jatin budhwar
@jatinbudhwar2
Bug Bounty Hunter
immunefi.com/profile/J10/
ID: 1002469473914376192
01-06-2018 08:38:42
276 Tweet
29 Followers
324 Following











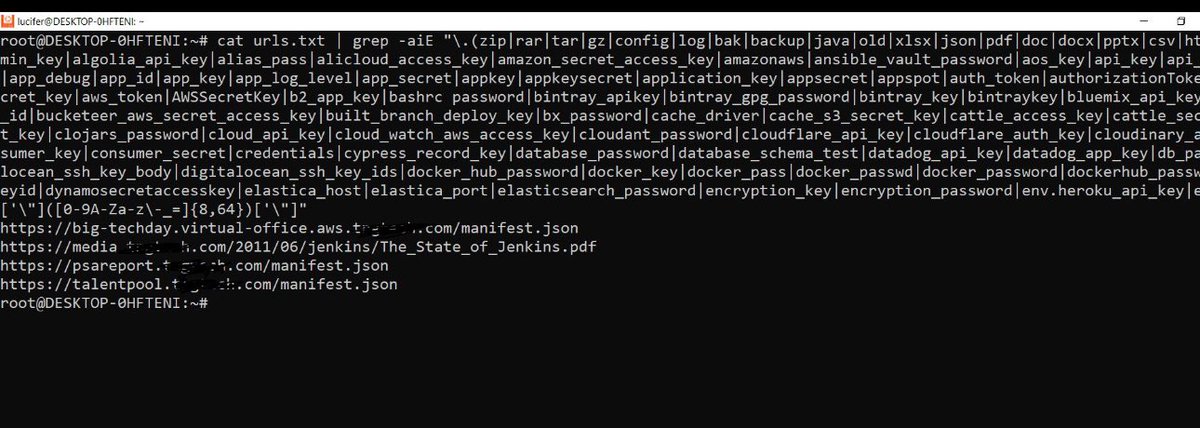
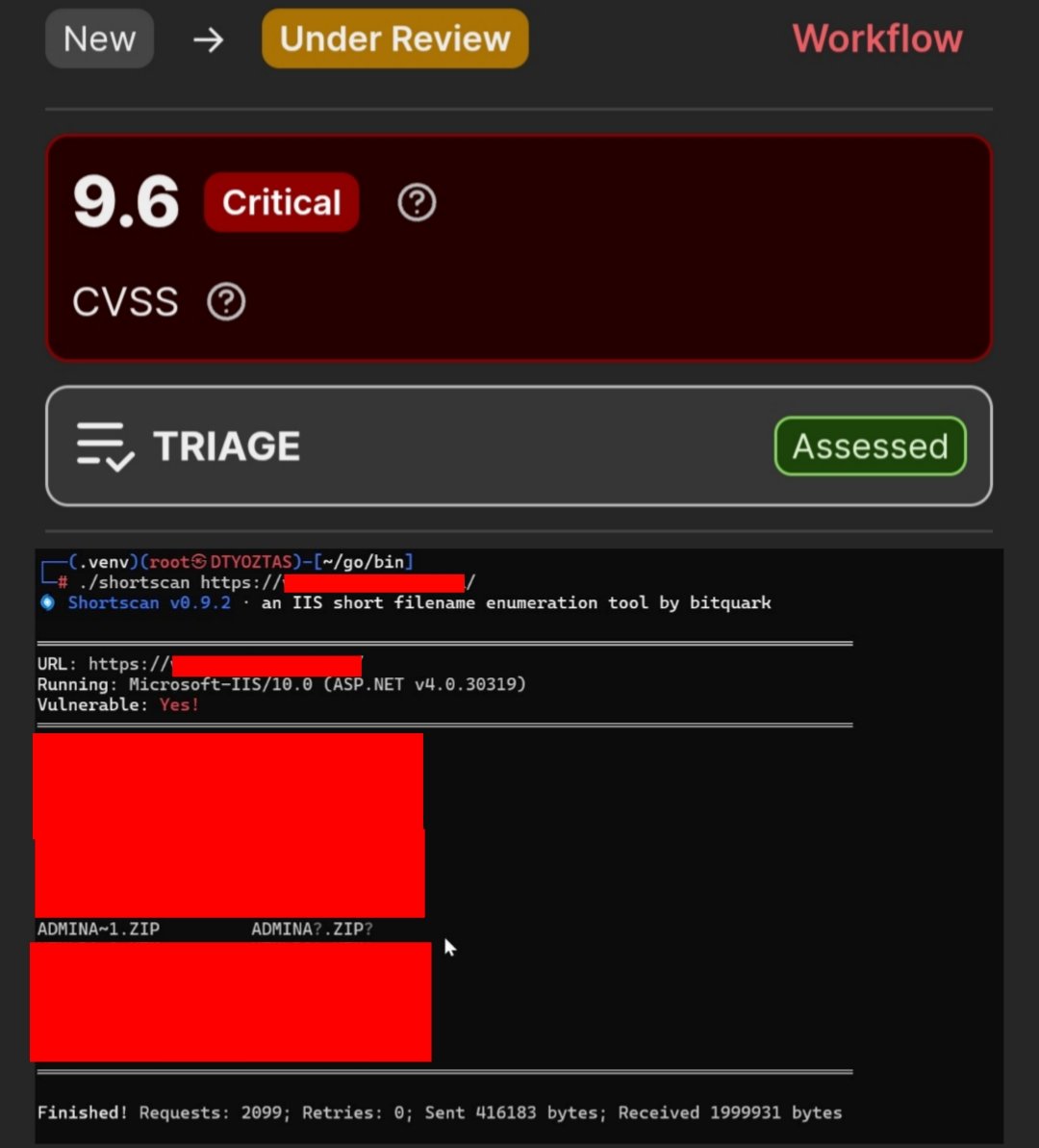
Always delve deeper into your ASN number searches for your goals, sometimes a .zip file changes everything 🥳🌹😊 For Windows IIS fuzzing, I generally use the .../raft-medium-words.txt wordlist. #bugbountytip #bugbountytips #InfoSec #recon YesWeHack ⠵





