
Mohammed Sami
@jizen0x01
Offensive Security | Malware Research | AI/ML
ID: 1181267218514026499
http://jizen0x01.github.io 07-10-2019 17:57:26
67 Tweet
228 Followers
1,1K Following








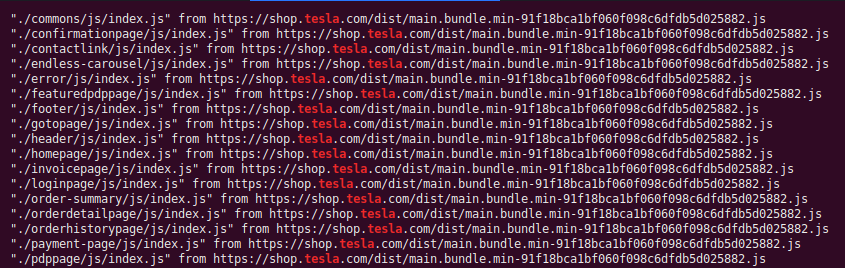
subfinder -d tesla.com -silent | httpx -timeout 3 -threads 300 --follow-redirects -silent | xargs -I% -P10 sh -c 'hakrawler -plain -linkfinder -depth 5 -url %' | grep "tesla" @b51b5b43 Luke Stephens (hakluke) JS0N Haddix STÖK ✌️ ProjectDiscovery #bugbountytip #bugbounty


Extract URL .apk 💀 🔥 apktool d com.uber -o uberApk;grep -Phro "(https?://)[\w\.-/]+[\"'\`]" uberApk/ | sed 's#"##g' | anew | grep -v "w3\|android\|github\|schemas.android\|google\|goo.gl" 🔥 @b51b5b43 STÖK ✌️ JS0N Haddix Ben Sadeghipour TomNomNom
![👑 OFJAAAH 👑 (@ofjaaah) on Twitter photo Extract URL .apk 💀
🔥 apktool d com.uber -o uberApk;grep -Phro "(https?://)[\w\.-/]+[\"'\`]" uberApk/ | sed 's#"##g' | anew | grep -v "w3\|android\|github\|schemas.android\|google\|goo.gl" 🔥
@b51b5b43 <a href="/stokfredrik/">STÖK ✌️</a> <a href="/Jhaddix/">JS0N Haddix</a> <a href="/NahamSec/">Ben Sadeghipour</a> <a href="/TomNomNom/">TomNomNom</a> Extract URL .apk 💀
🔥 apktool d com.uber -o uberApk;grep -Phro "(https?://)[\w\.-/]+[\"'\`]" uberApk/ | sed 's#"##g' | anew | grep -v "w3\|android\|github\|schemas.android\|google\|goo.gl" 🔥
@b51b5b43 <a href="/stokfredrik/">STÖK ✌️</a> <a href="/Jhaddix/">JS0N Haddix</a> <a href="/NahamSec/">Ben Sadeghipour</a> <a href="/TomNomNom/">TomNomNom</a>](https://pbs.twimg.com/media/EgjE2_lXgAAUBHB.jpg)







Giveaway time! We are going to send a t-shirt and few goodies to one person who follows PentesterLab and likes this tweet !! And we are going to give a 1-year voucher to someone who RT this tweet!

![👑 OFJAAAH 👑 (@ofjaaah) on Twitter photo ./github-subdomains.py -t APIKEY -d att.com | httpx -silent | xargs -I@ -P20 sh -c 'gospider -a -s "@" -d 2' | grep -Eo "(http|https)://[^/\"].*.js+" | sed "s#\] \- #\n#g" | anew | grep "att.com"
github.com/gwen001/github…
@b51b5b43 <a href="/stokfredrik/">STÖK ✌️</a> ./github-subdomains.py -t APIKEY -d att.com | httpx -silent | xargs -I@ -P20 sh -c 'gospider -a -s "@" -d 2' | grep -Eo "(http|https)://[^/\"].*.js+" | sed "s#\] \- #\n#g" | anew | grep "att.com"
github.com/gwen001/github…
@b51b5b43 <a href="/stokfredrik/">STÖK ✌️</a>](https://pbs.twimg.com/media/EgRzmv8X0AMkSja.png)

