Justin Sherman
@jsherma100
Security reseacher
ID: 1064232000922505216
https://github.com/jsherman212/ 18-11-2018 19:00:56
140 Tweet
3,3K Followers
146 Following






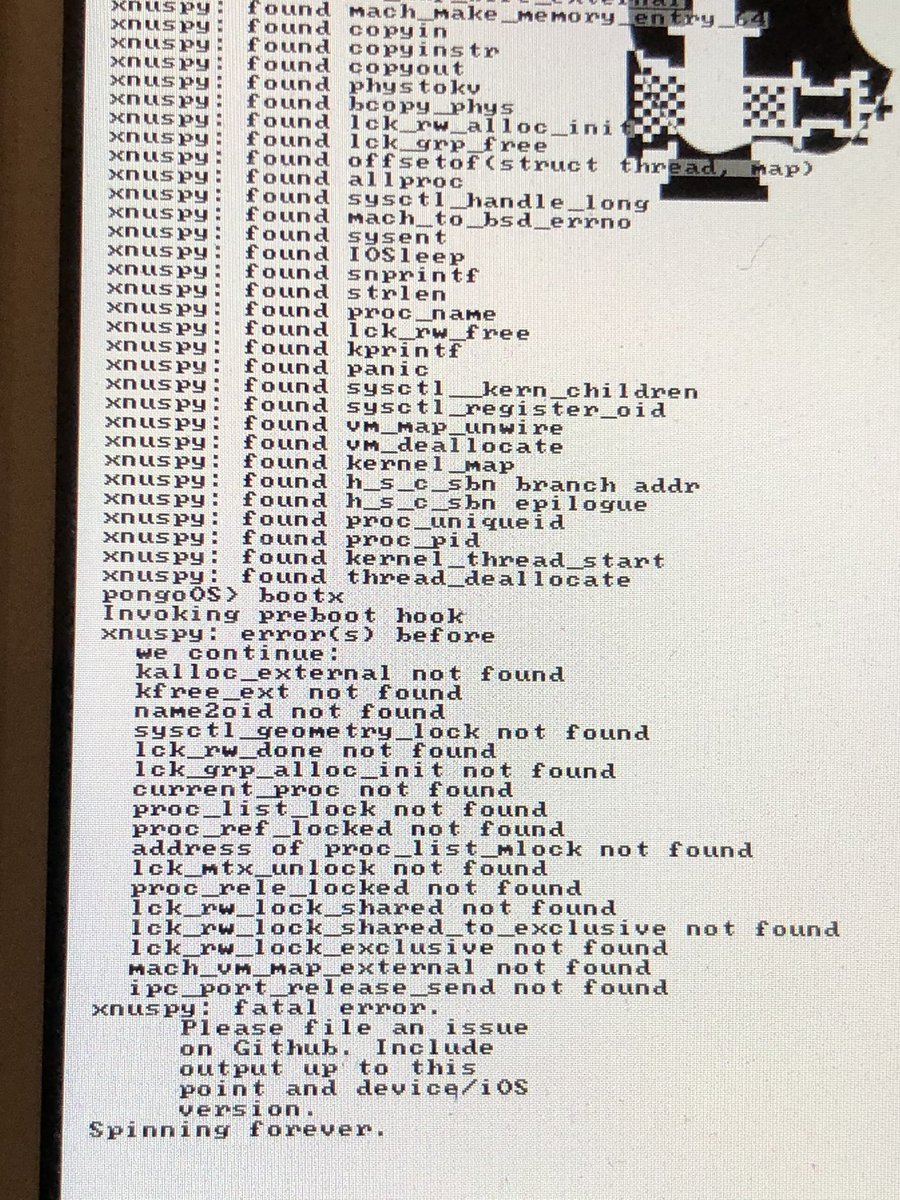
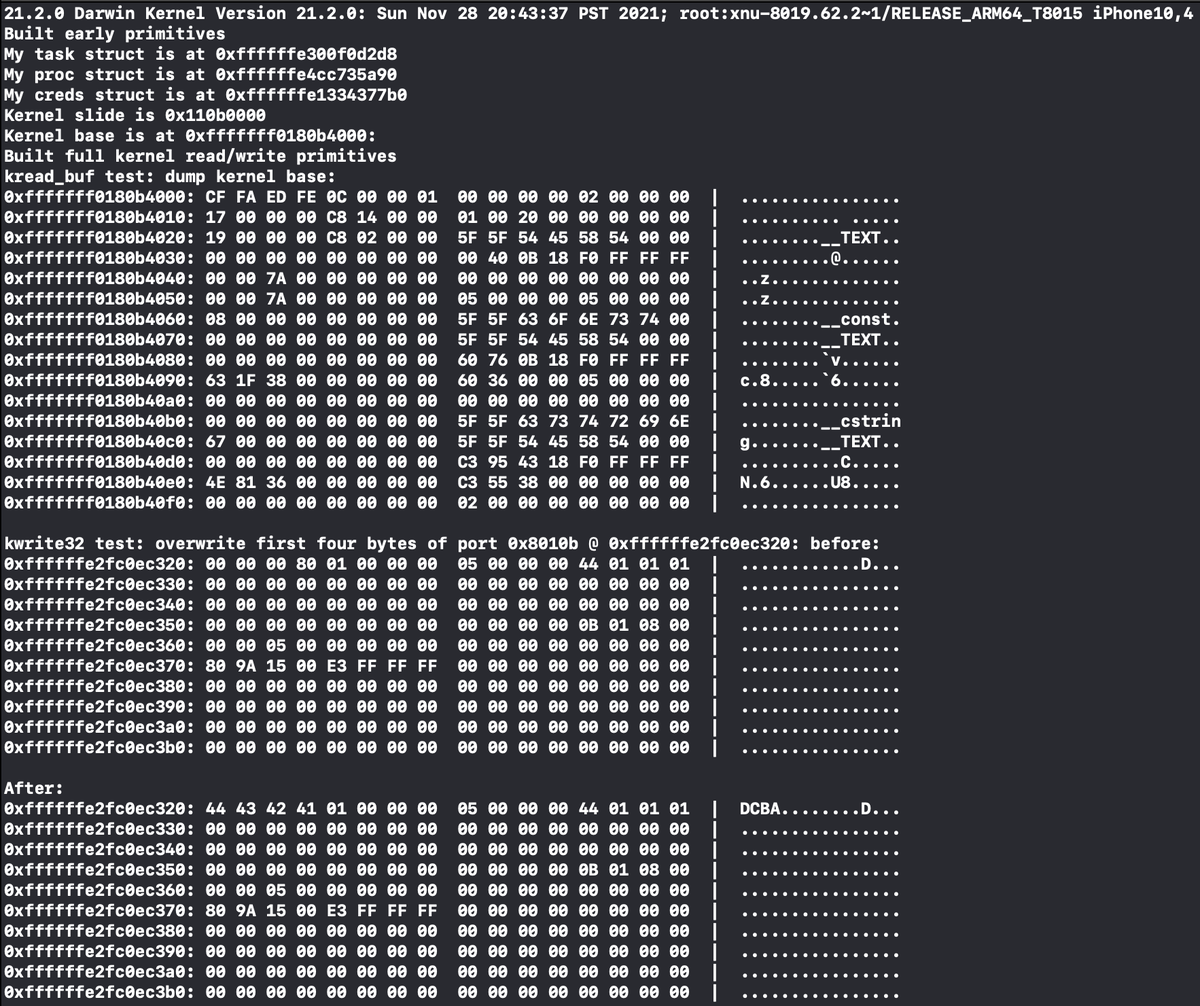
Updated Brandon Azad's KTRW for 14.x and wrote patchfinders for the offsets it needs (aka no more hunting for offsets yourself and putting them in a text file, the pongo module will get them automatically) @ github.com/jsherman212/kt…