Sec_Nerd07
@itssecuritynerd
🌍 Grateful
💻 Geek
💪 Fitness freak
ID: 1077596137392164865
https://sahil-security-nerd07.medium.com/ 25-12-2018 16:05:14
1,1K Tweet
283 Takipçi
161 Takip Edilen



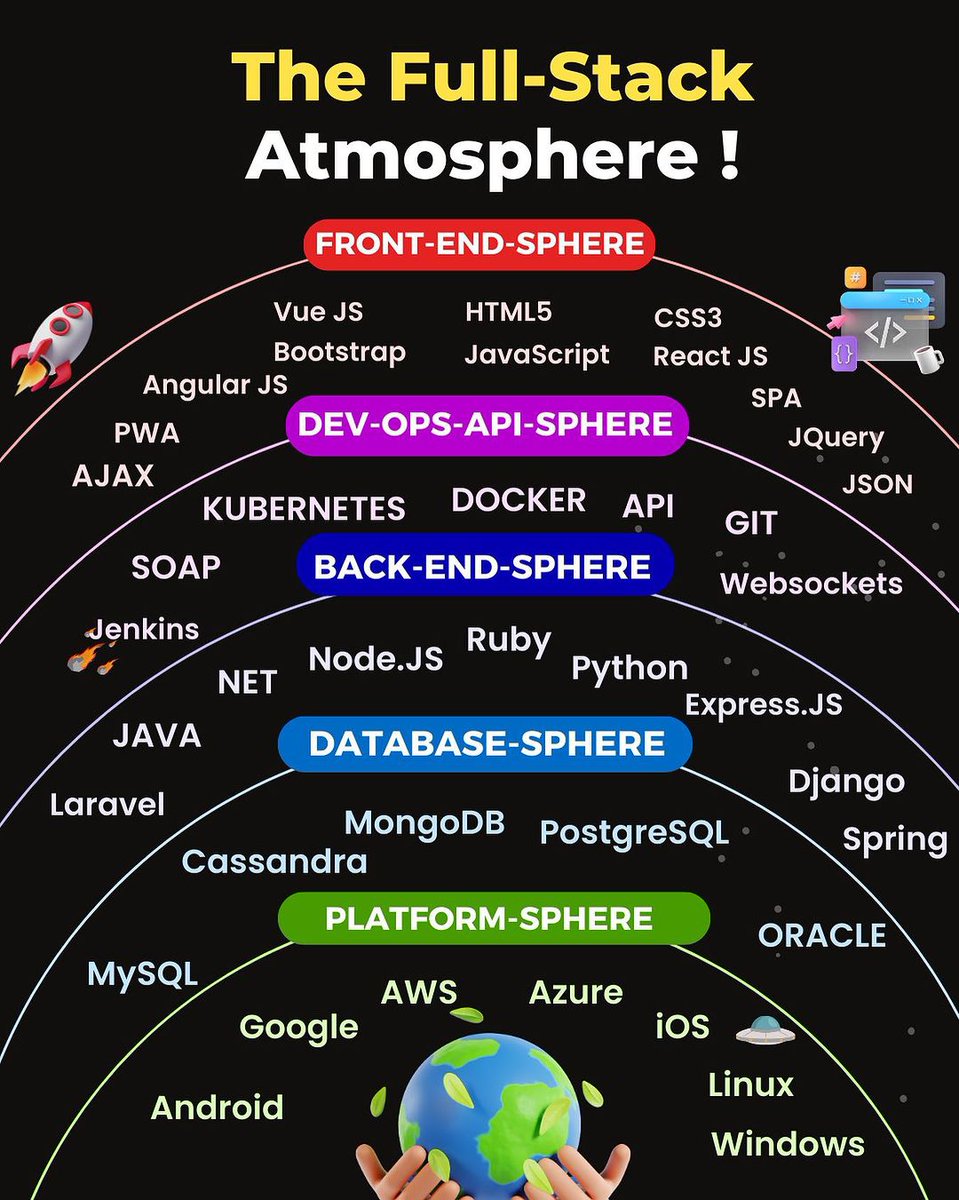
Free Computer Science Certifications to try in 2023: 🔸GIT simplilearn.com/learn-git-basi… 🔸Python mygreatlearning.com/academy/learn-… 🔸SQL cognitiveclass.ai/courses/learn-… 🔸DSA mygreatlearning.com/academy/learn-… 🔸Java openclassrooms.com/en/courses/566… 🔸JavaScript openclassrooms.com/en/courses/566… 🔸C alison.com/course/c-progr…







GAP by / XNL -н4cĸ3r (and @xnl-h4ck3r in the new Sky), is a must-have Burp extension. It parses paths/URLs from JS and pinpoints key params via the sus_params project from Gunnar Andrews and myself. Plus, it generates targeted custom wordlists! 👨💻 github.com/xnl-h4ck3r/GAP… 🎥 youtube.com/watch?v=Os3bN0…

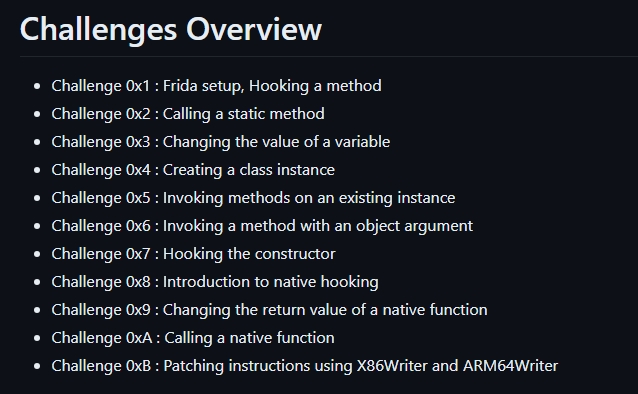
I just wrote a new blog on IOS pentesting after a while. I got this idea when I was stuck for an entire day while setting things up for this assessment. I noticed a lot has changed in this landscape. sahil-security-nerd07.medium.com/getting-starte… #CyberSecurity #Pentesting #IOSpentesting



In case you missed Godfather Orwa 🇯🇴's Recon video, here you go. 🫡 Gain that knowledge: youtube.com/watch?si=RDw88…