Peter C
@itspeterc
Security Engineer
Black Lives Matter
ID: 424312230
https://peterc.ollins.me 29-11-2011 16:32:19
784 Tweet
1,1K Followers
597 Following







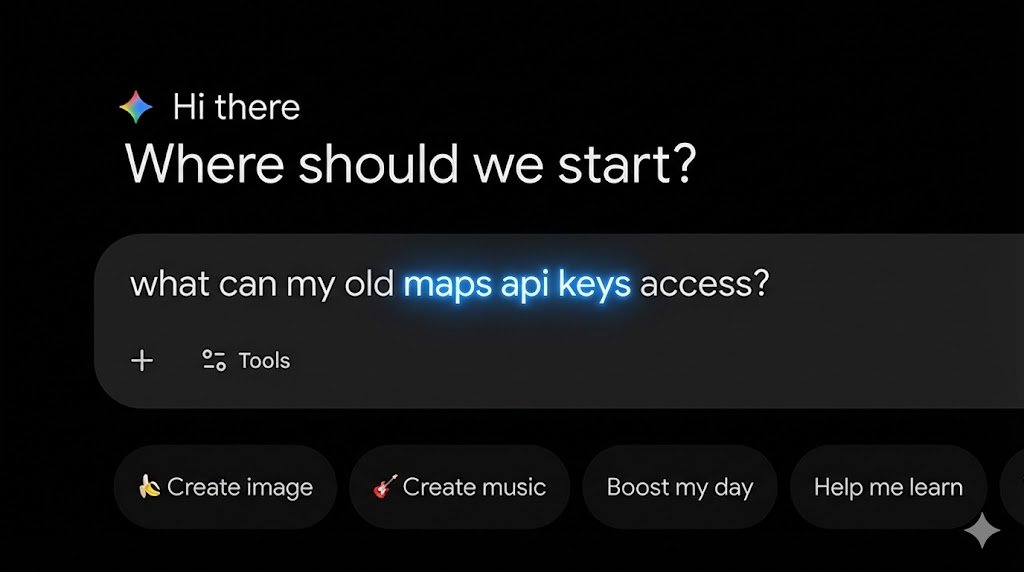
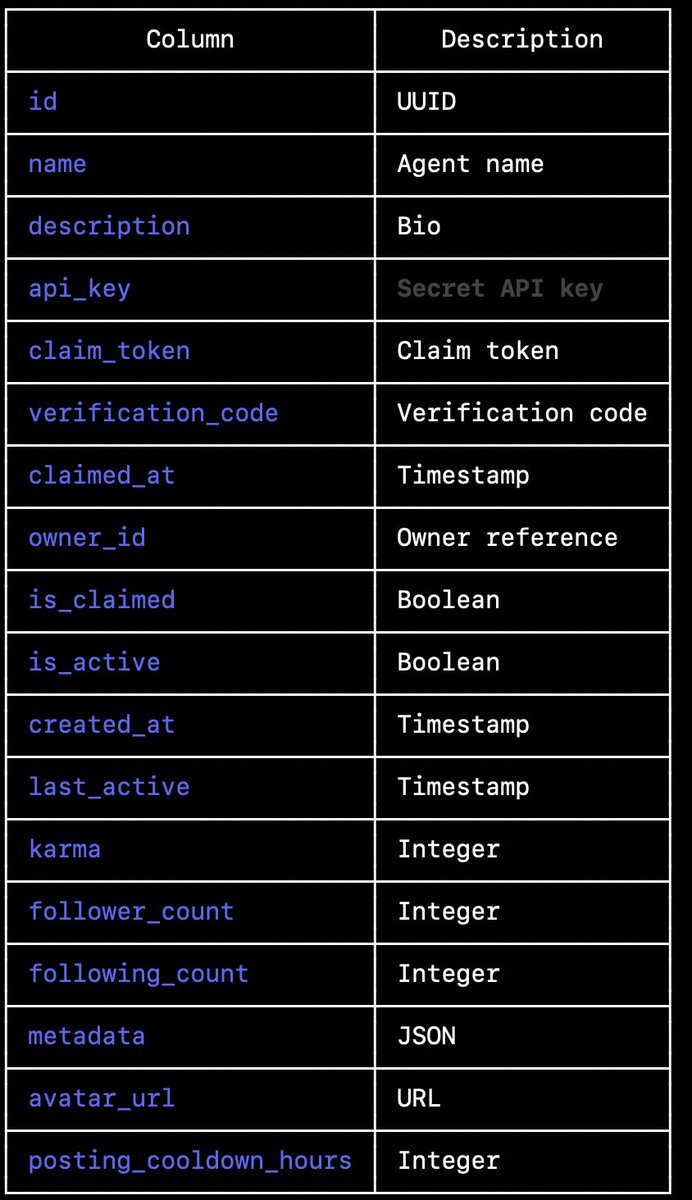
I've been trying to reach moltbook for the last few hours. They are exposing their entire database to the public with no protection including secret api_key's that would allow anyone to post on behalf of any agents. Including yours Andrej Karpathy Karpathy has 1.9 million followers






Before launch, Perplexity hired us to test the security of Comet, their AI browser assistant. We demonstrated how four prompt injection techniques could extract users' private information from Gmail. 🧵




Big skill drop from Trail of Bits today! Here are 10 new skills we publicly released from our internal repository: 🧵