Ivan Novikov
@johnnovikov
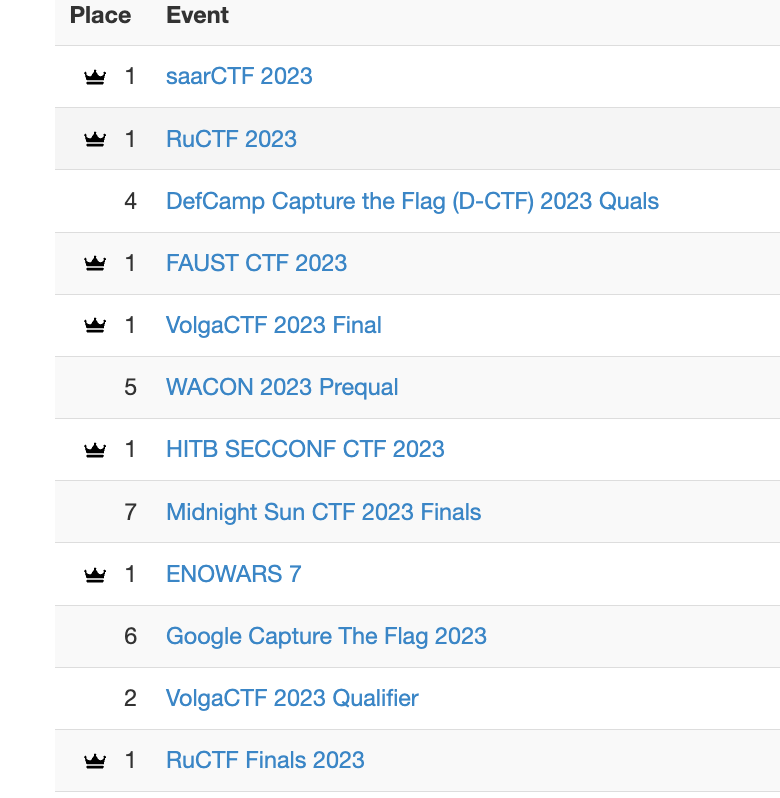
Google SWE, playing CTFs with C4T BuT S4D
ID: 1678177782
17-08-2013 13:14:13
110 Tweet
38 Followers
67 Following





Start your week with a simple #Python sandbox escape challenge from Google CTF: capturetheflag.withgoogle.com/challenges/san… Task is to get the content of file `flag`. The sandbox disallows calling functions on AST level. Attachment is a ZIP file with source. Use nc to connect to that host/port there














Announcing the #TheSAS2025 #CTF winners! Congratulations to C4T BuT S4D for taking the absolute win in the A/D and first-blooding 2 of the 4 services, including the trickiest one. Kudos to SKSD and dtl for their well-deserved 2nd and 3rd places. Every team received a check with a