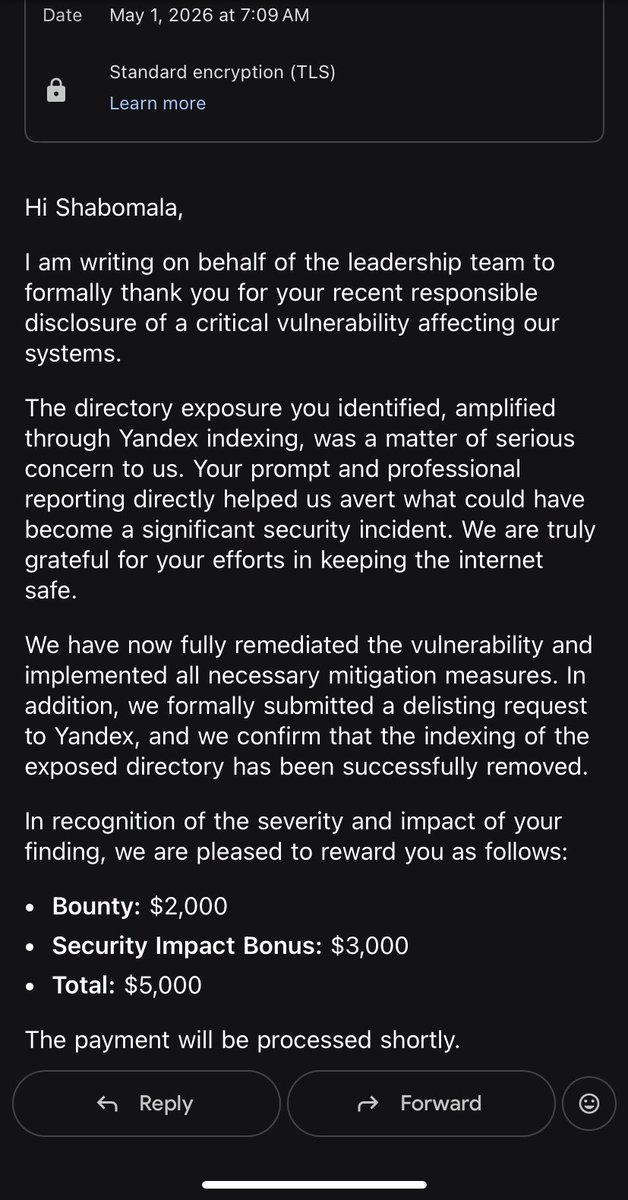
Wow Yandex Dork is Very Crazy 🔥🔥🔥🔥🔥 Glad they write to Yandex to remove there index 🚀🚀🚀 Big up Sachin Pandey for the Yandex dork Simple url: yandex-dork.lovable.app 🔥🔥🔥🔥 so insane Yandex Never Fail 🔥🔥🔥🚀🚀🚀


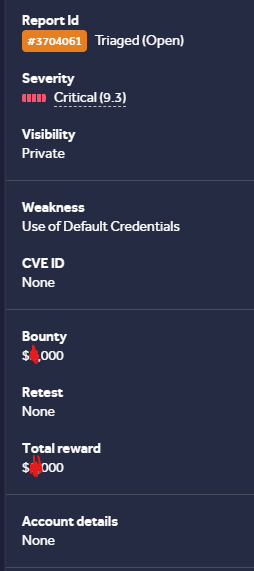
If the admin panel you targeted has a username enumeration , you can brute-force using a wordlist. This has worked many times for me in this case, the username was "admin" My password wordlists: Basic: raw.githubusercontent.com/danielmiessler… Advance: raw.githubusercontent.com/mrtc0/honeylog… Usernames