Lukas Stefanko
@LukasStefanko
Malware Researcher at @ESET
Android security, malware analysis, app vulnerability research
https://t.co/dnQvb9BCZj
https://t.co/7RLveZTSoz
ID:2936786110
http://welivesecurity.com/author/lstefanko 22-12-2014 10:23:40
3,3K Tweets
23,8K Followers
697 Following

#ESETresearch has discovered an active #Android #espionage campaign targeting users mainly in 🇮🇳India and 🇵🇰Pakistan with apps bundled with the XploitSPY malware posing mostly as messaging services. We named this campaign eXotic Visit. Lukas Stefanko welivesecurity.com/en/eset-resear… 1/6

#VajraSpy #Patchwork of espionage apps by Lukas Stefanko from ESET Research
•leveraged #GooglePlay to distribute apps with #RAT code
•apps reached 1,400+ installs & are still available on alternative app stores
welivesecurity.com/en/eset-resear…
#Malware #Research #AndySvints #InfoSec


VajraSpy: A Patchwork of espionage apps
#MobileSecurity #AndroidSecurity by WeLiveSecurity Lukas Stefanko
welivesecurity.com/en/eset-resear…


#ESET researchers have discovered twelve #Android apps containing #VajraSpy RAT used by the #Patchwork APT group. Six of these apps had previously been available on #Google Play; together they reached over 1,400 installs. Lukas Stefanko welivesecurity.com/en/eset-resear… 1/5

PoC to takeover Android using another Android by exploiting critical Bluetooth vulnerability to install #Metasploit payload without proper Bluetooth pairing (CVE-2023-45866)
It still affects Android 10 and bellow
mobile-hacker.com/2024/01/23/exp…
#NetHunter

#ESETResearch has observed an alarming growth of deceptive Android loan apps offering personal loans designed to defraud users and gain their personal information. Many of these apps found their way to official marketplaces.
Lukas Stefanko welivesecurity.com/en/eset-resear… 1/8

#ESETResearch has identified a watering-hole attack on the HUNZA NEWS® website, where we discovered a malicious #Android app containing #spyware we named #Kamran . The site focuses on #GilgitBaltistan , a region administered by 🇵🇰 Pakistan. Lukas Stefanko welivesecurity.com/en/eset-resear… 1/5


Well, he got me 🥲 should've pushed for the 🧹 instead 😅
Wizard prodigy Harry Potter ⚡️ joins the show to talk Qakbot, Android BadBazaar espionage, UK air traffic control meltdown, and much more!
Shoutout to the FBI and U.S. Department of Justice for obliterating Qakbot, Zscaler ThreatLabz for…

Trojanized Signal, Telegram apps found on Google Play, Samsung Galaxy Store - helpnetsecurity.com/2023/08/31/fak… - ESET Lukas Stefanko #signal #telegraph #malware #android #MaliciousApps #cybersecurity #netsec #security #InfoSecurity #CISO #ITsecurity #CybersecurityNews #SecurityNews


