Jan Holman
@jenykholman
Malware Researcher at Eset
ID: 401003248
29-10-2011 22:15:54
50 Tweet
59 Takipçi
390 Takip Edilen




Každoroční #LockedShields, kybernetické cvičení organizované NATO CCDCOE dnes ráno odstartovalo. Český tým ve složení #NUKIB a našich partnerských organizací se ho již tradičně účastní.









New #APT research on the Decoded blog: Operation Dragon Castling, a campaign targeting betting companies in Taiwan, the Philippines & Hong Kong. Analysis by Jan Holman @n3ph8t3r & Igor Morgenstern. Read, enjoy and share decoded.avast.io/luigicamastra/…

Read this intriguing story of a suspected #APT #MustangPanda collecting data from the #Burmese government, written by Avast Threat Labs team read enjoy and share: decoded.avast.io/threatintel/ap…


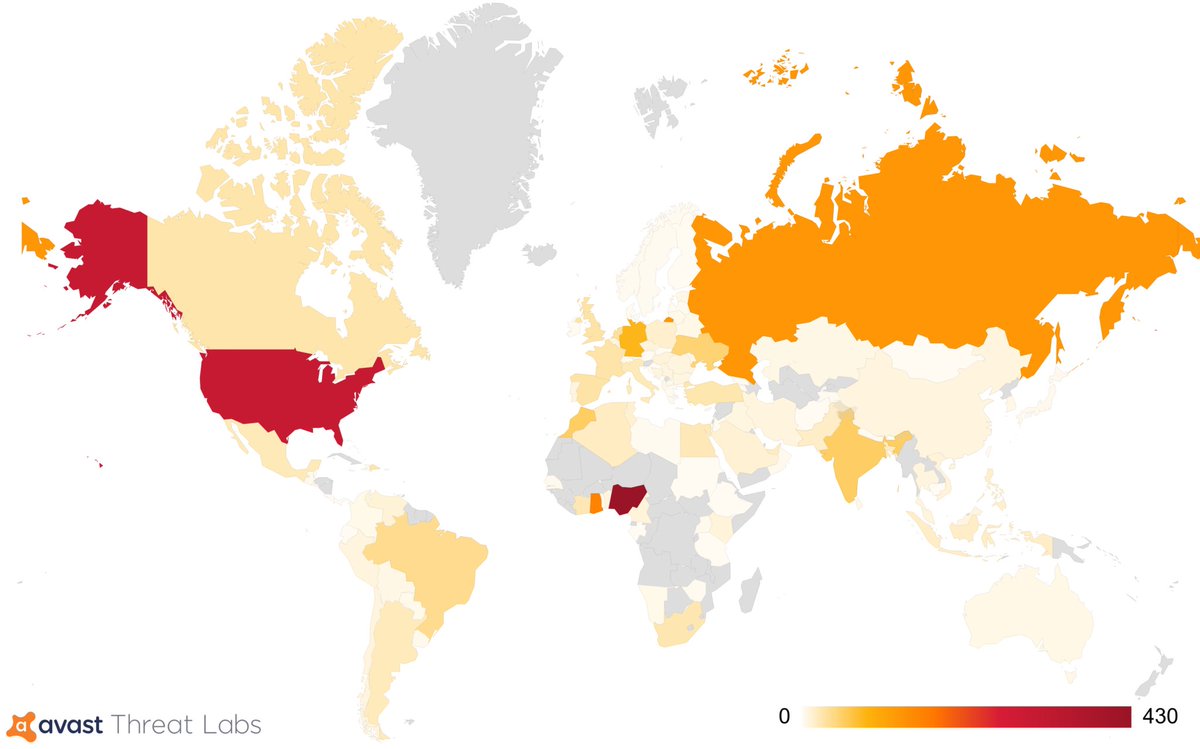
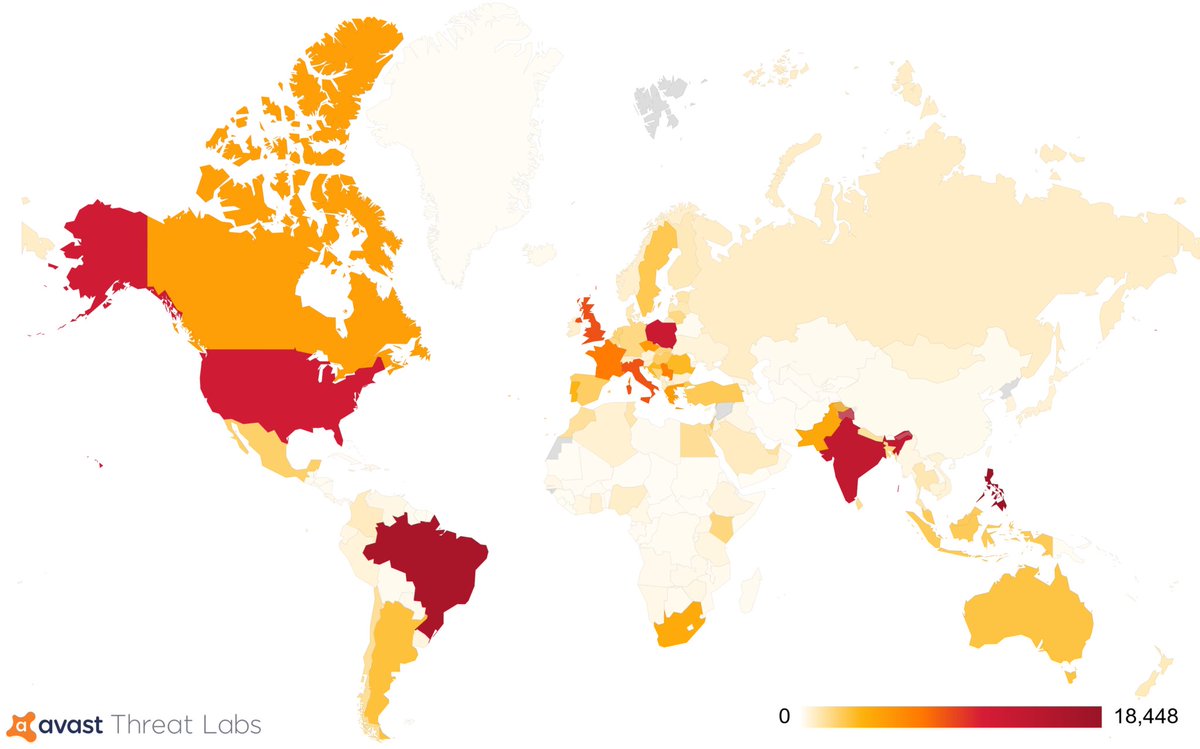
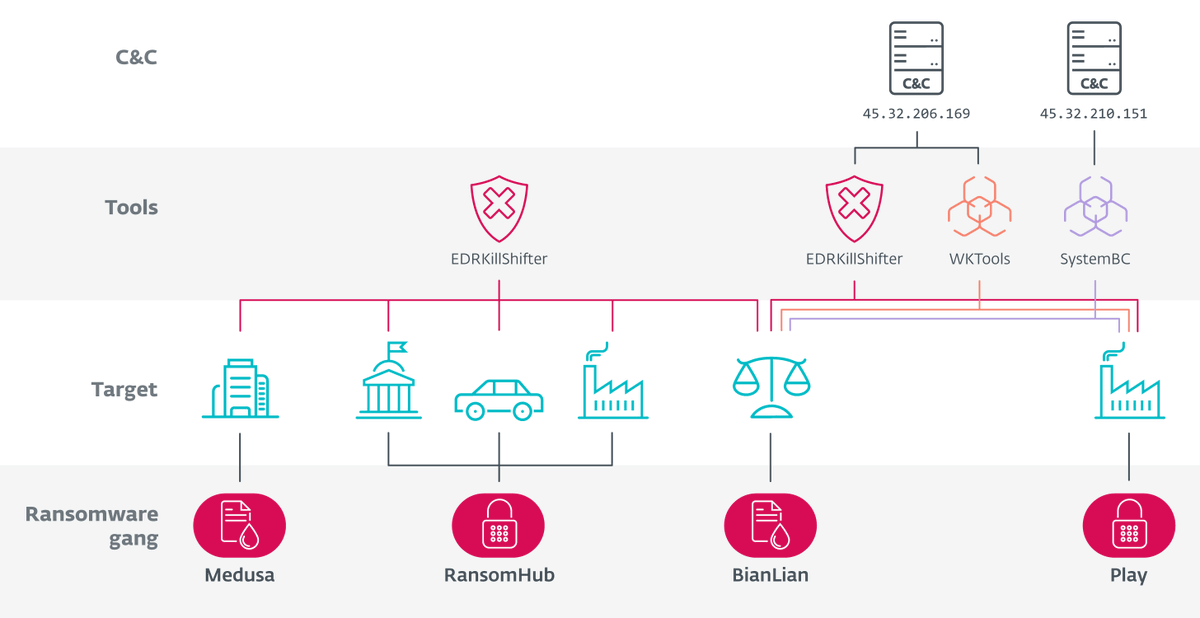
#ESETresearch discovered previously unknown links between the #RansomHub, #Medusa, #BianLian, and #Play ransomware gangs, and leveraged #EDRKillShifter to learn more about RansomHub’s affiliates. Jakub Souček welivesecurity.com/en/eset-resear… 1/7



#LockedShields2018 = altogether 4000 virtualised systems, more than 2500 attacks underway + strategic, legal, media, digital forensics tasks NATO CCDCOE flagship exercise is more challenging & complex than ever. First captures from the control room in Tallinn: flickr.com/photos/1338008…