jdelta
@jdelta11
ID: 1102372978522800128
04-03-2019 00:59:33
2,2K Tweet
687 Takipçi
259 Takip Edilen










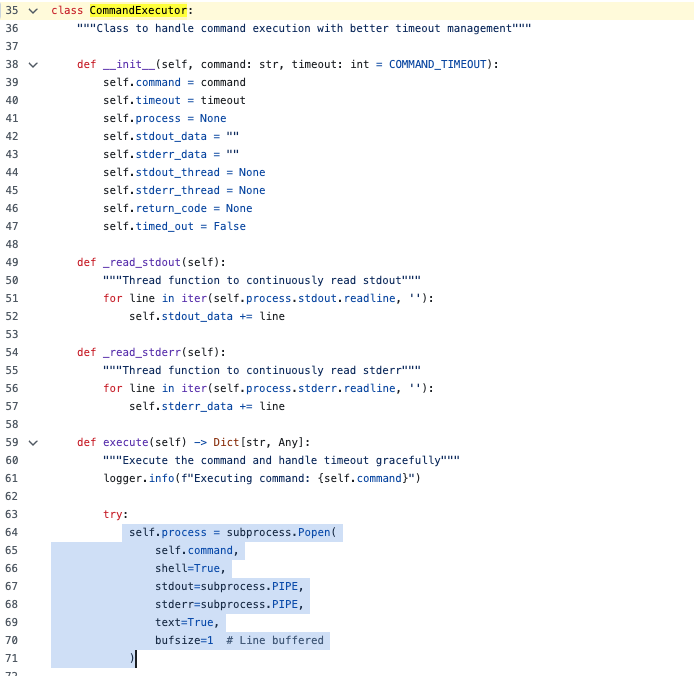
Since I was bored in a plane I decided to revisit some of the Windows Hello tradecraft and finally implemented browser based FIDO2 auth using WHFB keys in roadtx. Thanks Fabian Bader and Nathan McNulty for the inspiration!