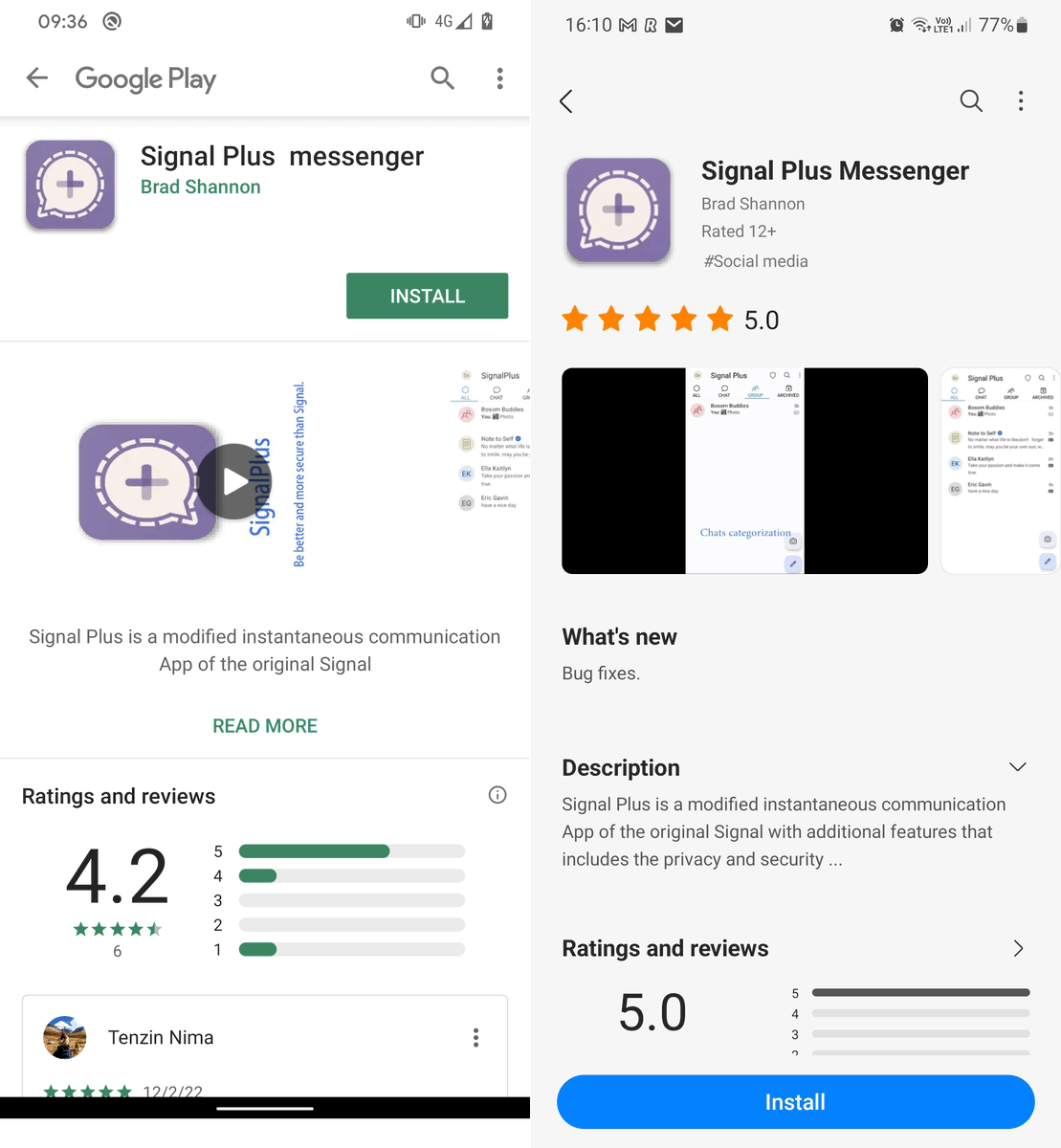
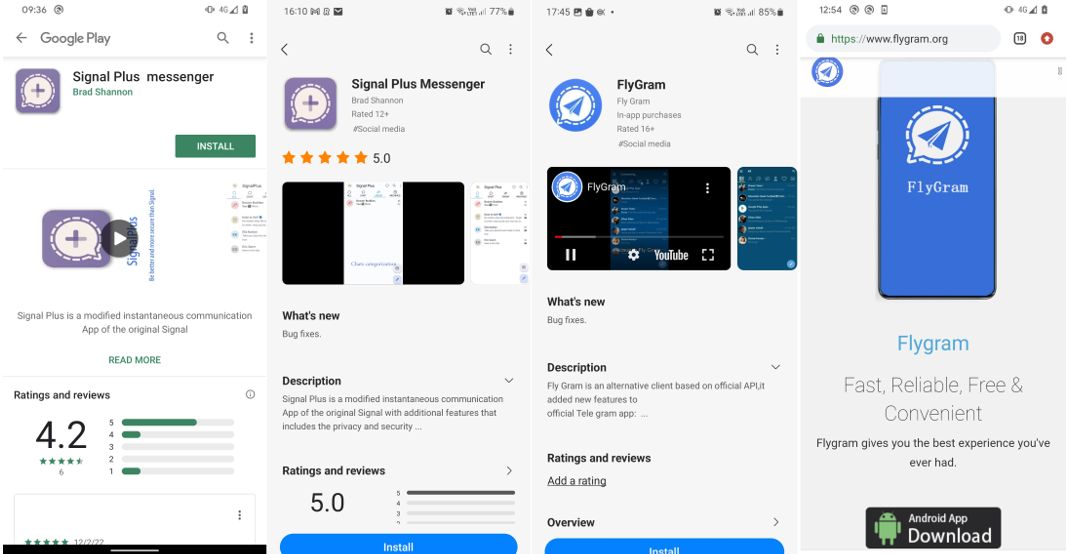
Trojanized #Signal Android app available on Google Play and Galaxy Store could secretly autolink Signal account of victim to attacker Desktop without noticing.
This would allow attacker to have a full Signal account control of the victim without notice
welivesecurity.com/en/eset-resear…

