Padawan
@johnk3r
Threat Hunter
ID: 3032765321
12-02-2015 14:02:33
615 Tweet
1,1K Takipçi
235 Takip Edilen





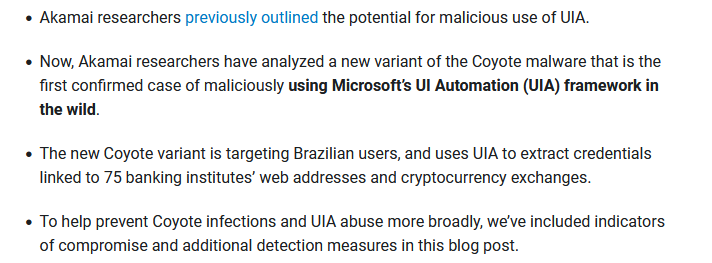
#Malware That Abuses UI Automation More in-depth research on this topic was published today: akamai.com/blog/security-… Akamai Security Intelligence Group Tomer Peled Thanks for the kind mention! Dodo on Security 🇵🇸 🇺🇦 Germán Fernández






Sample recently analyzed is now available on abuse.ch - VT 2/67 bazaar.abuse.ch/sample/360966a… Lukas Stefanko Germán Fernández JAMESWT ESET Research


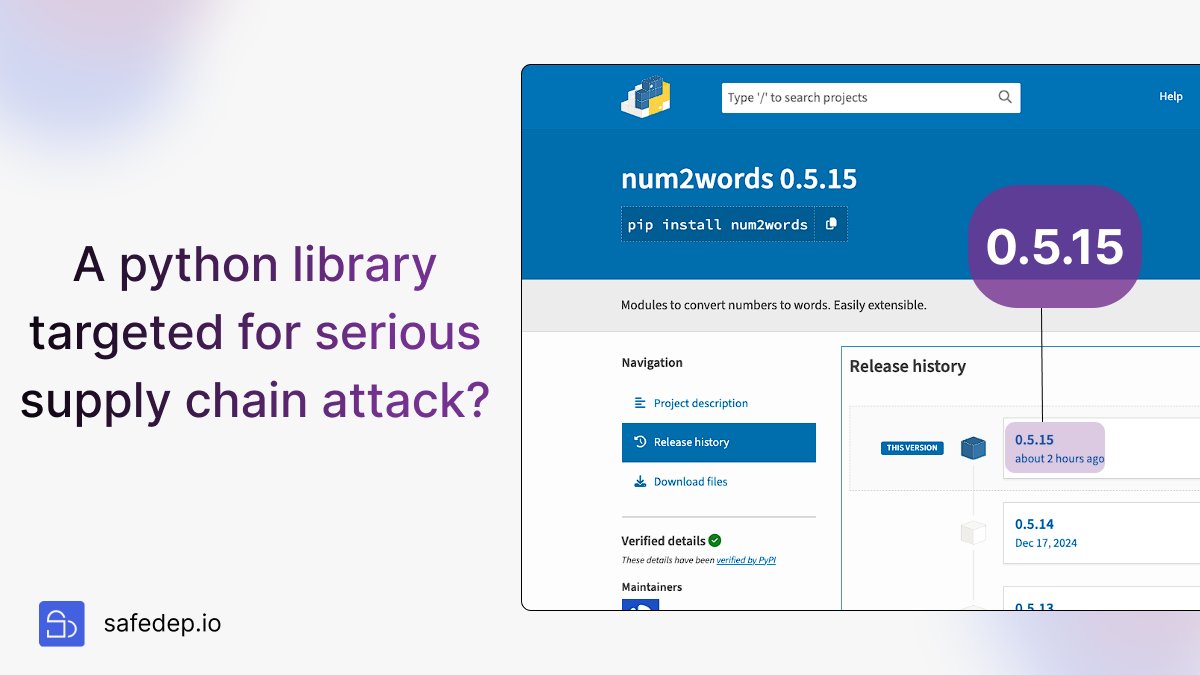
Savoir-faire Linux Padawan Malware Utkonos Invoke RE A new version (0.5.16) was just deployed and it still contains a malicious payload (the same as in 0.5.15). I feel like their sessions are still active despite the password rotation

Tony/Humpty Padawan Malware Utkonos Invoke RE I found a weird token in our pypi account, probably the attacker had created it. I removed the token and deleted the malicious version again (0.5.16). I also created new backup TOTP codes for MFA. Will keep an eye on it but hopefully they won't be able to reupload the malware.


Padawan Malware Utkonos Tony/Humpty Detailed write up invokere.com/posts/2025/07/… Malware Utkonos Padawan




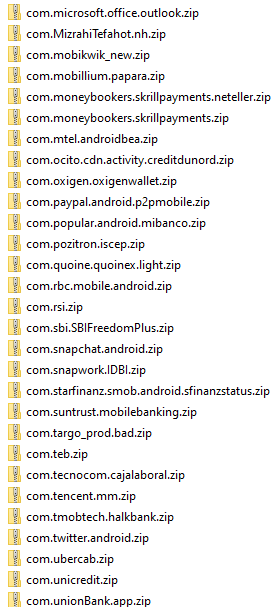
Last observed IoC linked to Brazil-focused Android NFC malware: Domain: brazil-nfc8886-com IP: 43.157.171.245 Package: kqxedi.jpjxke.dxzuzy bazaar.abuse.ch/sample/21c66fe… Mikhail Kasimov