is really quick and the algorithms handle file alignment very well. williballenthin.com/post/2022-03-0…










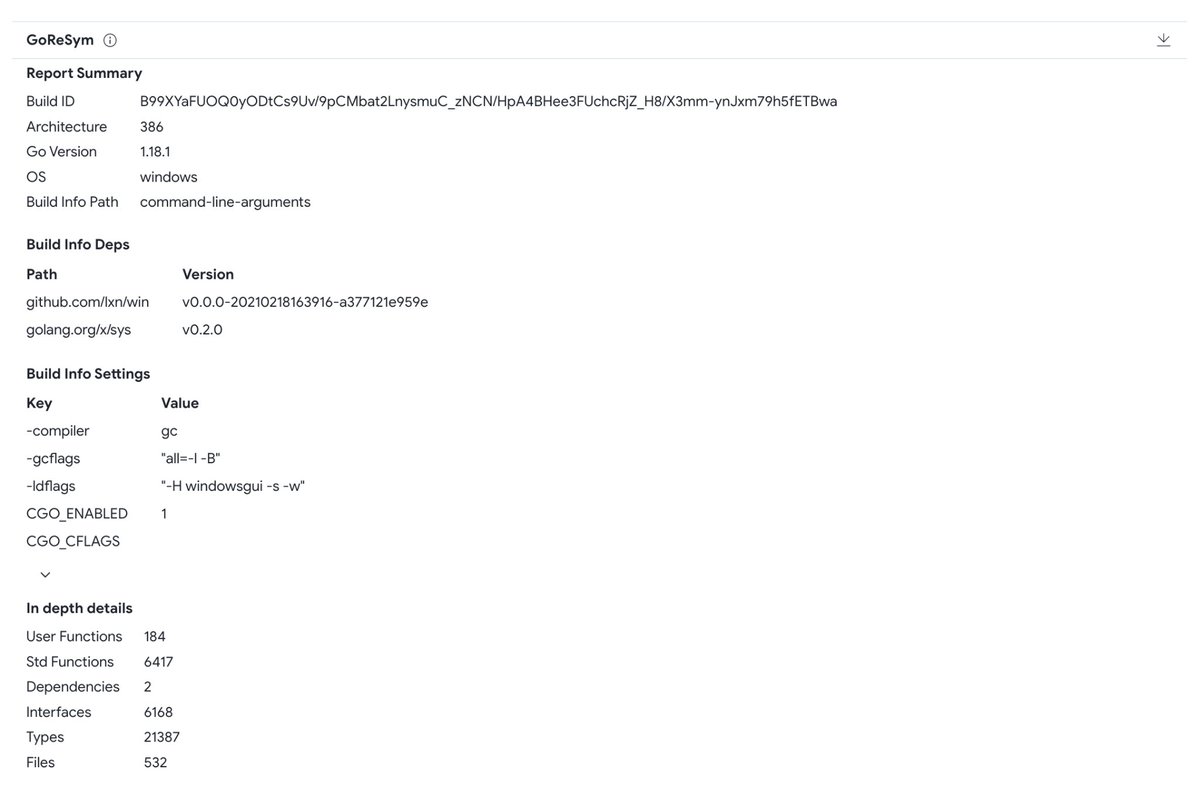
We welcome Mandiant (part of Google Cloud)'s CAPA and GoReSym to our malware analysis suite. CAPA provides valuable TTPs, and GoReSym produces all kind of metadata to analyse GO samples: blog.virustotal.com/2023/01/mandia…