Jonathan Creasy 🧢
@johann8384
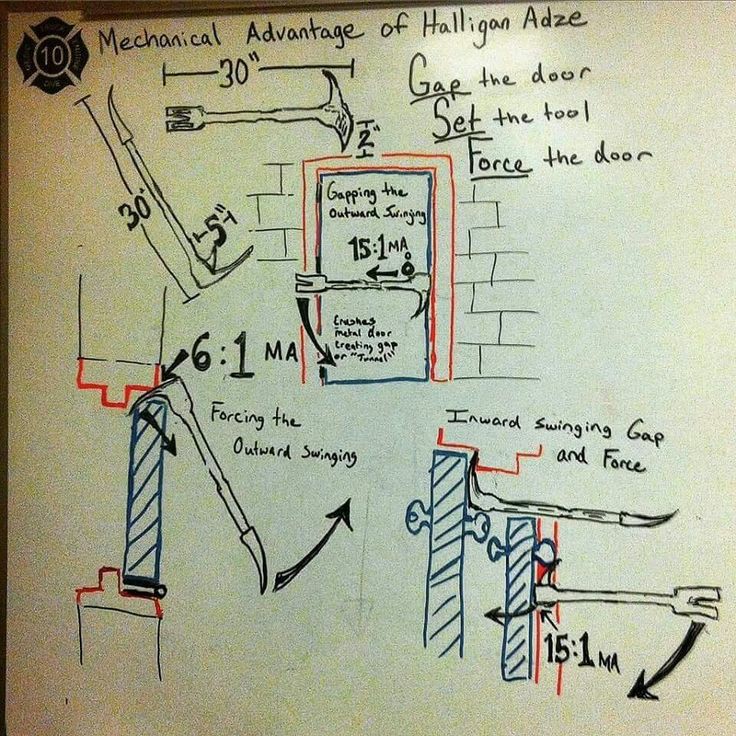
Loves technology and data, volunteer firefighter. Machine Learning at Cisco, Disaster Relief with ITDRC, KC9FQT, Oldham County KY ARES EC
ID: 118937716
http://www.ghostlab.net 02-03-2010 04:44:52
5,5K Tweet
336 Takipçi
1,1K Takip Edilen



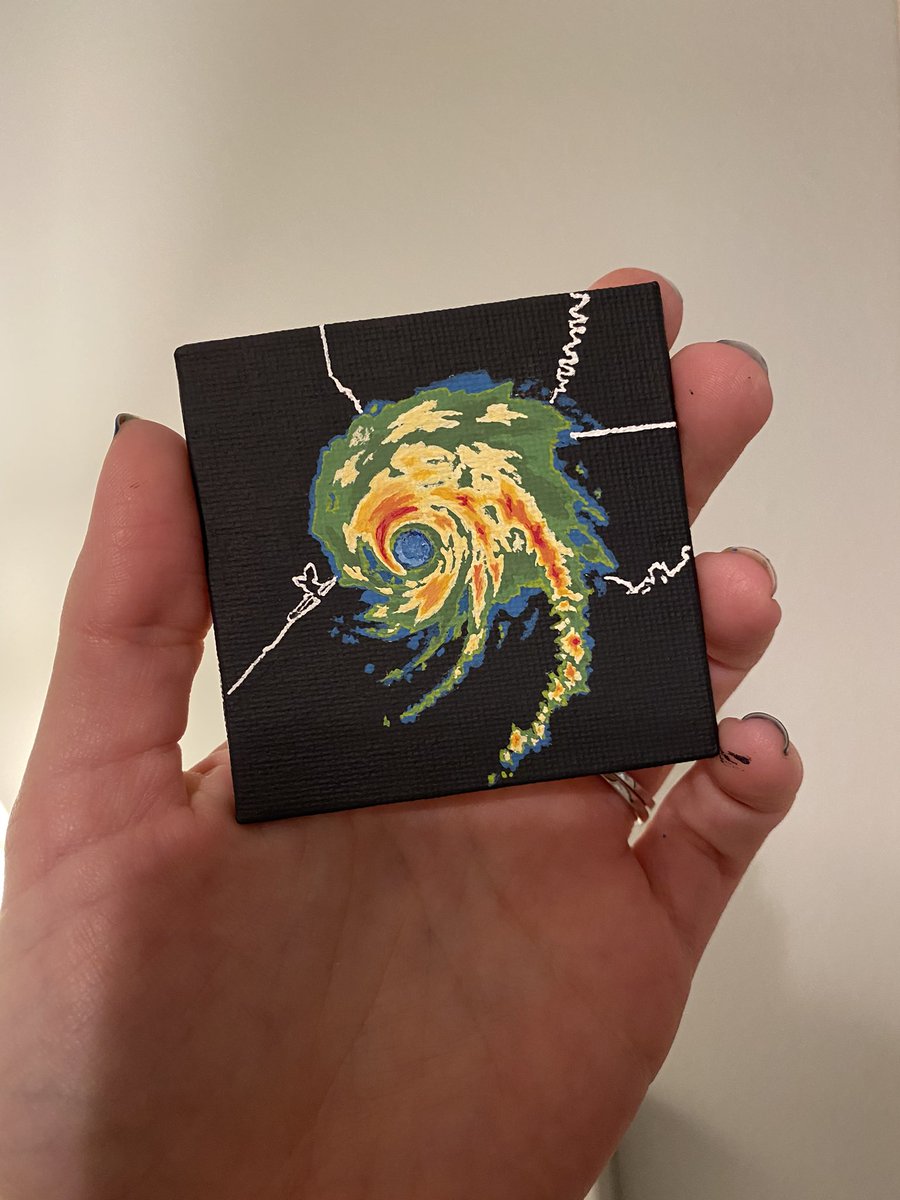
In Kentucky, our teams responded to a request from KY State Police to provide connectivity to local gas stations who were unable to process credit card transactions after the #MayfieldTornado #CommIsAid