NEW - A fake Signal app popped up on Google Play using a previously-undocumented method to spy on the encrypted comms tool.
The hackers are linked to China and previous hits on the Uyghur community.
There was a fake Telegram too...
h/t Lukas Stefanko
forbes.com/sites/thomasbr…

#ESETresearch identified two GREF campaigns targeting #Android users with Signal and Telegram Messenger apps trojanized into cyberespionage tools .
Lukas Stefanko
welivesecurity.com/en/eset-resear…
1/9


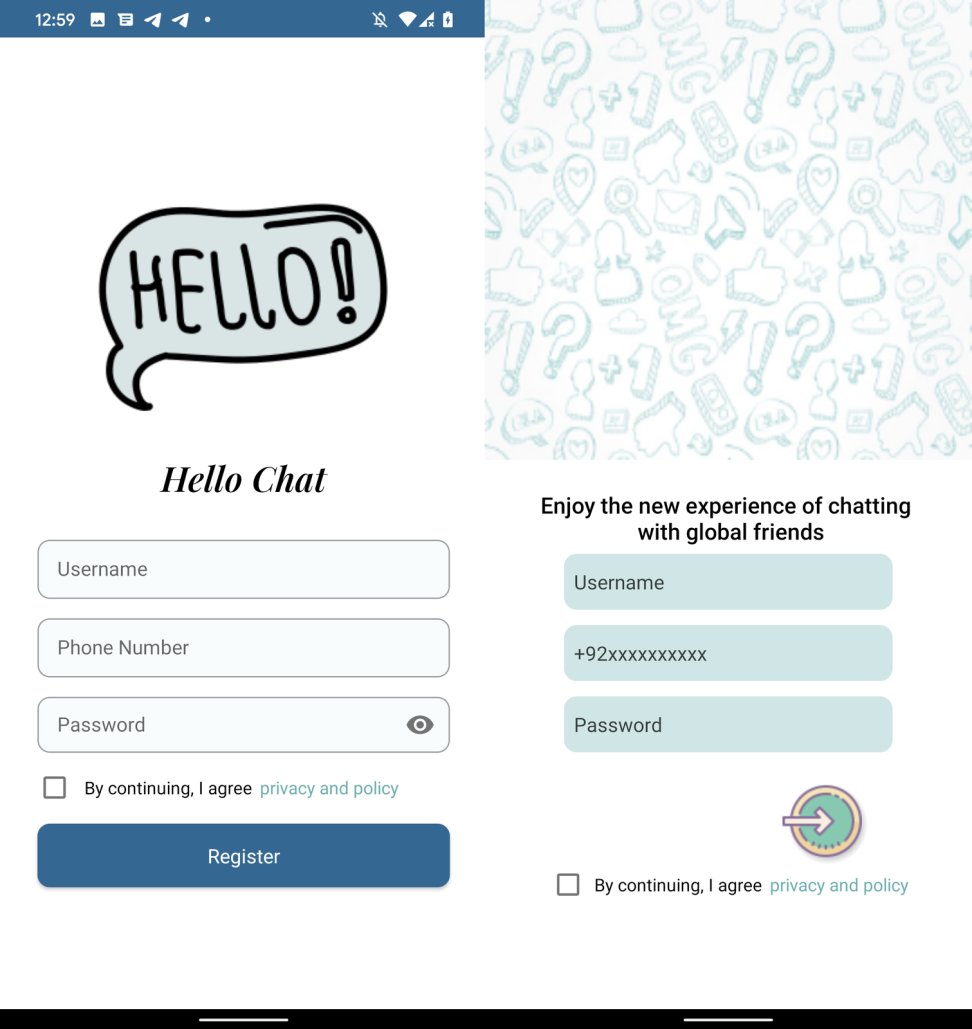
#ESETResearch identified #Android #GravityRAT malware being distributed as the #BingeChat and Chatico messaging apps. The BingeChat campaign is still active as of this writing. Lukas Stefanko
welivesecurity.com/2023/06/15/and… 1/5